In today’s interconnected digital landscape, cybersecurity is no longer just about protecting human users. A new, rapidly expanding category of digital entities—Non-Human Identities (NHIs)—has emerged as a critical, yet often overlooked, area of enterprise security. These invisible workforces, powered by cloud computing, automation, and increasingly, artificial intelligence, are vital to modern operations, but their unchecked proliferation creates significant vulnerabilities.
What are Non-Human Identities (NHIs)?
Non-human identities are the digital credentials and permissions assigned to automated actors like machines, software, and background processes. They are essentially the “social security numbers” for these entities, enabling them to securely prove their identity and interact within an IT ecosystem without human intervention. [
Securing Tomorrow’s Enterprise: A CISO’s Guide to Navigating AI, NHIs, and the Escalating Secrets Sprawl in 2025
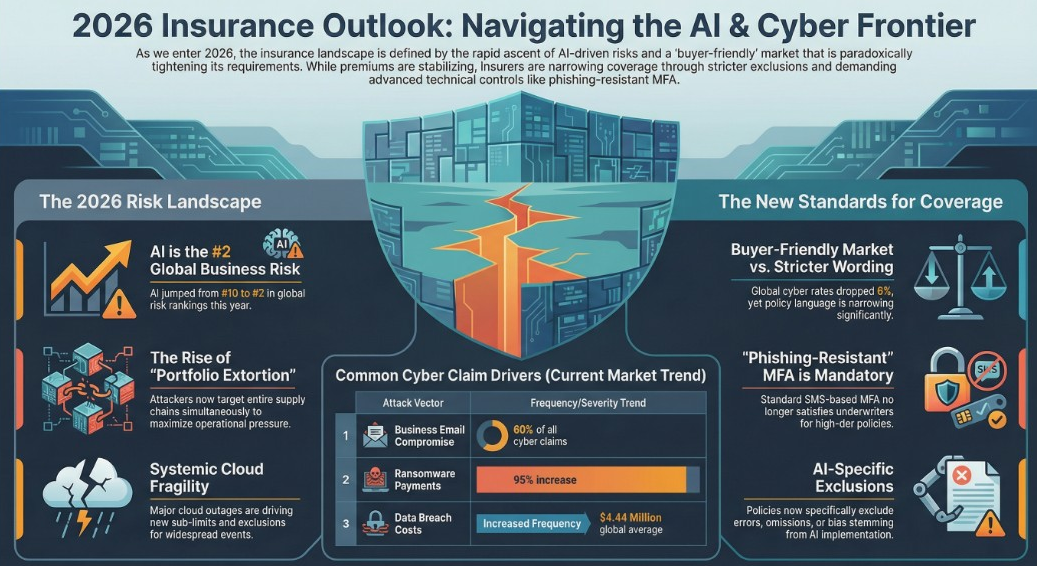
The year 2025 presents a critical juncture for cybersecurity leaders. While the promise of Artificial Intelligence (AI) for productivity and innovation is undeniable, its rapid adoption, coupled with the proliferation of non-human identities (NHIs) and low-code/no-code platforms, is fueling an unprecedented surge in secrets sprawl across the enterprise. For
![]()
Security Careers HelpSecurity Careers
Common examples of NHIs include:
- Service Accounts / Application Accounts: Used by applications and services to run automated tasks, integrate systems, and connect applications to databases and APIs.
- API Keys & OAuth Tokens: Unique credentials that enable secure communication and data exchange between software components and applications.
- Certificates: Digital certificates authenticate workloads, services, or devices to ensure secure communication.
- Machine Identities: Secure device identities widely used by virtual machines (VMs), containers, and Internet of Things (IoT) devices.
- DevOps Tools: Automated build and deployment tools within CI/CD pipelines use NHIs to access code repositories, trigger builds, and deploy applications.
- AI Agents: Autonomous systems designed to act on behalf of a person or organization, making decisions and interacting with systems.
Unlike human identities, which are typically managed centrally and protected by multiple layers of security, NHIs are often decentralized, numerous, and frequently rely on single “secrets” for access. They now vastly outnumber human identities, sometimes by as much as 45:1 or even 100:1, doubling in ratio from 2021 to 2023.
Why is Non-Human Identity Management Crucial? The Risks of “Secrets Sprawl”
The sheer volume and decentralized nature of NHIs lead to a phenomenon known as “secrets sprawl” or “identity sprawl” . This refers to the widespread and unmanaged distribution of digital authentication credentials across an organization’s IT environment. When secrets are scattered and poorly managed, they introduce significant risks:
- Expanded Attack Surface: Every NHI—every service account, API token, and machine identity—presents a potential entry point for attackers. This massive proliferation creates a significantly larger attack surface that can easily be overlooked in security strategies.
- High-Value Targets with Overprivileged Access: NHIs often hold elevated or “overprivileged” access rights to critical systems and sensitive data, granted to facilitate seamless operations. If a compromised NHI has excessive permissions, attackers can exploit these to gain unauthorized access, escalate privileges, and move laterally within the network.
- Secret Leakage: Sensitive NHIs like API keys, tokens, and certificates frequently end up in unsanctioned data stores throughout the software development lifecycle. They may be hard-coded into source code, stored in plain text configuration files, or sent over public chat applications, making them highly susceptible to exposure. This “Secret Leakage” is identified as the #2 risk in the OWASP Top 10 Non-Human Identity Risks for 2025, implicated in over 80% of breaches.
- Difficulty in Tracking and Monitoring: The large volume of NHIs, coupled with their creation across various systems and teams, leads to limited centralized visibility. This makes it challenging to understand the full scope of NHI activity, identify risks, and enforce consistent security policies, especially since traditional security tools often miss NHI activity. NHIs also lack human judgment, making it harder to detect “suspicious” activities without proper security measures.
- Lack of Lifecycle Management: NHIs are often created and then forgotten, leading to an accumulation of “zombie” or orphaned credentials. Inconsistent offboarding processes fail to properly remove unused tokens, creating persistent security gaps. The use of “long-lived secrets” with distant or no expiration dates further compounds this risk by providing attackers with prolonged access if breached.
- Risks from AI Agents: The explosive growth of AI agents introduces specific identity challenges. Unverified AI agents can lead to fraud, create synthetic identities, pose security threats by being hijacked to access sensitive data, and spread misinformation. Without verifiable digital identities, it becomes difficult to know whose AI agent is operating, what it’s authorized to do, or who is accountable when things go wrong.
- Compliance Violations: Regulatory frameworks like PCI DSS 4.0 and NIST are increasingly demanding strong controls for machine identities, including least privilege, secure onboarding, and continuous monitoring. Unmanaged NHIs complicate efforts to meet these requirements, leading to potential compliance failures and penalties. [
DevSecOps Maturity Calculator | Security Posture Assessment Tool
Evaluate your organization’s security posture and receive actionable recommendations to strengthen your security practices.
![]()
DevSecOps Maturity Calculator

](https://devsecops.vibehack.dev/)
Best Practices for Effective Non-Human Identity Management
Securing NHIs requires a departure from traditional human IAM approaches and the implementation of targeted strategies to address their unique vulnerabilities.
- Comprehensive Visibility and Inventory: The first step is to discover and inventory all NHIs across your environments, including their ownership, last rotation, and access scope. This centralized view is foundational for effective governance.
- Policy Enforcement and Least Privilege: Establish clear policies for the secure creation, rotation, and decommissioning of NHIs. Enforce the principle of least privilege (POLP), granting NHIs only the minimum permissions necessary for their tasks. This significantly reduces the attack surface and potential impact of a compromise.
- Automated Credential Lifecycle Management: Manual secret management is prone to errors and increases risk. Automate credential rotation and expiration to eliminate hard-coded, long-lived secrets. Solutions like Aembit’s platform aim to reduce work related to credential rotation by up to 95%. Leveraging managed identities in cloud environments like Azure can also securely handle authentication without storing credentials in code.
- Continuous Monitoring and Anomaly Detection: Implement continuous monitoring of NHI usage patterns to detect unusual activity, such as access outside of normal hours or privilege escalations. Advanced analytics and anomaly detection enable rapid response to high-risk events and policy violations.
- Embrace Zero Trust Principles: Never assume trustworthiness. Always verify every access request, even for authenticated NHIs. Aembit, for example, is designed to provide foundational elements for Zero Trust for workloads, focusing on identity and policy-based access to services.
- Dedicated Workload IAM Platforms: Enterprises are moving towards Workload Identity and Access Management (IAM), which provides a unified approach to managing and securing application-to-service access. Platforms like Aembit aim to manage workload-to-workload access based on identity rather than secrets, similar to how Okta manages human user identities.
- Inclusive Design Processes and Training: Address potential biases in AI systems by using diverse training datasets, conducting regular algorithmic audits, and ensuring human oversight for sensitive access requests. Organizations should also train personnel on NHI security risks and best practices to prevent misconfigurations and vulnerabilities. [
Vibe Hacking Security Assessment | Security for AI-Generated Code
Identify and fix security vulnerabilities in AI-generated code with our comprehensive assessment tool and tailored AI prompts.
Vibe Hacking Security AssessmentVibe Hacking Security Team

Conclusion: Securing the Future of Digital Interactions
Non-human identities are now at the core of modern infrastructure, driving automation, cloud services, and AI-powered environments. Leaving them unmanaged creates one of the largest and most dangerous attack surfaces, risking financial loss, reputational damage, and compliance failures. [
AI RMF to ISO 42001 Crosswalk Tool
Navigate between NIST AI Risk Management Framework and ISO/IEC 42001 standards with our interactive crosswalk tool.
![]()
AI Risk Management Framework to ISO 42001 MappingAI Risk Assessment

](https://compliance.airiskassess.com/)
By implementing comprehensive visibility, strong governance, lifecycle automation, and continuous monitoring, organizations can secure NHIs with the same rigor applied to human identities. This proactive approach, moving from “managing credentials to managing access”, is essential for building a resilient cybersecurity posture and confidently embracing the innovations of the AI-enabled future.