How OpenClaw spawned 11+ spin-offs in 30 days, and why “Claws” are becoming the new layer of the AI stack
🎧 Related Podcast Episode
Executive Summary
A new category of software is emerging: Claws. Named after OpenClaw, the viral personal AI assistant that connects language models to messaging platforms and local files, “Claw” has become a term of art for persistent AI agent systems that run on personal hardware, communicate via messaging protocols, and can both act on direct instructions and schedule autonomous tasks.
In less than a month, OpenClaw’s explosive growth has spawned an entire ecosystem of derivatives—each optimizing for different constraints: security, size, hardware requirements, or enterprise readiness. This article examines the “Claw Wars,” the technical architectures driving these systems, and what this means for the future of personal computing. [
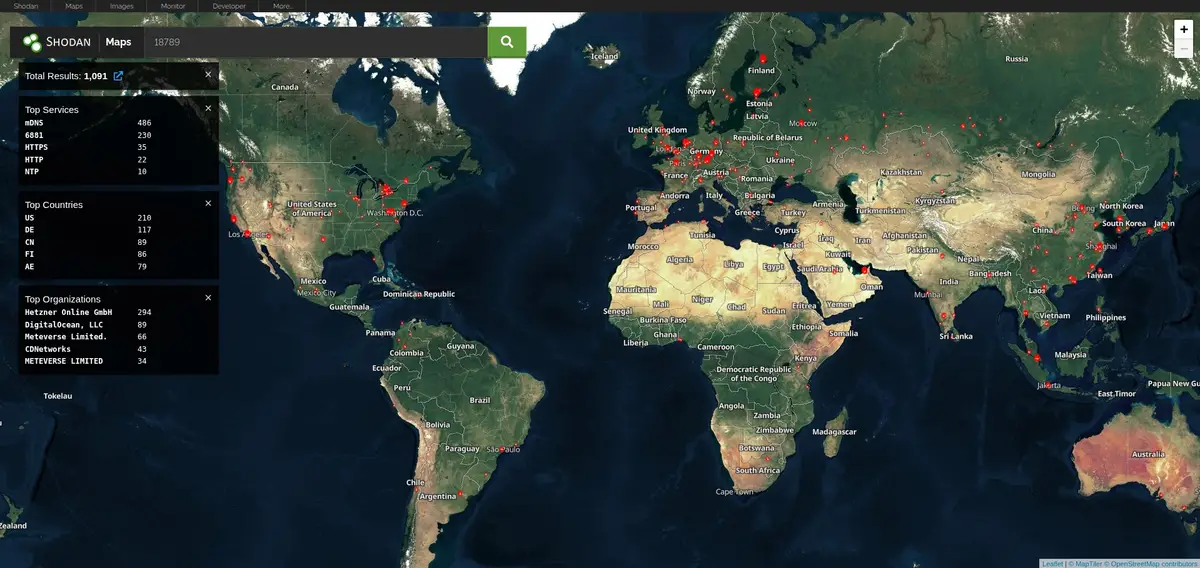
Over 1,000 Clawdbot AI Agents Exposed on the Public Internet: A Security Wake-Up Call for Autonomous AI Infrastructure
Executive Summary Clawdbot, the rapidly-adopted open-source AI agent gateway, has a significant exposure problem. Our research using Shodan and Censys identified over 1,100 publicly accessible Clawdbot gateway and control instances on the internet. While many deployments have authentication enabled, we discovered numerous instances requiring no authentication whatsoever—leaving API
![]()
Breached CompanyBreached Company
The OpenClaw Origin Story
OpenClaw (formerly Clawdbot/Moltbot), developed by Peter Steinberger, represents the reference implementation of the Claw concept. It’s a full-featured personal AI assistant that:
- Runs locally on your devices (Mac, Linux, Raspberry Pi, VPS)
- Connects to messaging platforms (WhatsApp, Telegram, Slack, Discord, iMessage, Google Chat)
- Bridges any AI model (Claude, GPT-4, DeepSeek, Gemini, local LLMs)
- Executes “skills” (tools) on your behalf—reading files, browsing the web, managing calendars, sending emails
- Operates 24/7 with scheduled tasks and autonomous capabilities
The Numbers
| Metric | OpenClaw |
| Codebase | ~430,000+ lines (Python) |
| Memory footprint | ~1.52 GB |
| Startup time | ~5.98 seconds |
| Modules | 50+ |
| Dependencies | 45+ |
| GitHub stars | 6,500+ |
In February 2026, Steinberger joined OpenAI to focus on personal agents, with Sam Altman confirming OpenClaw would continue as an open-source protocol supported by OpenAI.
But OpenClaw’s success revealed a problem: it’s too big.
The Problems That Sparked the Claw Wars
1. Security Concerns
OpenClaw’s 430,000 lines of code represent a massive attack surface. The system has near-unlimited permissions on the host machine, meaning a compromised agent could:
- Exfiltrate credentials and private keys
- Execute arbitrary code
- Access sensitive files
- Manipulate external accounts
For users unable to audit the codebase, running OpenClaw on a primary device is a significant risk. Documented cases exist of users losing cryptocurrency funds through agent manipulation.
2. Hardware Requirements
OpenClaw requires substantial compute—typically a Mac Mini or equivalent server. This creates barriers:
- Cost: Dedicated hardware isn’t feasible for everyone
- Isolation: Security-conscious users need separate devices
- Accessibility: Billions of potential users have only smartphones or low-powered devices
3. Production Readiness
As a single-machine assistant, OpenClaw isn’t designed for:
- Enterprise multi-tenant deployments
- IoT/embedded environments
- Microcontroller platforms
- Browser-based execution
These gaps created opportunities for derivatives to fill. [
CISO Marketplace | Cybersecurity Services, Deals & Resources for Security Leaders
The premier marketplace for CISOs and security professionals. Find penetration testing, compliance assessments, vCISO services, security tools, and exclusive deals from vetted cybersecurity vendors.
Cybersecurity Services, Deals & Resources for Security Leaders](https://cisomarketplace.com/blog/clawdbot-security-architecture-hardened-ai-agent-infrastructure-oracle-cloud)
The Claw Ecosystem: 11+ Variants
Security-First Implementations
NanoClaw
Creator: Gavriel Cohen (Qwibit)
Philosophy: “Dead simple so you can review all the code”
NanoClaw reduces OpenClaw’s 430,000 lines to just 500 lines. The core innovation: containerized isolation. Every agent runs inside a Linux container with access only to explicitly whitelisted folders.
- WhatsApp-first design
- Already in production use (Qwibit’s sales pipeline agent “Andy”)
- Complete audit possible in an afternoon
IronClaw
Creator: Near AI (Illia Polosukhin’s team)
Technology: Rust + WebAssembly sandboxing
Built specifically to prevent private key leaks and credential exposure, IronClaw takes a “your AI assistant should work for you, not against you” approach. Tool execution happens in WASM sandboxes, providing cryptographic verification of isolation.
ZeroClaw
Creator: ZeroClaw Labs
Philosophy: “Zero compromise”
A 100% Rust implementation achieving remarkable metrics:
| Metric | ZeroClaw | OpenClaw | Improvement |
| Binary size | 3.4 MB | 28+ MB | 8× smaller |
| Startup | <10 ms | 5.98 s | 600× faster |
| Memory | 7.8 MB | 1.52 GB | 194× smaller |
| Tests | 943 passing | — | Functional parity |
Security features include localhost-only binding, one-time pairing codes, and filesystem sandboxing.
Ultra-Lightweight Implementations
PicoClaw
Creator: Sipeed (embedded hardware company)
Technology: Go, self-bootstrapping design
PicoClaw brings agent capabilities to previously impossible hardware:
- Runs on $10 RISC-V boards with <10 MB RAM
- 1-second boot time (400× faster than OpenClaw)
- Single self-contained binary
- Targets: routers (32 MB RAM), IP cameras (64-128 MB), any Linux device
Remarkably, 95% of PicoClaw’s code was written by AI—a self-bootstrapping demonstration of the technology it enables.
GitHub stars: 3,100+ in first week.
MimiClaw
Platform: ESP32-S3 microcontroller
Language: C
MimiClaw proves agents can run on $5 hardware. With just 10 MB spare RAM, it acts as a gateway between Telegram and Claude—99% smaller than OpenClaw in code size.
TinyClaw
Creator: Jian Liao
Implementation: 400 lines of Shell script
Using Claude Code and tmux, TinyClaw recreates OpenClaw’s core functionality in a single shell script:
- WhatsApp channels ✓
- Heartbeat system ✓
- Cron jobs ✓
- Multiple agents addressable by name ✓
- Self-healing: Auto-fixes and restarts on failure
One TinyClaw agent ran for 3 days straight without human intervention. [
The #1 Most Downloaded AI Skill Was Malware. Here’s How 1,184 Poisoned Packages Slipped Past Everyone.
The ClawHavoc campaign is the most alarming AI supply chain attack to date — and most people still don’t know it happened. It started with a butler joke. Imagine you hire a brilliant personal assistant. He manages your calendar, reads your messages, runs errands on your behalf. He has keys to
![]()
Hacker Noob TipsHacker Noob Tips

Educational & Minimal Implementations
NanoBot
Creator: HKU Data Science Lab (University of Hong Kong)
Purpose: Educational skeleton framework
NanoBot strips agents to their essence: ~4,000 lines providing core functionality (24/7 operation, tool calling, memory). Ideal for learning agent architecture or building custom extensions.
Production & Enterprise Variants
MiniClaw
Focus: Smaller models, enterprise features
A production-oriented variant featuring:
- Web dashboard
- Plugin system
- Sandboxing
- Monitoring
- Multi-tenant support
ZeptoClaw
Technology: 5 MB Rust binary
Focus: Multi-tenant production deployments
Requires only 6 MB RAM while supporting enterprise-scale concurrent agents.
Subscription-Based Variants
Mini-Claw (hyphenated)
Innovation: Uses existing Claude Pro/ChatGPT Plus subscriptions
Eliminates API costs entirely by bridging Telegram to your existing AI subscriptions. No separate API keys required.
Kimi Claw
Creator: Moonshot AI
Platform: Browser-based, 24/7 availability
Features:
- ClawHub skill access
- 40 GB cloud storage
- Pro-grade search (Yahoo Finance integration)
- Web UI at kimi.com or Telegram bridge
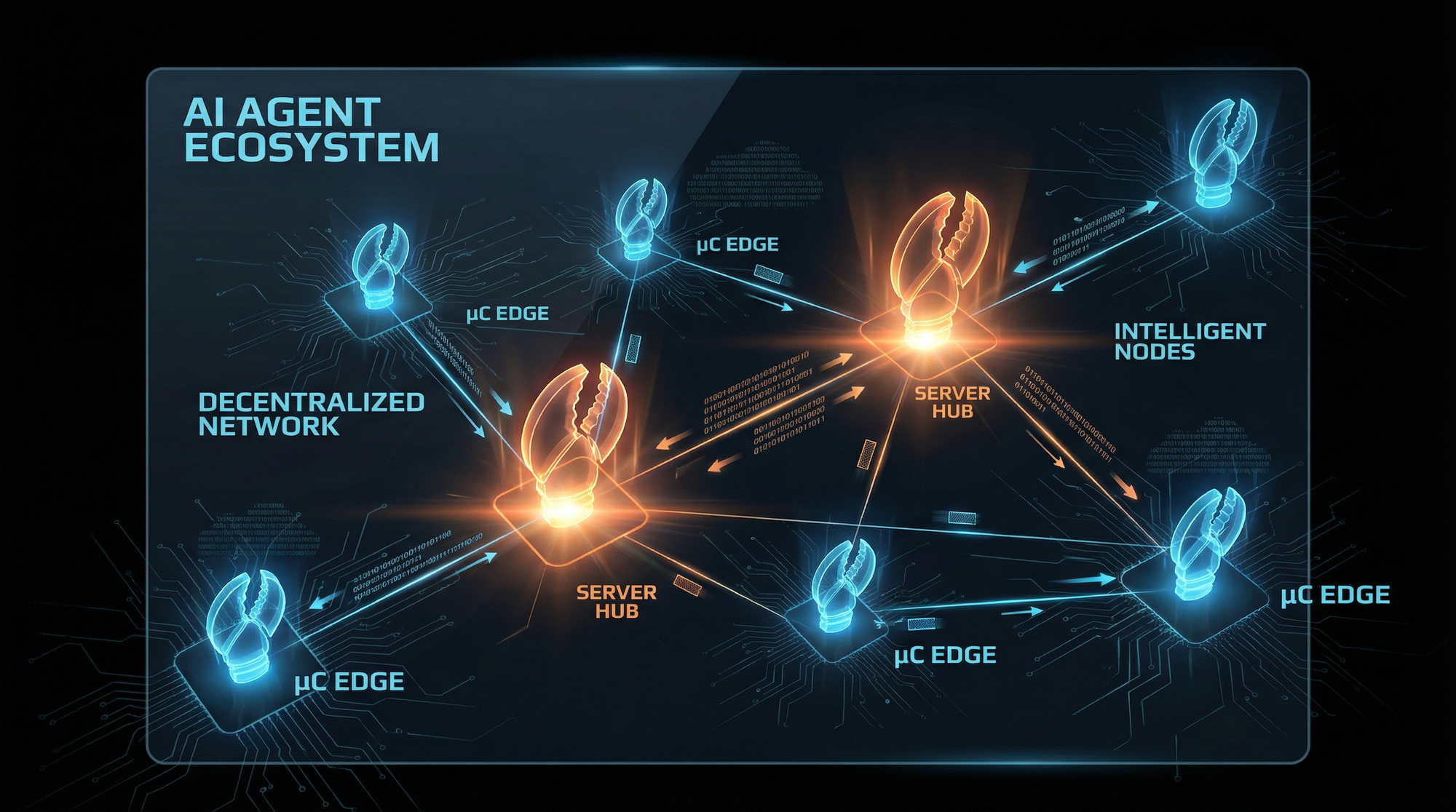
Architectural Deep Dive
Despite their differences, all Claws share a common architecture:
The Gateway Layer
A pure traffic controller with no embedded intelligence:
- Normalizes heterogeneous messaging protocols (WhatsApp, Telegram, Slack, Discord)
- Routes to isolated agent sessions
- Prevents context leakage between users
- Implements lane queues for deterministic execution
The Agent Execution Loop
A six-stage pipeline:
- Intake: Receive normalized message
- Context Assembly: Pull session history, semantic memory, workspace files, tool schemas
- Model Inference: Generate reasoning + structured tool calls
- Tool Execution: Dispatch to handlers (sandboxed or direct)
- Result Backfill: Inject tool outputs into conversation
- Streaming Reply: Deliver partial responses in real-time
Memory Architecture: Filesystem as Truth
OpenClaw and derivatives reject opaque vector databases:
- Short-term memory: Timestamped daily logs (Markdown files)
- Long-term memory: MEMORY.md, SOUL.md (distilled knowledge)
- Operating instructions: AGENTS.md (immutable per session)
Vector indices are ephemeral caches that rebuild from Markdown on startup. All agent knowledge remains human-readable, Git-versionable, and editable with any text editor.
Tool Framework
Tools follow a registry pattern:
- Name + description + JSON Schema parameters + execution handler
- Optional Docker sandbox (non-root, read-only filesystem, network isolation)
- Human-in-the-loop approval for critical operations (deletions, financial transactions) [
Your AI Coding Assistant Has a Plugin Problem: Inside the First Large-Scale Study of Malicious Agent Skills
And how to protect yourself from the 632 vulnerabilities researchers just found hiding in plain sight TL;DR — Key Takeaways * 🔬 First major study: Researchers analyzed 98,380 AI agent skills across two major community registries * ⚠️ 157 confirmed malicious skills containing 632 vulnerabilities — that’s 0.16% of the ecosystem * 🎯 Two attack
![]()
Hacker Noob TipsHacker Noob Tips

The Karpathy Effect
Andrej Karpathy’s recent commentary crystallized the category:
“Claws are an awesome, exciting new layer of the AI stack… sitting on top of agents that run on LLMs.”
He identifies the key characteristics:
- Run on personal hardware
- Communicate via messaging protocols
- Can act on direct instructions
- Can schedule autonomous tasks
This framing—Claws as “a layer running on top of agents”—positions them as infrastructure, not applications. The model does the thinking; the Claw does the doing.
Security Implications
The Claw Wars highlight a fundamental tension in AI agent design:
The Trade-Off Triangle
Capability
/\
/ \
/ \
/ \
/________\
Security Simplicity
- OpenClaw: Maximum capability, minimal security, high complexity
- NanoClaw/IronClaw: High security, reduced capability, moderate complexity
- PicoClaw/TinyClaw: High simplicity, moderate capability, emerging security
Recommendations for Enterprise
- Never run Claws on primary devices containing sensitive data
- Prefer containerized variants (NanoClaw) for production
- Audit tool permissions before enabling financial or credential operations
- Implement network segmentation for Claw hosts
- Monitor for anomalous behavior in agent execution logs
[
CISO Marketplace | Cybersecurity Services, Deals & Resources for Security Leaders
The premier marketplace for CISOs and security professionals. Find penetration testing, compliance assessments, vCISO services, security tools, and exclusive deals from vetted cybersecurity vendors.
Cybersecurity Services, Deals & Resources for Security Leaders](https://cisomarketplace.com/blog/soul-engineering-identity-layer-attacks-on-ai-agents)
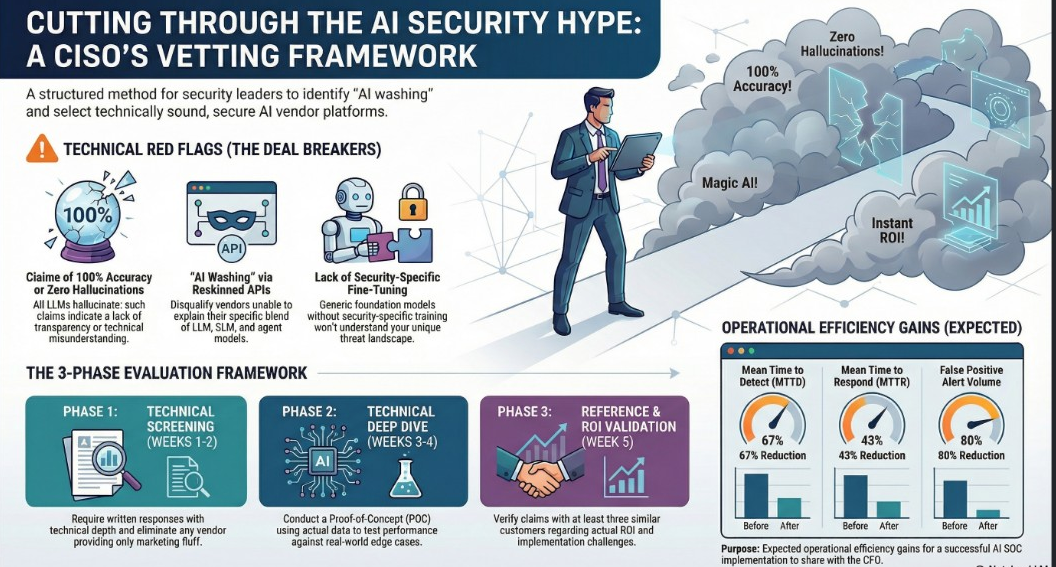
What This Means for CISOs
The Claw ecosystem creates both opportunities and risks:
Opportunities
- Security automation: Claws can monitor logs, triage alerts, draft incident reports
- Compliance assistance: Automated evidence gathering, policy review
- Threat intelligence: 24/7 monitoring and summarization of feeds
Risks
- Shadow AI: Employees deploying personal Claws on corporate devices
- Credential exposure: Agents with access to passwords, API keys, certificates
- Supply chain: Unaudited skills from ClawHub introducing vulnerabilities
- Data exfiltration: Compromised agents tunneling data through messaging channels
Recommended Controls
- Policy: Prohibit unapproved AI agent deployment on corporate assets
- Detection: Monitor for Claw process signatures and messaging API traffic
- Sandboxing: If approved, mandate containerized execution
- Audit: Review all enabled skills and tool permissions quarterly
The Road Ahead
The Claw Wars are just beginning. Watch for:
- Consolidation: Some variants will merge; others will fade
- Enterprise Claws: Multi-tenant, SOC 2-compliant implementations
- Mobile Claws: Agents running natively on iOS/Android
- Hardware Claws: Purpose-built Claw appliances (think: AI-native Raspberry Pi)
- Claw Protocols: Standards for inter-Claw communication
The question isn’t whether Claws will become ubiquitous—it’s whether we’ll secure them before they’re everywhere.
Conclusion
In 30 days, OpenClaw evolved from a single project to an entire ecosystem. The “Claw Wars” demonstrate what happens when a powerful idea meets the open-source community: rapid iteration, specialization, and an explosion of innovation.
For security professionals, this is both an opportunity and a warning. Claws are coming to every device—from data centers to $10 microcontrollers. The organizations that understand this shift will harness it. Those that don’t will be blindsided by employees’ personal AI assistants accessing corporate resources in ways no one anticipated.
The age of the Claw has begun.