In today’s escalating cyber warfare landscape, technical security tools alone are insufficient. The most sophisticated attacks target the human element of cybersecurity—exploiting gaps in team capabilities, overwhelming incident responders, and leveraging organizational weaknesses that no technology can address. For CISOs, the question isn’t just whether your security infrastructure can withstand nation-state attacks, but whether your security team possesses the skills, resilience, and organizational alignment necessary to defend against sophisticated adversaries. [
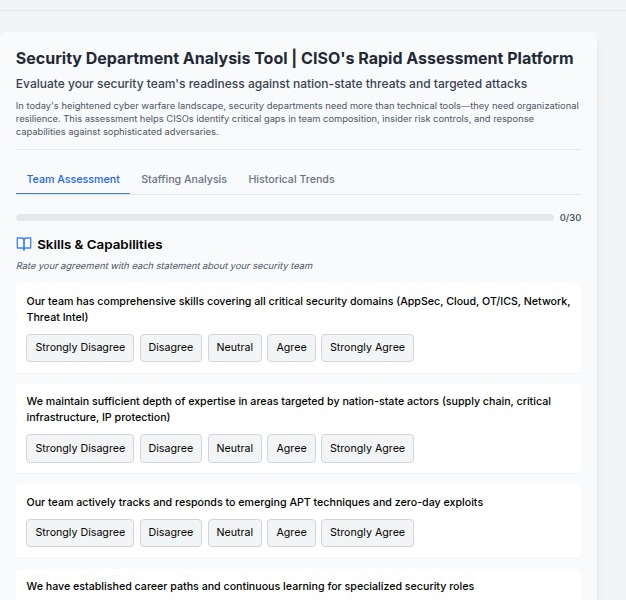
Security Team Risk Assessment Tool | CISO’s Rapid Assessment Platform
Evaluate your security team’s readiness against sophisticated threats. Identify critical gaps in team composition and capabilities.
Security Team Risk Assessment Tool

](https://teamrisk.securitycareers.help/)
The sobering reality is that most security teams are unprepared for the advanced persistent threats (APTs) and targeted campaigns they face daily. While organizations invest heavily in security technologies, they often overlook the critical importance of building resilient, capable security teams that can adapt to evolving threats and maintain effectiveness under pressure.
The Evolution of Security Team Challenges
From Reactive Response to Proactive Resilience
Traditional security team assessments focus on technical certifications and incident response metrics. While important, these measures fail to capture the holistic capabilities required to defend against modern threats. Today’s security teams must demonstrate:
Adaptive Expertise: The ability to quickly understand and respond to novel attack techniques, zero-day exploits, and sophisticated evasion methods employed by nation-state actors.
Psychological Resilience: The mental fortitude to maintain decision-making effectiveness during high-stress incidents, extended campaigns, and psychological manipulation tactics.
Organizational Integration: The capability to align security objectives with business goals while maintaining appropriate executive support and resource allocation.
Continuous Evolution: The commitment to ongoing learning and capability development in response to rapidly evolving threat landscapes. [
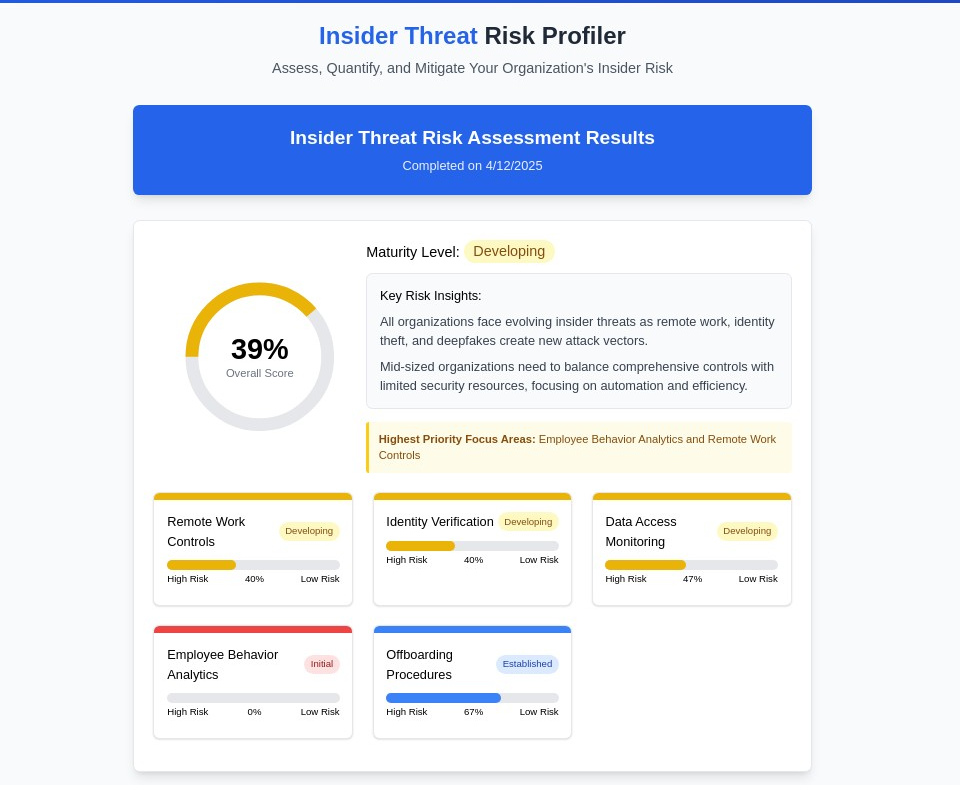
The Evolution of Insider Threats: Why Your Security Framework Needs an Urgent Update
The cybersecurity landscape has fundamentally shifted. While organizations have historically focused on building walls to keep external threats out, the most significant risks now often originate from within. Today’s insider threats are more sophisticated, harder to detect, and exponentially more damaging than ever before. Insider Threat Risk Profiler | Modern Security
![]()
Security Careers HelpSecurity Careers
The Nation-State Challenge
Nation-state actors represent the apex of cyber threat sophistication. These adversaries possess:
- Unlimited Resources: State-sponsored teams operate with extensive budgets, advanced tools, and long-term strategic objectives
- Advanced Capabilities: Access to zero-day exploits, custom malware, and sophisticated social engineering techniques
- Strategic Patience: Willingness to conduct multi-year campaigns with multiple attack vectors and contingency plans
- Intelligence Integration: Coordination between cyber operations and traditional intelligence gathering activities
Defending against such adversaries requires security teams that match their sophistication, persistence, and strategic thinking.
The Six Pillars of Security Team Excellence
1. Skills & Capabilities: Building Comprehensive Expertise
Modern security teams must maintain expertise across an expanding array of technical domains while developing specialized knowledge in areas targeted by advanced adversaries.
Core Domain Mastery Security teams require comprehensive skills across critical areas:
- Application Security (AppSec): Deep understanding of secure development practices, code review techniques, and application vulnerability assessment
- Cloud Security: Expertise in securing multi-cloud environments, containerized applications, and cloud-native architectures
- Operational Technology (OT/ICS): Specialized knowledge of industrial control systems, SCADA networks, and critical infrastructure protection
- Network Security: Advanced understanding of network forensics, traffic analysis, and network-based attack detection
- Threat Intelligence: Capability to collect, analyze, and operationalize intelligence about adversary tactics, techniques, and procedures
Nation-State Focus Areas Teams must develop specialized expertise in domains frequently targeted by nation-state actors:
- Supply Chain Security: Understanding of software supply chain attacks, hardware trojans, and third-party risk management
- Critical Infrastructure Protection: Knowledge of sector-specific vulnerabilities and attack methods targeting power grids, transportation systems, and communication networks
- Intellectual Property Protection: Expertise in defending against economic espionage, trade secret theft, and research and development targeting
Emerging Threat Adaptation Security teams must actively track and respond to:
- Advanced Persistent Threat (APT) Techniques: Continuous monitoring of new tactics employed by sophisticated adversary groups
- Zero-Day Exploit Management: Rapid response capabilities for previously unknown vulnerabilities and attack methods
- Artificial Intelligence Threats: Understanding of AI-powered attacks, deepfake technologies, and machine learning vulnerabilities
2. Team Resilience: Sustaining Effectiveness Under Pressure
Cyber incidents, particularly those involving nation-state actors, can last weeks or months. Security teams must maintain effectiveness throughout extended high-stress scenarios.
Psychological Fortitude
- Decision-Making Under Pressure: Training team members to make sound judgments during crisis situations
- Stress Management: Developing individual and team strategies for managing sustained high-stress operations
- Cognitive Load Management: Preventing decision fatigue and maintaining analytical capabilities during complex incidents
Operational Continuity
- Personnel Redundancy: Ensuring critical security functions have backup personnel with equivalent skills and clearances
- Knowledge Documentation: Maintaining comprehensive documentation that enables team members to assume unfamiliar roles during emergencies
- Rotation Protocols: Preventing burnout through strategic personnel rotation during extended incidents
Team Cohesion
- Communication Protocols: Establishing clear, efficient communication channels that function under stress
- Collaborative Decision-Making: Developing processes that leverage collective expertise while maintaining rapid response capabilities
- Mutual Support Systems: Building team cultures that support individual resilience and collective effectiveness
3. Insider Risk Controls: Protecting Against Internal Threats
Sophisticated adversaries often attempt to recruit insiders or exploit trusted access. Security teams must implement robust controls to mitigate these risks.
Access Management
- Least Privilege Principles: Implementing granular access controls that limit exposure if credentials are compromised
- Privileged Account Security: Securing administrative accounts used by security team members
- Separation of Duties: Dividing critical security functions to prevent single points of failure or compromise
Behavioral Monitoring
- Anomaly Detection: Implementing systems that identify unusual behavior patterns among security team members
- Peer Review Processes: Establishing procedures for validating critical security decisions and actions
- Continuous Vetting: Ongoing assessment of security team members’ trustworthiness and potential compromise indicators
Cultural Integration
- Security Awareness: Ensuring security team members understand insider threat risks and protective measures
- Reporting Mechanisms: Creating safe channels for reporting concerning behavior or potential compromise
- Response Procedures: Developing protocols for investigating and responding to potential insider threats within the security organization
4. Adversary Focus: Understanding and Countering Targeted Attacks
Effective defense requires deep understanding of adversary motivations, capabilities, and tactics specifically directed at your organization.
Threat Modeling
- Adversary Profiling: Developing detailed understanding of threat actors likely to target your organization
- Attack Surface Analysis: Identifying assets and vulnerabilities that attract sophisticated adversaries
- Campaign Attribution: Connecting observed activities to known adversary groups and their typical operations
Counter-Intelligence Awareness
- Social Engineering Recognition: Training team members to identify and resist sophisticated manipulation attempts
- Information Security: Protecting sensitive information about security capabilities, personnel, and operations
- Operational Security: Maintaining appropriate secrecy around security team activities and defensive measures
Proactive Defense
- Threat Hunting: Actively searching for indicators of adversary presence within organizational networks
- Deception Technologies: Deploying honeypots, canary tokens, and other deception mechanisms to detect intrusions
- Threat Disruption: Engaging in activities that increase adversary costs and reduce attack effectiveness
5. Organizational Alignment: Integrating Security with Business Objectives
Security teams must align their activities with organizational goals while maintaining appropriate independence and authority.
Executive Engagement
- Strategic Communication: Effectively communicating security risks and requirements to executive leadership
- Resource Advocacy: Building compelling cases for security investments and team expansion
- Business Partnership: Aligning security initiatives with business objectives and operational requirements
Cross-Functional Collaboration
- IT Integration: Working effectively with IT teams to implement security controls without disrupting operations
- Legal Coordination: Collaborating with legal teams on incident response, regulatory compliance, and threat intelligence sharing
- HR Partnership: Coordinating with human resources on personnel security, training, and insider threat programs
Governance Framework
- Policy Development: Creating security policies that balance protection with operational efficiency
- Risk Management: Integrating security risk assessment with enterprise risk management processes
- Compliance Oversight: Ensuring security operations meet regulatory requirements and industry standards
6. Incident Response: Rapid Detection and Effective Remediation
When sophisticated attacks occur, security teams must respond rapidly and effectively to minimize damage and gather intelligence.
Detection Capabilities
- Monitoring Infrastructure: Maintaining comprehensive visibility across organizational networks and systems
- Alert Prioritization: Effectively triaging security alerts to focus on the most critical threats
- Threat Correlation: Connecting disparate indicators to identify coordinated attack campaigns
Response Coordination
- Incident Command: Establishing clear leadership and coordination structures during security incidents
- External Collaboration: Working effectively with law enforcement, intelligence agencies, and industry partners
- Communication Management: Balancing transparency with operational security during incident response
Recovery and Learning
- Forensic Analysis: Conducting thorough post-incident analysis to understand attack methods and improve defenses
- Lessons Integration: Incorporating incident learnings into defensive improvements and team training
- Resilience Building: Using incident experience to strengthen team capabilities and organizational defenses [
Security Team Risk Assessment Tool | CISO’s Rapid Assessment Platform
Evaluate your security team’s readiness against sophisticated threats. Identify critical gaps in team composition and capabilities.
Security Team Risk Assessment Tool

](https://teamrisk.securitycareers.help/)
Assessment Methodology: Measuring Team Readiness
Comprehensive Evaluation Framework
Effective security team assessment requires systematic evaluation across multiple dimensions:
Skills Assessment
- Technical Proficiency: Evaluating hands-on capabilities across core security domains
- Specialized Knowledge: Assessing expertise in areas relevant to specific threat landscapes
- Continuous Learning: Measuring commitment to ongoing skill development and adaptation
Capability Testing
- Scenario-Based Exercises: Testing team performance under realistic threat scenarios
- Red Team Engagements: Evaluating defensive capabilities against simulated advanced attacks
- Tabletop Exercises: Assessing decision-making and coordination during complex incidents
Organizational Integration
- Alignment Assessment: Measuring how well security objectives integrate with business goals
- Resource Adequacy: Evaluating whether teams have sufficient tools, personnel, and authority
- Executive Support: Assessing leadership commitment to security team effectiveness
Scoring and Improvement
Performance Categories
- Strong (80-100%): Teams demonstrate excellent capabilities with minimal vulnerabilities
- Adequate (60-79%): Solid foundations exist but improvement opportunities are present
- Developing (40-59%): Basic capabilities exist but significant gaps require attention
- At Risk (0-39%): Critical vulnerabilities exist that require immediate remediation
Improvement Prioritization Assessment results should drive targeted improvement initiatives:
- Critical Gap Remediation: Immediate attention to vulnerabilities that pose existential risks
- Capability Enhancement: Strategic investments in areas that provide maximum defensive improvement
- Continuous Development: Ongoing programs to maintain and expand team capabilities
Building Career Paths for Specialized Security Roles
Developing Advanced Expertise
Security teams require individuals with specialized skills that go beyond traditional cybersecurity training:
Threat Intelligence Specialists
- Technical Analysis: Deep-dive capability in malware analysis, network forensics, and attack attribution
- Strategic Assessment: Understanding of geopolitical factors that influence threat actor behavior
- Communication Skills: Ability to translate technical intelligence into actionable business guidance
Critical Infrastructure Defenders
- OT/ICS Expertise: Specialized knowledge of industrial control systems and operational technology
- Safety Integration: Understanding of how cybersecurity intersects with physical safety systems
- Regulatory Knowledge: Familiarity with sector-specific regulations and compliance requirements
Advanced Incident Responders
- Forensic Capabilities: Expert-level skills in digital forensics and evidence preservation
- Coordination Leadership: Ability to manage complex, multi-stakeholder incident response efforts
- Communication Excellence: Skills in briefing executives, law enforcement, and external partners
Continuous Learning Frameworks
Formal Education Pathways
- Advanced Certifications: Industry certifications relevant to specialized security domains
- Graduate Education: Master’s degree programs in cybersecurity, intelligence analysis, or related fields
- Professional Development: Ongoing training in emerging technologies and threat landscapes
Experiential Learning
- Cross-Functional Rotations: Exposure to different aspects of security operations and business functions
- Industry Collaboration: Participation in information sharing organizations and threat intelligence communities
- Simulation Training: Regular participation in advanced tabletop exercises and red team engagements
Retention and Motivation
Career Advancement
- Technical Leadership Tracks: Advancement opportunities that don’t require abandoning technical work
- Specialization Recognition: Formal recognition and compensation for specialized expertise
- Innovation Opportunities: Encouragement to develop new defensive techniques and technologies
Professional Growth
- Conference Participation: Support for attending and presenting at industry conferences
- Research Opportunities: Time and resources for security research and tool development
- Mentorship Programs: Structured programs connecting senior and junior security professionals
Staffing Analysis: Building Optimal Team Composition
Role Specialization
Modern security teams require diverse skill sets and role specializations:
Core Security Functions
- Security Operations Center (SOC) Analysts: 24/7 monitoring and initial incident response
- Threat Hunters: Proactive searching for indicators of sophisticated attacks
- Incident Response Specialists: Expert-level responders for complex security incidents
- Vulnerability Management: Systematic identification and remediation of security weaknesses
Specialized Capabilities
- Malware Analysts: Deep technical analysis of malicious software and attack tools
- Forensic Investigators: Digital forensics and evidence collection for legal proceedings
- Threat Intelligence Analysts: Collection and analysis of adversary tactics and capabilities
- Security Architects: Design and implementation of comprehensive security frameworks
Business Integration Roles
- Security Compliance Officers: Ensuring adherence to regulatory requirements and industry standards
- Risk Analysts: Quantitative assessment of security risks and control effectiveness
- Security Awareness Coordinators: Training and culture development across the organization
- Vendor Security Managers: Third-party risk assessment and security requirement enforcement
Team Sizing Considerations
Baseline Staffing Requirements
- Organization Size: Scaling security team size based on organizational complexity and risk profile
- Industry Factors: Adjusting staffing based on sector-specific threats and regulatory requirements
- Technology Environment: Accounting for the complexity of infrastructure and application portfolios
Surge Capacity Planning
- Incident Response Scaling: Ensuring adequate personnel for extended incident response operations
- Cross-Training Requirements: Developing redundant capabilities to maintain operations during staff absences
- Contractor Integration: Planning for augmenting internal teams with external specialists during major incidents
Historical Trends and Predictive Analysis
Threat Evolution Tracking
Security teams must understand how threats have evolved and anticipate future developments:
Attack Sophistication Trends
- Tool Development: Tracking the evolution of attack tools and techniques over time
- Adversary Adaptation: Understanding how threat actors adapt to defensive improvements
- Technology Integration: Anticipating how emerging technologies create new attack vectors
Organizational Impact Analysis
- Incident Frequency: Tracking how often different types of security incidents occur
- Impact Assessment: Measuring the business impact of various security events over time
- Response Effectiveness: Evaluating how team performance changes over time and through different incidents
Predictive Capabilities
Future Threat Assessment
- Emerging Technology Risks: Anticipating security challenges from new technologies like AI, IoT, and quantum computing
- Geopolitical Influences: Understanding how international relations affect cyber threat landscapes
- Industry Targeting Trends: Predicting which sectors and organizations are likely to face increased targeting
Capability Gap Prediction
- Skill Demand Forecasting: Anticipating future security skill requirements based on threat evolution
- Technology Adoption Impacts: Understanding how new security technologies will change team composition and capabilities
- Resource Planning: Predicting future staffing and training requirements based on threat trends
Implementation Roadmap: Building Resilient Security Teams
Phase 1: Assessment and Baseline (Months 1-3)
Comprehensive Team Evaluation
- Skills Assessment: Systematic evaluation of current team capabilities across all critical domains
- Gap Analysis: Identification of specific areas where team capabilities fall short of requirements
- Threat Alignment: Assessment of how well current team composition matches organizational threat profile
Documentation and Planning
- Capability Mapping: Detailed documentation of current team skills, roles, and responsibilities
- Improvement Prioritization: Ranking of capability gaps based on risk impact and improvement feasibility
- Resource Requirements: Assessment of budget, time, and external support needed for improvements
Phase 2: Foundation Building (Months 4-12)
Critical Gap Remediation
- Emergency Hiring: Recruiting specialists for the most critical capability gaps
- Intensive Training: Accelerated training programs for existing team members in priority areas
- External Partnerships: Establishing relationships with external experts and service providers
Process Development
- Standard Operating Procedures: Documenting key processes for consistent team performance
- Communication Protocols: Establishing clear communication channels and escalation procedures
- Training Programs: Implementing ongoing education and skill development initiatives
Phase 3: Advanced Capability Development (Months 12-24)
Specialization Programs
- Expert Development: Advanced training for team members in specialized areas
- Certification Achievement: Supporting team members in obtaining relevant professional certifications
- Research Integration: Encouraging participation in security research and tool development
Organizational Integration
- Executive Engagement: Building stronger relationships between security teams and organizational leadership
- Cross-Functional Collaboration: Improving cooperation with other organizational functions
- Culture Development: Building a strong security culture that supports team effectiveness
Phase 4: Continuous Excellence (Ongoing)
Performance Optimization
- Regular Assessment: Quarterly evaluation of team performance and capability development
- Adaptive Training: Adjusting training programs based on emerging threats and organizational changes
- Innovation Encouragement: Supporting team innovation in defensive techniques and technologies
Strategic Evolution
- Threat Adaptation: Continuously adapting team composition and capabilities to match evolving threats
- Industry Leadership: Establishing the organization as a leader in security team development and effectiveness
- Knowledge Sharing: Contributing to industry knowledge through conference presentations and publications
Measuring Success: Key Performance Indicators
Team Capability Metrics
Skills Development
- Certification Achievement: Tracking professional certifications earned by team members
- Training Completion: Measuring participation in and completion of training programs
- Skill Assessment Scores: Regular evaluation of technical and strategic capabilities
Operational Effectiveness
- Incident Response Times: Measuring how quickly teams can detect and respond to security incidents
- Threat Detection Accuracy: Evaluating the quality of threat detection and analysis
- Recovery Performance: Assessing how effectively teams restore normal operations after incidents
Organizational Impact Metrics
Risk Reduction
- Vulnerability Metrics: Tracking improvements in organizational security posture
- Incident Frequency: Measuring whether better teams result in fewer successful attacks
- Business Continuity: Evaluating team effectiveness in maintaining business operations during security events
Strategic Alignment
- Executive Satisfaction: Regular feedback from organizational leadership on security team performance
- Business Integration: Measuring how well security initiatives support business objectives
- Resource Optimization: Evaluating the return on investment in security team development
The Future of Security Team Excellence
Emerging Challenges
Artificial Intelligence Integration Security teams must adapt to both AI-powered attacks and AI-enhanced defensive capabilities:
- AI Threat Analysis: Understanding how adversaries use artificial intelligence to enhance attacks
- Defensive AI Implementation: Leveraging machine learning and AI tools to improve security operations
- Human-AI Collaboration: Developing effective partnerships between human analysts and AI systems
Quantum Computing Implications The emergence of quantum computing will fundamentally change cryptography and security:
- Quantum-Safe Cryptography: Preparing for the transition to post-quantum cryptographic systems
- Threat Timeline Assessment: Understanding when quantum threats will become practical concerns
- Strategic Planning: Developing long-term plans for quantum-era security operations
Hybrid Warfare Evolution The integration of cyber operations with traditional warfare creates new challenges:
- Multi-Domain Operations: Understanding how cyber attacks integrate with physical and information warfare
- Critical Infrastructure Targeting: Preparing for attacks that combine cyber and physical components
- International Cooperation: Building relationships for cross-border threat response and intelligence sharing
Strategic Recommendations
Investment Priorities
- Human Capital: Prioritizing investment in team development over technology acquisition
- Specialized Expertise: Focusing on developing capabilities that can’t be easily outsourced or automated
- Adaptive Capacity: Building teams that can rapidly adapt to new threats and technologies
Organizational Evolution
- Flatter Hierarchies: Reducing bureaucratic overhead to enable rapid response and decision-making
- Cross-Functional Integration: Breaking down silos between security and other organizational functions
- Innovation Culture: Encouraging experimentation and creative approaches to security challenges
🎧 Related Podcast Episode
Conclusion: The Human Element in Cybersecurity
In an era of increasingly sophisticated cyber threats, technology alone cannot provide adequate protection. The most critical factor in organizational cybersecurity is the capability, resilience, and effectiveness of security teams. Organizations that recognize this reality and invest systematically in building exceptional security teams will be best positioned to defend against nation-state actors, advanced persistent threats, and the emerging challenges of tomorrow.
Success requires more than hiring skilled individuals. It demands comprehensive assessment, systematic development, and ongoing investment in human capabilities. The organizations that master this challenge will not only protect their assets and operations but also contribute to broader national and international cybersecurity resilience.
The future belongs to organizations that recognize security teams as strategic assets worthy of significant investment and careful development. The question isn’t whether sophisticated threats will target your organization—it’s whether your security team will be ready to defend against them effectively.
[
Security Team Risk Assessment Tool | CISO’s Rapid Assessment Platform
Evaluate your security team’s readiness against sophisticated threats. Identify critical gaps in team composition and capabilities.
Security Team Risk Assessment Tool

](https://teamrisk.securitycareers.help/)
Ready to evaluate your security team’s readiness against advanced threats? Use our comprehensive assessment tool to identify capability gaps and develop a roadmap for building a world-class security organization.