The cybersecurity M&A landscape just hit a fascinating inflection point. With Zscaler’s acquisition of SPLX yesterday, we’ve now witnessed ten major acquisitions in the “Security for AI Applications” category since August 2024. Meanwhile, the “AI for Security Operations” bucket? A big fat zero.
This isn’t random. This is a market signal screaming at us about where the real money, real urgency, and real innovation budgets are flowing in 2025.
The Acquisition Frenzy: A Timeline
This latest wave of AI security acquisitions represents a fascinating subset of the broader cybersecurity consolidation trend we’ve been tracking, which has seen over 800 M&A deals and $167+ billion in disclosed transaction values from 2023-2025. But what makes this AI security surge unique is the speed and focus—thirteen acquisitions in just 15 months, all targeting a brand new attack surface.
The deal that started it all: Cisco’s acquisition of Robust Intelligence wasn’t just the first major “Security for AI” deal—it was the market signal that changed everything. When Cisco, fresh off its massive $28 billion Splunk acquisition, turned around and dropped a reported $400 million on a relatively young AI security startup in August 2024, it sent a clear message: AI security is a distinct category worth building (or buying) into.
Let’s look at what just happened in rapid succession:
-
Cisco → Robust Intelligence (August 2024, completed September 24, 2024) - ~$400M reported
- The catalyst deal: Purpose-built platform for AI model security throughout their lifecycle
- Protection against prompt injection, data poisoning, jailbreaking, and unintentional model outcomes
- Integrated into Cisco Security Cloud for end-to-end AI security
- Mapped to OWASP and MITRE ATLAS standards
-
Coralogix → Aporia (December 23, 2024)
-
Torq → Revrod (April 16, 2025)
-
Palo Alto Networks → Protect AI (April 28, 2025)
-
Tenable → Apex Security (May 29, 2025)
-
Snyk → Invariant Labs (June 24, 2025)
-
SentinelOne → Prompt Security (August 5, 2025)
-
Cato Networks → Aim Security (September 3, 2025)
-
SentinelOne → ObservoAI (September 8, 2025)
-
F5 → CalypsoAI (September 11, 2025)
-
Check Point → Lakera (September 16, 2025)
-
CrowdStrike → Pangea (September 16, 2025)
-
Zscaler → SPLX (November 3, 2025)
In September alone, five major security vendors forked over $1.31 billion combined to gain positioning in AI security. This isn’t just healthy M&A activity—this is a land grab.
Why Cisco’s Move Changed Everything
Before we dive into what was acquired, let’s understand why Cisco’s Robust Intelligence deal was the inflection point.
Timing: According to Cisco’s 2024 AI Readiness Index, 95% of respondents believed AI would significantly impact IT infrastructure and security. But belief and action are different things. When Cisco—a networking giant that had just spent $28 billion on Splunk—immediately turned around and acquired an AI security startup for hundreds of millions, it validated that “Security for AI” was a distinct category requiring specialized solutions.
The market signal: Traditional security vendors had been trying to wrap existing tools around AI use cases. Cisco’s acquisition acknowledged that “traditional security tools often fall short in addressing the unique challenges posed by AI, creating a pressing need for specialized solutions.” This wasn’t about adding AI features to security tools (AI for security)—this was about building entirely new technology to secure AI systems themselves (security for AI).
Technical validation: Robust Intelligence’s platform offered protection for AI models throughout their lifecycle, from development to production, with specific capabilities for mitigating prompt injection, data poisoning, jailbreaking, and unintentional model outcomes—all mapped to OWASP and MITRE ATLAS standards. This level of specialization signaled that AI security required genuine R&D investment, not just repackaged existing tools.
Strategic positioning: By integrating Robust Intelligence into the Cisco Security Cloud, Cisco could provide visibility into all customer AI traffic across their network and security products. This wasn’t a point solution—it was platform-level thinking for a new attack surface.
Once Cisco made this move, the race was on. Every other major security vendor had to decide: build, buy, or get left behind.
What’s Actually Being Acquired?
These acquisitions aren’t cookie-cutter deals. Each tells a slightly different strategic story, but they cluster around several key capabilities that Cisco’s Robust Intelligence acquisition first validated as essential:
1. Prompt Injection Defense
SentinelOne’s Prompt Security and CrowdStrike’s Pangea acquisitions were both heavily focused on intercepting malicious prompts in real-time, scoring prompt risk, and injecting guardrails into AI interactions. F5’s CalypsoAI acquisition also enables red-teaming against agentic workflows to uncover emergent threats. This builds on what Robust Intelligence pioneered—protecting against prompt-based attacks mapped to OWASP standards.
2. AI Asset Discovery and Runtime Protection
Zscaler’s SPLX acquisition extends the platform with shift-left AI asset discovery, automated red teaming, and governance capabilities that secure organizations’ AI investments from development through deployment. This matters because AI infrastructure investments are projected to surpass $250 billion by the end of 2025. Cisco’s Robust Intelligence acquisition was the first to offer this comprehensive lifecycle protection.
3. Model Security and Red-Teaming
Cisco’s acquisition of Robust Intelligence was the blueprint: automated model testing, runtime validation, and compliance checks directly into the AI pipeline. Palo Alto’s Protect AI acquisition followed a similar path, providing testing, red teaming, and runtime protection. The key insight? AI models need fundamentally different security approaches than traditional applications.
4. Data Poisoning and Model Integrity
One of Robust Intelligence’s core capabilities—and a focus area for subsequent acquisitions—is protecting against data poisoning attacks that corrupt model training, and preventing jailbreaking attempts that bypass model safety controls. These threats don’t exist in traditional application security.
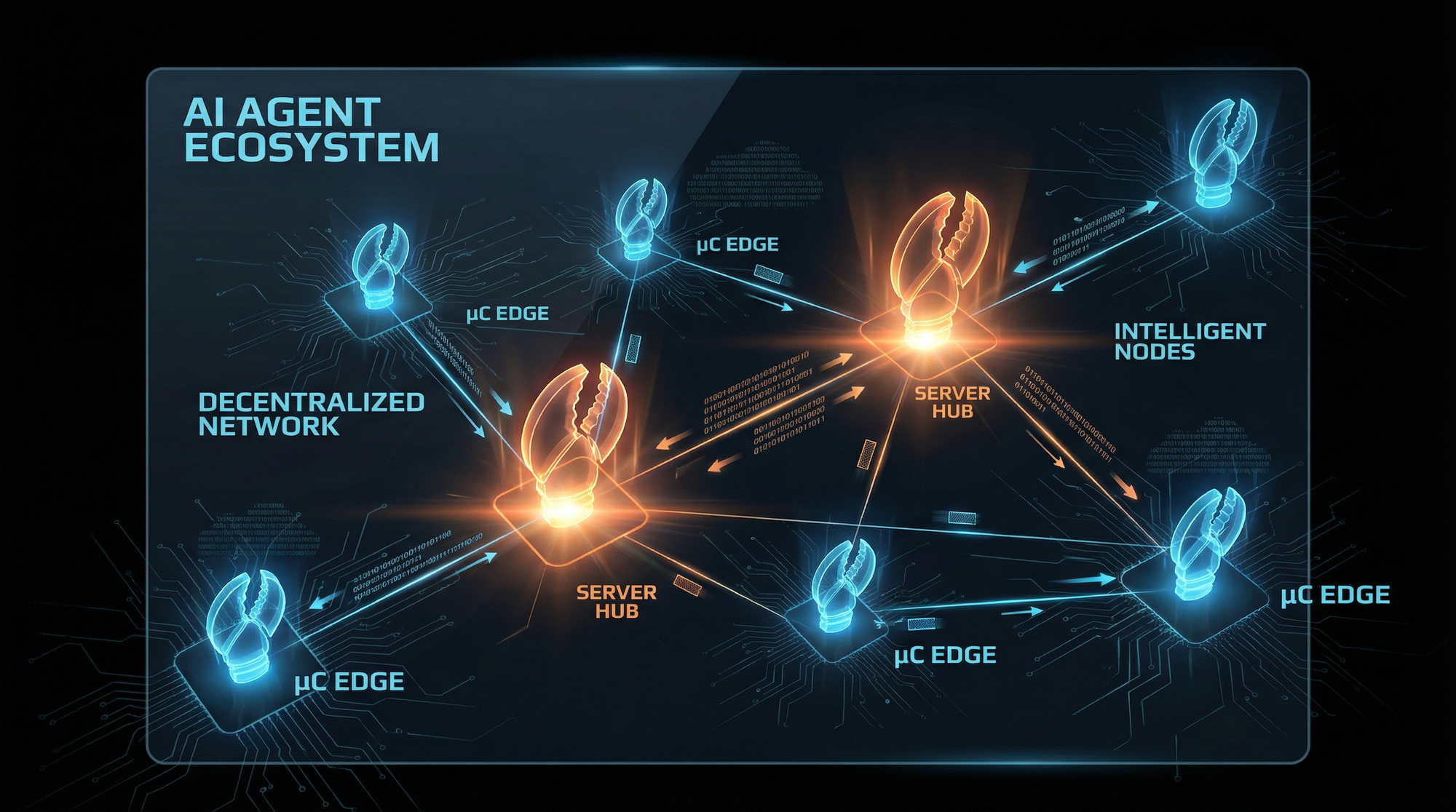
5. Agentic AI and MCP Protocol Security
Snyk’s purchase of Invariant Labs focuses on the Model Context Protocol (MCP), which governs how AI agents communicate with models and each other. This is critical as we shift from treating LLMs as tools to dealing with AI-based agents as autonomous actors.
6. Comprehensive Platform Plays
SentinelOne’s acquisition of both Prompt Security and ObservoAI created the most comprehensive coverage, spanning browsers, endpoints, APIs, and network proxies. These platforms had solutions for basically anywhere that AI lived, providing visibility and control across the entire enterprise AI ecosystem. This follows Cisco’s playbook of integrating AI security directly into existing data flows through networking and security products.
Why the Massive Imbalance?
Here’s where it gets interesting. While “Security for AI” is red-hot, the “AI for SOC” market remains relatively quiet on the M&A front. This divergence is particularly striking when you consider the broader market context: we’ve documented $85+ billion in mega-deals across cybersecurity in 2025 alone—including Google’s $32B Wiz acquisition and Palo Alto’s $25B CyberArk purchase—yet SOC automation tools aren’t getting scooped up despite obvious market need.
Why?
1. Business Risk vs. Operational Efficiency
Companies deploying AI face existential concerns about prompt injection, data leakage, and compliance violations that could tank their entire AI initiative. These are C-suite level concerns.
According to Zscaler, enterprises are blocking 18.5% of all AI and machine learning transactions—a 577% increase in blocked transactions over nine months—reflecting growing concerns around AI data security. When 63% of organizations have established limitations on what data can be entered into GenAI tools, and 27% have banned GenAI applications altogether, you’re looking at a market screaming for solutions.
SOC automation? It’s valuable, sure. But it’s an operational efficiency play competing for budget in mature, crowded markets with entrenched players like Splunk, Palo Alto, and Microsoft Sentinel.
2. Attach Rate to Every AI Deployment
Every single company shipping AI features needs new guardrails. Period. This creates a mandatory line item with potential for 100%+ net dollar retention as AI deployments expand.
Thirty-three percent of business and technology professionals report that their organization is using generative AI in production applications, and that number is climbing fast. Each one needs protection.
Compare that to SOC tools, which compete in a market where the average organization faces around 960 alerts per day, while large enterprises manage more than 3,000 alerts daily from an average of 28 different tools. The market is saturated and fragmented.
3. Technology Moats Are Real
Defending against AI-specific attacks requires genuinely new intellectual property. SPLX brought more than 5,000 purpose-built attack simulations for AI systems. You can’t just wrap existing security tech in an AI ribbon and call it done.
Most SOC automation, by contrast, is applying LLMs to existing security workflows. While AI technology is poised to revolutionize SOC operations, its adoption remains complicated by SOC leaders’ ongoing concerns about SIEM-related costs and implementation challenges. These are process improvements, not platform innovations.
4. Budget Dynamics
AI security spending comes from innovation budgets—the same pool funding AI development. These budgets are growing, and security is baked into the business case.
SOC tools fight for operational security budgets that are flat to declining and already allocated to incumbent vendors. Despite promises from legacy SOAR platforms and rule-based SIEM enhancements, many security leaders still face analyst alert fatigue, manual context correlation across disparate tools, and disjointed detection workflows.
5. Trust and Adoption Barriers in SOC
CISOs and SecOps leaders remain wary of AI solutions due to “trust issues” regarding their efficacy, and are not confident enough to place AI at the frontlines of the SOC. The demand-side challenge is significant—messaging about “replacing analysts” has created organizational resistance.
What About “AI for SOC”? Is It Dead?
Hell no. It’s just not ready for prime time M&A yet.
For more on where SOC automation is headed, check out our analysis on AI-Powered SOC Transformation, which covers the emerging platforms and operational models that will define the next generation of security operations.
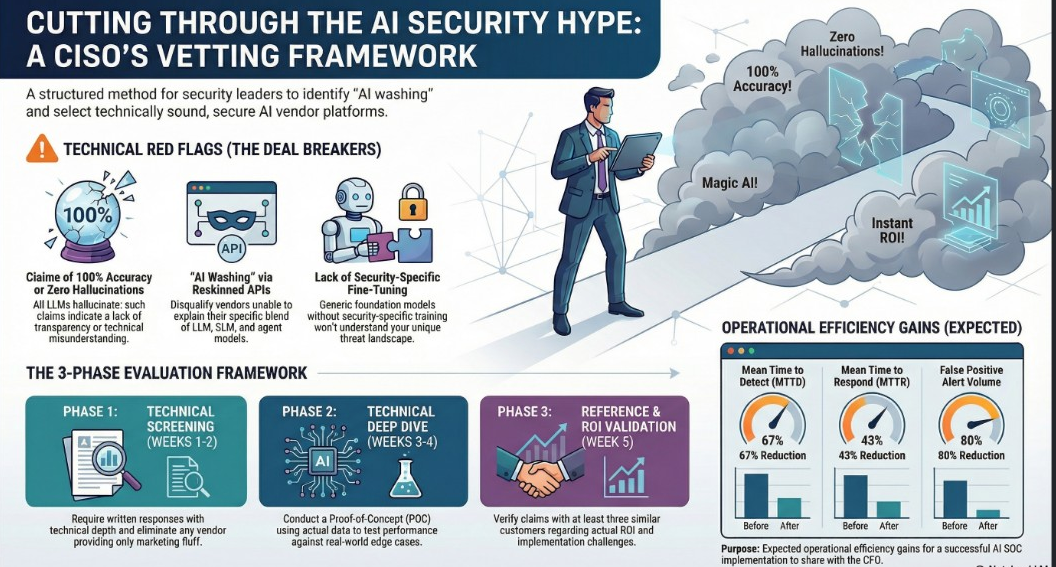
According to the Gartner Hype Cycle for Security Operations, 2025, AI SOC agents are in the Innovation Trigger stage with 1-5% penetration. This is extremely early adoption territory.
The technology is promising, but it’s facing real challenges:
- High implementation complexity - Traditional SOAR solutions required significant maintenance, scripting, and continuous integration work
- Limited adaptive learning - Many current solutions rely on predefined rules rather than true autonomous decision-making
- Integration overhead - They need to work with existing SIEMs, EDRs, ticketing systems, and dozens of other tools
- Skills atrophy concerns - Gartner predicts that by 2030, 75% of SOC teams will see a decline in core security analysis skills as they grow too reliant on automation and AI.
However, 88% of organizations that don’t yet run an AI-driven SOC plan to evaluate or deploy one within the next year. The interest is there. The market just isn’t mature enough for acquisition exits yet.
The Gen3 SIEM is Coming
We’re likely looking at a 2027-2028 timeline for AI SOC M&A to heat up. Here’s what needs to happen first:
- Agentic architectures mature - Current platforms are still figuring out how to balance deterministic automation with LLM-based reasoning
- Proof of ROI - Vendors need production deployments showing measurable improvement in MTTD/MTTR without introducing new failure modes
- Market consolidation - Too many point solutions right now; acquirers want proven platforms
- Budget reallocation - Security operations budgets need to shift from legacy SIEM licenses to next-gen automation
The technology is advancing rapidly. Google’s Security Operations platform now uses Gemini to automate data analysis, guide investigations, and streamline response actions, resulting in up to 240% ROI over three years and up to 70% reduction in breach risk and cost. Microsoft, Palo Alto, and others are making similar investments.
But these are being built, not bought. The acquisition market follows proven revenue and customer adoption at scale.
The Founder/Investor Lesson
There’s a critical insight here for anyone building in the security space:
New budget creates fast paths to M&A. Disrupting incumbents creates bigger outcomes, but takes longer.
If you’re building “Security for AI,” you’re creating a new category with new budget, minimal switching costs, and C-suite urgency. You can hit meaningful ARR fast, prove product-market fit quickly, and become acquisition-ready within 2-3 years.
If you’re building “AI for SOC,” you’re disrupting entrenched vendors with massive installed bases, complex integrations, and long sales cycles. You can build a more valuable company—the SOC market is enormous—but you need patient capital and a longer runway to prove you can actually replace Splunk or Palo Alto.
Both paths are valid. They’re just very different games with very different timelines.
📊 Quick Assessment: Is Your Organization Ready for These Market Shifts?
With all this M&A activity, now’s the time to baseline where you stand:
- Vendor Risk Exposure: Are you tracking which of your security vendors might be acquisition targets? Use our Vendor Risk Management platform to monitor third-party risk and build contingency plans
- SOC Maturity: Before investing in AI automation, understand your current capabilities. Rate Your SOC to identify gaps
- Team Readiness: M&A creates talent churn. Assess your team’s risk to ensure you can handle vendor transitions
The Hidden Risk: Post-Acquisition Reality Check
Here’s something nobody talks about enough: acquisitions often make products worse before they make them better.
When your AI security vendor gets acquired, expect:
- Support team consolidation - That 24/7 SOC you loved? Now it’s a shared tier-1 queue across the acquirer’s entire portfolio
- Roadmap integration delays - Features you were promised? Pushed back 12-18 months while they standardize on the parent company’s tech stack
- Sales rep turnover - Your champion who understood your environment? Gone. Now you’re account #4,573 to someone who just learned the product exists
- Price increases - Integration costs get passed to customers, renewal rates mysteriously climb 20-40%
- Feature deprecation - That integration you rely on? “Not aligned with our strategic direction”
Protect yourself:
- Assess vendor risk proactively using our VRM platform - track acquisition announcements, evaluate post-M&A support changes, and build contingency plans
- Lock in multi-year contracts before acquisition closes (if you can stomach the risk)
- Maintain competitive alternatives - Don’t get locked into a single vendor that might change overnight
- Document everything - SLAs, promised features, support response times. You’ll need this ammunition during renewals
Want to know if your security team is equipped to handle vendor transitions? Assess your team’s risk readiness before you’re scrambling during a product sunset.
What This Means for Security Practitioners
If you’re a CISO or security leader, here’s what you should be thinking about:
For AI Security (Short-term priority):
- Inventory your AI assets NOW - Shadow AI is everywhere, and you can’t protect what you don’t know exists
- Implement runtime guardrails - Your developers are calling external LLMs; you need visibility and control
- Red-team your AI applications - Prompt injection, data extraction, and model manipulation are real threats
- Establish governance policies - Who can use what AI tools? What data can they access?
- Track vendor acquisitions - When AI security vendors get acquired, assess the vendor risk impact on your security posture—support teams get trimmed, roadmaps change, and your favorite sales rep might be gone
For SOC Automation (Medium-term investment):
- Evaluate AI SOC platforms for pilot programs - The technology isn’t mature enough to rip-and-replace your SIEM, but you can start testing. Not sure where your SOC stands? Rate your SOC capabilities to establish a baseline before investing in automation
- Focus on Tier 1 alert triage first - This is where AI shows immediate ROI without high-risk decision-making
- Maintain human-in-the-loop for complex investigations - Full autonomy isn’t ready for production
- Plan for SIEM modernization - Legacy SIEMs face high operational costs, scalability issues, and integration hurdles with modern cloud-based security tools
The Bottom Line
We’re watching a masterclass in market timing. The AI security acquisition wave isn’t hype—it’s rational actors responding to genuine business needs with innovation budgets to match.
The AI for SOC market will have its day. The technology trajectory is clear, the need is real, and the potential market size is massive. But that day is probably 2-3 years out, when early adopters have proven ROI, analysts can trust the automation, and CFOs see compelling business cases to rip out incumbent solutions.
Until then, watch the smart money flow into “Security for AI.” They’re not chasing fantasy football defenses in round 6—they’re securing the infrastructure that’s reshaping every industry on the planet.
And if you’re a startup founder, pay attention to where the new budget is being created. That’s your signal.
About This Analysis
This article analyzes the recent wave of AI security M&A activity following Zscaler’s acquisition of SPLX on November 3, 2025. Data sourced from public acquisition announcements, including Cisco’s Robust Intelligence announcement, market research reports, and cybersecurity industry analysis as of November 2025. All acquisition dates and details verified through multiple sources.
Related Reading from Our Network
M&A and Market Trends:
- Cybersecurity Consolidation 2023-2025: Major M&A Deals and Market Dynamics - Deep dive into $167+ billion in cybersecurity M&A including mega-deals from Google, Palo Alto, and Cisco
AI Security Resources:
- AI-Powered SOC Transformation: Modernizing Security Operations 2025 - How AI is reshaping security operations centers
- Navigating the AI Revolution in Cybersecurity - Strategic guidance for security leaders
CISO Resources:
- CISO Marketplace (cisomarketplace.com) - Security tools and resources for technology leaders
- CISO Insights Podcast (podcast.cisomarketplace.com) - Conversations with cybersecurity executives
- Breached.company (breached.company) - Latest breach intelligence and threat analysis
- ComplianceHub.wiki (compliancehub.wiki) - Compliance frameworks and regulatory guidance
- Security Careers (securitycareers.help) - Career development for cybersecurity professionals
Free Assessment Tools:
- Vendor Risk Management (vrm.cisomarketplace.services) - Track vendor acquisitions and assess third-party security risk
- Rate My SOC (ratemysoc.com) - Benchmark your security operations center maturity
- Team Risk Assessment (teamrisk.securitycareers.help) - Evaluate your security team’s readiness and capability gaps
Published on CISO Marketplace | Empowering security leaders with actionable intelligence