🎧 Related Podcast Episode
Executive Summary
The global cybersecurity landscape in 2026 is defined by a pivotal transformation, moving from a reactive defense posture to a preemptive, AI-driven paradigm. This shift is compelled by the dual nature of artificial intelligence, which has emerged as both the primary engine of sophisticated cyberattacks and the core of next-generation defense systems, creating a high-stakes “AI-versus-AI battlefield.”
Economically, the market is returning to a growth trajectory, with global spending projected to reach between $240 billion and 300 billion, and some forecasts predicting it will exceed 520 billion. This investment is increasingly directed toward software-centric architectures, which now command 40% of enterprise security budgets, reflecting a strategic move away from traditional hardware appliances. This growth is driven by the escalating speed and scale of AI-powered threats, significant board-level engagement in cyber risk, and a complex web of new global regulations.
Strategically, the era of “detect and respond” is ending. The focus has decisively shifted to preemptive security, resilience, and architectural integration. Frameworks like Cybersecurity Mesh Architecture (CSMA) are becoming mandates to unify the sprawling ecosystem of security tools, combat complexity, and operationalize Zero Trust at scale. Concurrently, the looming threat of quantum computing has become a practical concern, compelling organizations to act on “harvest now, decrypt later” risks by beginning the migration to post-quantum cryptography.
Finally, 2026 represents a “compliance cliff,” as a cascade of major international regulations enters full enforcement. Key legislative frameworks include China’s amended Cybersecurity Law (CSL), the European Union’s AI Act, new SEC rules in the United States, Australia’s Cyber Security Act 2024, and India’s Digital Personal Data Protection (DPDP) Act. This convergence of technological disruption, economic realignment, and regulatory pressure demands a new level of strategic foresight from security leaders, who must now operate as “Risk Orchestrators” in an increasingly autonomous and volatile digital world.
1.0 Economic and Budgetary Outlook for 2026
After a period of measured spending in 2025, the cybersecurity market is forecast to return to a robust growth mode in 2026, driven by an evolving threat landscape and increasing executive accountability.
1.1 Market Growth and Spending Forecasts
Multiple analyses project significant growth in global cybersecurity expenditures for 2026:
- Global spending is projected to reach approximately $240 billion, a 12.5% increase from 2025’s $213 billion baseline. This marks a significant acceleration from 2025’s 4% growth rate, which was the slowest in five years.
- Other forecasts suggest worldwide IT security spending will approach $300 billion by 2026.
- A broader market view predicts global spending on cybersecurity products and services will exceed $520 billion annually by 2026.
1.2 Key Budget Drivers
The shift from 2025’s optimization focus to 2026’s growth orientation is fueled by several converging factors:
- AI-Powered Threat Evolution: Attackers are using generative AI to create 10,000 personalized phishing emails per minute.
- Deepfake Fraud Surge: Incidents of deepfake fraud increased by 3,000% in 2024, forcing a reassessment of authentication investments.
- Board-Level Engagement: Cybersecurity has become a core fiduciary duty, with increased executive accountability for risk management.
- Regulatory Pressure: A wave of new global and regional compliance requirements is driving mandatory investments in specific security controls.
- Cyber Insurance Requirements: Insurers are increasingly mandating specific security controls, such as microsegmentation, as a prerequisite for coverage.
1.3 Enterprise Budget Allocation
A fundamental shift toward software-centric security is reshaping how enterprise budgets are allocated. The decline of hardware appliances in favor of integrated, cloud-delivered platforms is a defining trend.
|
Budget Category |
Percentage of Total Budget |
2025 vs. 2026 Trend |
Key Drivers | |
Software/Security Tools |
~40% |
↗ Increasing |
Platform consolidation, AI-driven tools | |
Internal Personnel |
~30% |
→ Stable |
Talent shortage constraints, upskilling | |
Hardware/Appliances |
~15% |
↘ Declining |
Shift to software-defined security | |
Outsourced Services |
~15% |
↗ Increasing |
Skills gap, 24/7 monitoring needs | |
Training & Governance |
~5-10% |
→ Stable |
Compliance requirements |
Source: Forrester’s 2026 Budget Planning Guide
1.4 The Intensifying Cybersecurity Skills Gap
The global cybersecurity workforce shortage reached a record 4.8 million unfilled positions in 2025, a 19% year-over-year increase. This talent crisis directly impacts budget planning and increases financial risk, as organizations with staffing shortages face data breach costs that are, on average, $1.76 million higher than their well-staffed counterparts.
Top Skills in Demand for 2026:
|
Skill Area |
Percentage of Organizations Reporting Gaps | |
AI and Machine Learning Security |
34% | |
Cloud Security Expertise |
30% | |
Zero Trust Implementation |
27% | |
OT/IoT Security |
N/A (Essential for industrial sectors) | |
Incident Response & Forensics |
N/A (Critical for breach containment) |
2.0 The AI-Versus-AI Battlefield: Evolving Threats and Defenses
The year 2026 marks the moment AI moves from being a tool to becoming the battlefield itself. Adversaries are deploying autonomous, AI-driven attacks at machine speed, forcing organizations to adopt AI-powered defenses to keep pace.
2.1 The Proliferation of AI-Powered Attacks
Attackers are leveraging AI to automate and scale threats with unprecedented sophistication:
- Agentic AI Attacks: Autonomous AI agents are being developed to execute multi-step operations and interact with real systems, turning compromised agents into powerful, independent attack vectors.
- AI-Powered Social Engineering: Deepfake services and hyper-personalized AI are revolutionizing business email compromise (BEC) and extortion scams, making deception nearly impossible for humans to detect.
- Polymorphic and Adaptive Malware: AI is used to create malware that can dynamically adapt to defense conditions on the fly, evading traditional detection tools.
2.2 The Rise of AI-Driven Defense
To counter these threats, security strategies are becoming inherently AI-native.
- AI Security Platforms: These platforms provide a unified way to secure both third-party and custom-built AI applications. They centralize visibility, enforce usage policies, and protect against AI-specific risks like prompt injection, data leakage, and rogue agent actions. Gartner predicts that by 2028, over 50% of enterprises will use these platforms.
- AI-Native Development: GenAI is being used to create software faster and more securely, with some organizations creating small platform teams that enable non-technical domain experts to produce applications with security guardrails in place.
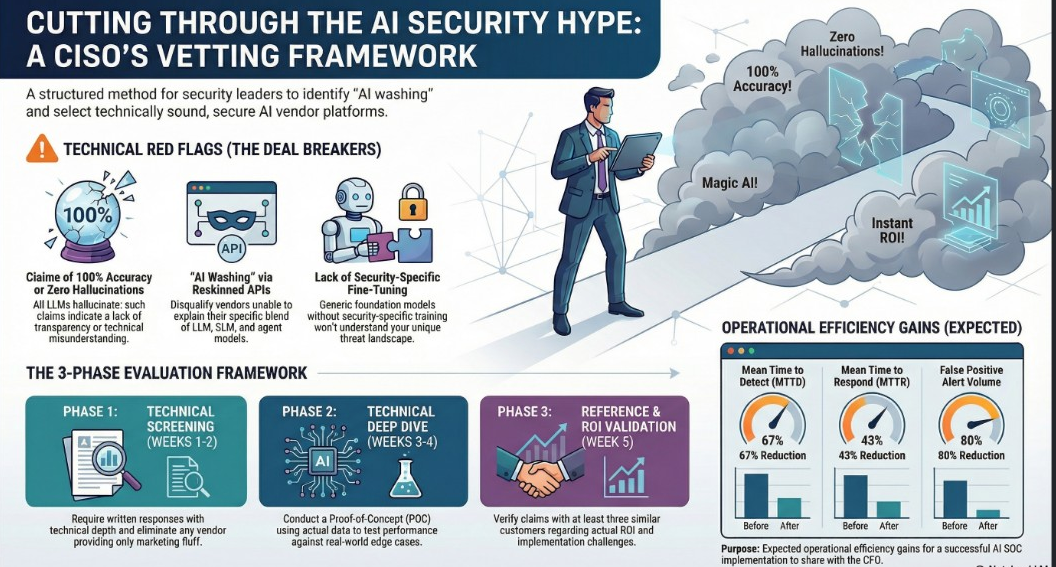
- Automated SOC Operations: AI and Machine Learning (ML) are becoming the analytical core of modern Security Operations Centers (SOCs), used for automated alert triage, investigation, and response.
2.3 Gartner’s Strategic Technology Trends for 2026
Gartner has identified several key technology trends for 2026 that directly impact the cybersecurity landscape.
|
Trend |
Description |
Cybersecurity Implication | |
Multiagent Systems (MAS) |
Collections of interacting AI agents that achieve complex goals. |
Requires unified visibility and governance to secure autonomous data flows and prevent rogue agent actions. | |
Domain-Specific Language Models (DSLMs) |
Language models trained on specialized data for a specific industry or function. |
Demands rigorous “digital provenance” controls to verify the integrity of training data and model outputs for compliance. | |
AI-Native Development Platforms |
Platforms that use GenAI to accelerate software creation. |
Security and governance guardrails must be embedded into the platform to manage risk in citizen-led development. | |
Confidential Computing |
Isolates sensitive data in hardware-based Trusted Execution Environments (TEEs). |
Protects data in use, which is critical for securing AI workloads in untrusted cloud or multi-tenant environments. | |
Physical AI |
AI that powers machines and devices like robots and drones. |
Expands the attack surface to the cyber-physical interface, demanding robust security for OT and industrial systems. |
3.0 Strategic and Architectural Imperatives
The speed and complexity of modern threats are rendering traditional, perimeter-based security models obsolete. In 2026, resilience, integration, and preemption are the guiding principles for enterprise security architecture.
3.1 The Shift to Preemptive Security
The industry has moved beyond the idea of perfect prevention, but the window between vulnerability discovery and exploitation has collapsed. This necessitates a shift from “detect and respond” to a preemptive defense posture. The focus is now on automated, memory-based, pre-execution prevention that can stop AI-modified and fileless attacks before they can execute.
3.2 Cybersecurity Mesh Architecture (CSMA): The Mandate for Integration
Complexity has become a primary security risk. The average enterprise now relies on 43+ security tools from 20 different vendors, leading to fragmented visibility, operational chaos, and an expanded attack surface.
Gartner’s Cybersecurity Mesh Architecture (CSMA) addresses this by promoting a collaborative ecosystem of integrated security tools. Rather than a “rip-and-replace” approach, CSMA weaves existing tools into a single intelligent fabric through four key layers:
- Security Intelligence and Analytics: Normalizes and correlates data from all tools to provide context and enable automated investigations.
- Identity Fabric: Unifies identity data to enable dynamic, least-privilege enforcement and cross-domain threat detection.
- Unified Posture, Policy, and Playbook Management: Centralizes security controls to enforce strategy consistently at scale.
- Integrated Operational Dashboard: Delivers a unified operational view that consolidates signals and prioritizes risks with business context.
3.3 The Resilience-First Mindset
Modern security strategy assumes that initial access will occur and that downtime is unacceptable. This resilience-first approach relies on two core concepts:
- Zero Trust Architecture: Moves from perimeter-focused defense to a comprehensive, identity-centric protection strategy. It requires coordinated investments across identity, devices, networks, applications, and data.
- Microsegmentation: A critical tactic for blocking lateral movement, which is involved in over 70% of cyberattacks. By implementing granular network controls, organizations can contain breaches and minimize business impact. A budget allocation of 15-20% for microsegmentation is recommended.
3.4 Identity as the New Perimeter
Identity has officially replaced the network as the primary cyber battleground. However, 75% of security leaders lack full identity visibility, and only 33% are confident in their identity security posture. Attackers are increasingly “becoming” someone with access by stealing authentication cookies and cloud tokens. In response, buying priorities are shifting toward unified identity visibility, machine identity discovery, and holistic identity strategies that move beyond traditional ZTNA.
4.0 The Looming Quantum Threat
The risk posed by quantum computing has transitioned from a theoretical future concern to a present-day threat. Although large-scale quantum attacks are still years away, adversaries are acting now.
4.1 “Harvest Now, Decrypt Later” Operations
Sophisticated adversaries, including nation-state actors, are actively conducting “harvest now, decrypt later” operations. This involves stealing large volumes of encrypted data today with the expectation that future quantum computers will be able to break current encryption standards (like RSA and ECC) and decrypt it. Once this becomes viable, decades’ worth of sensitive information could be exposed.
4.2 The Shift to Post-Quantum Cryptography (PQC)
In response, governments and critical industries are beginning the migration to post-quantum cryptography (PQC). The Post-Quantum Cryptography Coalition (PQCC) published a PQC Migration Roadmap in May 2025 to guide organizations. The key priorities for 2026 are:
- Inventory Cryptographic Assets: Begin auditing where and how encryption is used across all systems, applications, and vendors.
- Develop a PQC Roadmap: Plan phased transitions to quantum-resistant technologies, including pilot projects.
- Build “Crypto Agility”: Implement solutions that allow for the rapid switching of cryptographic algorithms as new standards are finalized.
5.0 The 2026 Global Regulatory Compliance Cliff
The year 2026 is a pivotal “compliance cliff” for organizations globally, as several major pieces of cybersecurity and data protection legislation move into full enforcement.
5.1 People’s Republic of China: Amended Cybersecurity Law (CSL)
-
Effective Date: January 1, 2026.
-
Key Changes:
- Increased Penalties: Maximum fines for general cybersecurity violations increase from RMB 1 million to RMB 10 million (approx. USD 1.41 million) for Critical Information Infrastructure Operators (CIIOs) and from RMB 100,000 to RMB 2 million for non-CIIOs.
- Expanded Scope: The law’s extraterritorial reach is broadened to cover any activities by overseas parties that harm China’s cybersecurity, not just those targeting critical infrastructure.
- AI Governance: The amendments integrate AI considerations, suggesting AI governance will be treated as a core dimension of cybersecurity compliance.
5.2 European Union: AI Act and Digital Sovereignty
-
Key Regulations: The EU AI Act, Digital Operational Resilience Act (DORA), NIS2 Directive, and Cyber Resilience Act create a complex regulatory environment.
-
AI Act Timeline:
- Governance rules and obligations for general-purpose AI models become applicable on August 2, 2025.
- A “Digital Omnibus” proposal suggests extending compliance deadlines for certain “high-risk” AI systems to December 2, 2027 (Annex III) and August 2, 2028 (Annex I) to allow time for harmonized standards to be developed.
5.3 United States: SEC Enforcement and Priorities
- Regulation S-P Amendments: New rules compelling investment advisers and broker-dealers to adopt incident response programs have a compliance deadline of June 3, 2026, for smaller entities.
- Enforcement Shift: Under new leadership, the SEC is expected to prioritize charging individuals responsible for misconduct over imposing large corporate penalties. The focus is shifting to traditional fraud, such as insider trading (especially in the biotech sector), rather than technical violations.
- Cybersecurity Disclosures: Despite the dismissal of the SolarWinds lawsuit, the SEC’s Cyber and Emerging Technologies Unit will continue to police material misrepresentations and omissions in cybersecurity disclosures that lead to investor harm.
- 2026 Examination Priorities: The SEC will increase its focus on firms’ use of AI for fraud prevention and trading, assessing whether capabilities are properly disclosed and controlled.
5.4 Australia: New Cyber Security Act 2024
-
Key Measures: Stemming from the 2023–2030 Australian Cyber Security Strategy, the Act introduces several new obligations.
- Mandatory Ransomware Payment Reporting: Businesses with an annual turnover exceeding $3 million must report any ransomware payment to the government within 72 hours.
- Cyber Incident Review Board (CIRB): A new board is established to review significant cybersecurity incidents and can compel the production of information.
- Limited Use Obligation: Information voluntarily shared with the National Cyber Security Coordinator (NCSC) is protected from use in civil proceedings to encourage greater transparency.
- IoT Security Standards: The government can define mandatory security standards for smart devices sold in Australia.
5.5 India: Digital Personal Data Protection (DPDP) Act
-
Phased Implementation: The DPDP Act is being implemented in stages.
-
Key Timelines:
- The registration of “Consent Managers”—intermediaries that help users manage data permissions—becomes mandatory in November 2026.
- Core provisions regarding data principal rights and data fiduciary security safeguards are scheduled to become fully effective by May 2027.
6.0 Evolving Roles: The Modern SOC and CISO
The technological and regulatory pressures of 2026 are forcing a radical evolution in both security operations and leadership.
6.1 Modernizing the Security Operations Center (SOC)
Lean SOC teams are expected to do more with fewer resources, manage sprawling tool stacks, and reduce analyst burnout. This is driving a shift toward operational efficiency and predictability.
-
Key Priorities: SOC buyers are prioritizing platform consolidation, AI automation embedded into workflows, and predictable cost control.
-
SOC as a Service (SOCaaS): SOCaaS is becoming a dominant model for enterprises seeking 24/7 detection and response without the heavy capital expenditure of an in-house SOC. Adopters have been found to achieve 20-40% faster detection cycles.
-
Critical KPIs: Modern SOCs are being measured against stringent benchmarks demanded by regulatory pressure, such as:
- Mean Time to Detect (MTTD): < 10 minutes
- Mean Time to Respond (MTTR): < 1 hour
6.2 The CISO 3.0: From Technologist to Risk Orchestrator
The role of the Chief Information Security Officer (CISO) is evolving from a technical manager to a strategic business leader. In the “agentic era” of 2026, the “CISO 3.0” must act as a “Risk Orchestrator,” navigating a complex ecosystem of autonomous systems, geopolitical risks, and board-level financial scrutiny. This requires balancing technological implementation with business integration, stakeholder alignment, and demonstrating a clear, measurable return on investment for security initiatives.