A Deep Dive into the Legal, Strategic, and Practical Implications of Enlisting Private Companies in Offensive Cyber Operations
🎧 Related Podcast Episode
Executive Summary
The Trump administration is drafting a National Cybersecurity Strategy that represents a seismic shift in how America conducts cyber warfare. According to four former senior U.S. officials, the forthcoming strategy includes provisions to substantially expand the role of private companies in offensive cyberattacks against foreign adversaries, criminal organizations, and state-sponsored threat actors. [
Why the US Cyber Force Debate Reveals Deeper Problems Than Organization Charts Can Fix
Analysis: While Congress debates whether to create a seventh military branch for cyber operations, the fundamental structural and cultural problems that plague USCYBERCOM remain unaddressed—and China just reorganized its cyber forces for the second time in a decade. The Organizational Agility Gap While the United States has spent the
![]()
Security Careers HelpSecurity Careers

This proposal moves beyond the current model where the government contracts private companies to develop cyberoperations tools, instead positioning private sector firms as active participants in executing offensive cyber campaigns. The initiative raises profound questions about legality, attribution, escalation management, international law compliance, and the fundamental nature of warfare in the digital age.
The Current Legal Framework: Why This Changes Everything
Existing Constraints
Under current U.S. law, private companies are explicitly prohibited from conducting offensive cyber operations. The Computer Fraud and Abuse Act (CFAA) of 1986 restricts private cybersecurity firms to purely defensive activities. Any offensive action—from network intrusion to data exfiltration to system disruption—constitutes a federal crime when conducted by non-governmental actors.
This legal barrier exists for good reason. The threshold between defensive security measures and offensive cyber operations is not merely technical but strategic. When a private company crosses that line, it potentially implicates the United States in actions that could be interpreted as acts of war.
Required Congressional Action
Changing this framework would require congressional approval through new legislation. This is not a policy that can be implemented via executive order or administrative guidance alone. The constitutional implications are significant enough that lawmakers would need to explicitly authorize this fundamental shift in how the nation conducts cyber warfare.
Historical precedent exists: Congress has explored similar concepts before, with legislators proposing various frameworks including:
- “Hack back” legislation allowing companies to actively pursue attackers into their infrastructure
- Letters of Marque for cyberspace—a constitutional provision (Article I, Section 8, Clause 11) last used during the War of 1812, which authorized private citizens to seize enemy ships
The Letters of Marque Debate: From Privateers to Cyber Pirates?
The Historical Model
Letters of Marque represent one of the most intriguing proposals circulating in Congress. This constitutional authority allowed the government to deputize private vessels during wartime, essentially legalizing what would otherwise be piracy by granting official sanction to capture enemy ships and cargo.
The practice was widespread during America’s founding era:
- Extensively used during the Revolutionary War
- Critical during the War of 1812 when the U.S. Navy was too small to confront British naval power
- Privateers operated under specific restrictions defined in their letters
- Violated restrictions resulted in legal liability and reparations
Modern Legislative Efforts
Recent Congressional proposals:
- Scam Farms Marque and Reprisal Authorization Act of 2025 (H.R. 4988)
- Introduced by Rep. David Schweikert (R-AZ) in August 2025
- Would authorize the President to commission private entities with letters of marque
- Targets foreign scam operations, particularly in Myanmar and North Korea
- Allows seizure of “person and property” of cybercriminals outside U.S. territories
- Cartel Marque and Reprisal Authorization Act
- Introduced by Sen. Mike Lee (R-UT) and Rep. Tim Burchett (R-TN)
- Focused on drug cartels but establishes similar privateering framework
- Would allow private seizure of cartel assets on land and sea
- Active Cyber Defense Certainty Act
- Long-discussed in Congress over multiple sessions
- Would permit companies to “hack back” against attackers
- Critics call it “the worst idea in cybersecurity”
The Cyber Piracy Concern
Lt. Gen. Charles L. Moore Jr., retired deputy commander of U.S. Cyber Command, warns that uncontrolled private sector offensive operations create “the specter of U.S.-approved piracy in cyberspace.”
In a report co-authored with Brett Goldstein and published by Vanderbilt University’s Institute of National Security, Moore articulates the core risk:
“If you just have companies out there hacking back, what you end up with is potential chaos in the environment. You’re going to have actions that take place by private companies against nation-states that believe that was the formal position of the United States, and now you see escalation, and potentially even kinetic conflict come of that. You’re going to see chaos.”
The Strategic Case: Why Privatization Is Being Considered
Capacity and Scale Challenges
Proponents argue that the U.S. government simply lacks sufficient capacity to match the scale and persistence of cyber threats from adversaries like China, Russia, Iran, and North Korea. This challenge is compounded by the administration’s simultaneous $1 billion investment in offensive cyber operations while cutting defensive cybersecurity programs, a controversial rebalancing that has drawn sharp criticism from security experts.
The Moore-Goldstein report identifies the core problem:
“The demand signal is too large, the threat landscape too dynamic and the technical talent pool too competitive for the department to meet future requirements with government personnel alone.”
The adversary advantage:
- Chinese-linked operations like Salt Typhoon campaign against critical infrastructure over years
- Russian persistent assaults on Ukraine and allied networks
- State-sponsored groups with abundant resources and minimal constraints
- Operates continuously across global timezones with coordinated teams
Current U.S. limitations:
- Isolated, periodic offensive operations rather than sustained campaigns
- Limited personnel with appropriate clearances and expertise
- Slow procurement and staffing processes
- Cannot match adversary operational tempo
The Shift from Deterrence to Persistent Campaigning
General Moore advocates for a fundamental strategic shift: moving from periodic action to persistent campaigning. The goal is to “throw sand into the gears of enemy cyberoperations” through continuous, scaled offensive actions.
This approach requires:
- Rapid increase in operational scale
- Sustained pressure on adversary infrastructure
- Pre-positioning for potential wartime cyber operations
- Proactive disruption rather than reactive defense
Joe Lin, former Navy Reserve officer who runs cyberwarfare start-up Twenty, explains the emerging consensus:
“There is much more of a consensus now that offensive cyberoperations are actually much less escalatory than people previously believed that they were.”
This perception shift matters enormously. If policymakers believe cyber operations pose less escalation risk than previously assumed, they become more willing to authorize aggressive campaigns.
Implementation Models: How It Could Work Without Changing the Law
While fully independent private cyber operations would require new legislation, the Moore-Goldstein report identifies several frameworks that could expand private sector involvement within existing legal structures:
Model 1: Embedded Military Operators
Concept: Place uniformed cyberoperators within private companies who actually execute the attacks while contractors provide support, intelligence, and tooling.
Advantages:
- Maintains clear chain of command
- Preserves government accountability
- Keeps trigger-pulling authority with military
- Leverages private sector technical expertise
Challenges:
- Still requires significant military personnel
- May not achieve desired scale
- Complex operational security concerns
- Integration and coordination overhead
Model 2: Virtual Oversight Framework
Concept: Private companies develop capabilities, write operational code, and prepare attacks under Cyber Command oversight, then hand off execution to government operators.
Advantages:
- Dramatically expands development capacity
- Allows government to focus on high-priority missions
- Private sector brings innovation and agility
- Clear separation between development and execution
Challenges:
- Coordination bottlenecks remain
- Government still executes everything
- May not fully solve capacity constraints
- Operational security of handoff process
Model 3: Full Authorization (Requires Legislation)
Concept: Congress passes laws explicitly authorizing private companies to conduct offensive operations under Letters of Marque or similar framework, with strict oversight mechanisms.
Advantages:
- Achieves maximum scale and speed
- Fully leverages private sector capabilities
- Could dramatically expand U.S. cyber offensive capacity
- Market-driven innovation and efficiency
Challenges:
- Massive legal and international complications
- Attribution and escalation management nightmares
- Accountability and liability questions
- Potential for profit-driven mission creep
The Attribution Problem: When Private Becomes Public
The Core Dilemma
One of the most dangerous aspects of private sector offensive operations is the attribution challenge. In cyberspace, determining who conducted an attack is notoriously difficult even when government intelligence agencies are involved. Adding private contractors to the mix creates catastrophic ambiguity.
The escalation ladder:
- Private U.S. company conducts offensive operation against nation-state infrastructure
- Target nation attributes action to U.S. government (reasonably)
- Nation-state retaliates against U.S. government assets or allies
- U.S. must respond to protect credibility and allies
- Escalation spiral potentially leading to kinetic conflict
This scenario is not theoretical. It’s the exact concern that kept offensive cyber operations tightly controlled within military and intelligence agencies for decades.
Historical Parallel: Privateering’s Demise
The Declaration of Paris (1856) abolished privateering precisely because it created uncontrollable escalation risks and diplomatic nightmares. Though the U.S. never signed that declaration, the international community recognized that authorizing private military action at sea was fundamentally destabilizing.
Cyberspace presents even greater challenges:
- Attacks can be launched from anywhere instantly
- Attribution requires sophisticated intelligence analysis
- Private actors lack diplomatic channels to de-escalate
- Speed of cyber operations compresses decision timelines
The Industry Perspective: Opportunity Meets Liability
The Business Case
Many cybersecurity firms possess technical capabilities that could be readily applied to offensive operations. Defensive security skills—network penetration, vulnerability research, exploit development, malware analysis—translate directly to offensive use.
Potential advantages for companies:
- Lucrative government contracts
- New revenue streams beyond traditional cybersecurity
- Opportunity to directly combat adversaries
- Enhanced reputation in national security community
The Liability Calculus
Michael Janke, co-founder of Datatribe (a cyber-focused startup foundry), identifies the stark business risks:
Financial exposure:
- Direct legal liability for actions against foreign entities
- Potential sanctions if operations violate international law
- Insurance complications and exclusions
- Shareholder lawsuits if operations leak or fail
Reputational concerns:
- Offensive operations could alienate commercial customers
- Investor reluctance about legal gray areas
- Difficulty maintaining “dual use” marketing
- Potential for public backlash
Operational risks:
- Direct retaliation from nation-state adversaries
- Targeting by foreign intelligence services
- Compromise of broader company operations
- Employee safety concerns
The Transparency Challenge
Future legislation might require companies to disclose how their tools are used, eliminating the “gray area” that currently allows some flexibility. This transparency could fundamentally undermine the discrete operations many companies prefer for competitive and security reasons.
International Law and Diplomatic Implications
Geneva Conventions and Warfare
The international legal framework for warfare was not designed for cyber privateering. Key questions without clear answers:
Status of private cyber operators:
- Are they lawful combatants under Geneva Conventions?
- What protections do they have if captured?
- What liability do they face under international law?
- How does immunity work for non-governmental actors?
Targeting and proportionality:
- Who determines legitimate military objectives in cyberspace?
- How is proportionality calculated for cyber effects?
- What constitutes excessive collateral damage?
- Who’s liable when cyber operations cause unintended physical harm?
Allied Reactions
NATO allies and other partners may view U.S. cyber privateering with deep concern:
Potential tensions:
- Actions could implicate allies through NATO Article 5
- Erodes trust in U.S. operational control
- Creates precedent other nations may follow
- Complicates intelligence sharing and cooperation
Operational coordination:
- How do allies deconflict with U.S. private operations?
- What notification and coordination protocols apply?
- How are zones of operation negotiated?
- What happens when private operations clash with allied missions?
Adversary Response
If the U.S. authorizes cyber privateering, adversaries will almost certainly follow suit:
China response:
- Already has opaque relationship with private hackers
- Could formalize and expand contractor operations
- Massive technical workforce could be mobilized
- Legal framework even less constraining than U.S.
Russia response:
- Long history of using criminal groups as proxies
- Could legitimize and systematize existing relationships
- Combines technical capability with plausible deniability
- May already operate under similar model informally
The Confirmation Hearing: Lt. Gen. Joshua Rudd’s Role
The Nominee
Lt. Gen. Joshua M. Rudd, currently Deputy Commander of U.S. Indo-Pacific Command, has been nominated to lead both the National Security Agency and U.S. Cyber Command in a dual-hatted capacity. His confirmation hearing took place January 15, 2026, before the Senate Armed Services Committee.
Background concerns:
- Rudd is a Special Forces officer with extensive combat experience
- Notably lacks direct experience in military cybersecurity or signals intelligence
- Selection based on operational experience in Indo-Pacific (China focus)
- Questioned repeatedly about cyber credentials during hearing
Testimony Highlights
Rudd defended his qualifications by emphasizing his consumption and integration of cyber intelligence throughout his career:
“For decades I have had the opportunity to be a leader, consumer, enabler, generator and integrator of the intelligence and operational capabilities of the NSA and Cyber Command.”
Notable exchange with Sen. Angus King (I-Maine):
When asked whether NSA and Cyber Command should develop an offensive cyber deterrence policy, Rudd deflected:
“Senator I don’t know if that’s my role to have that opinion.”
King’s response captured the moment’s significance:
“I’m confused, because you’re nominated to be the top cyber officer in the United States government. And you don’t have an opinion on cyber policy or what’s important? Are you simply a lever puller? I really don’t understand.”
Leadership Context
The NSA and Cyber Command have been without permanent leadership since April 2025, when Gen. Timothy Haugh and Deputy Director Wendy Noble were fired following pressure from far-right activist Laura Loomer. Lt. Gen. William Hartman has served as acting director during this period.
This leadership vacuum during a critical strategic pivot raises significant concerns about institutional knowledge, morale, and effective implementation of any new cyber strategy. The agency has also experienced significant staffing cuts, with an accelerated 8% personnel reduction within 90 days, far exceeding the typical 7% annual retirement rate.
The Timing: Convergence of Threats and Policy
The Salt Typhoon Wake-Up Call
Recent Chinese cyber intrusions, particularly the Salt Typhoon campaign targeting U.S. telecommunications systems, have intensified calls for more aggressive cyber responses. The campaign demonstrated:
- Persistent access to critical infrastructure over years
- Sophisticated operational security evading detection
- Strategic pre-positioning for potential wartime disruption
- Scale and coordination suggesting massive state resources
This urgency for offensive cyber capabilities comes amid controversial operational decisions, including reports that U.S. Cyber Command was ordered to stand down from offensive operations against Russia as part of diplomatic efforts—raising questions about strategic consistency in the administration’s cyber posture.
The Six Pillars
According to multiple sources, the Trump administration’s National Cybersecurity Strategy is organized around six pillars:
- Cyber offense and deterrence - The controversial private sector component
- Regulatory alignment - Harmonizing conflicting regulations
- Workforce development - Addressing talent shortage
- Federal procurement - Improving acquisition processes
- Critical infrastructure protection - Enhancing defensive posture
- Emerging technologies - AI integration and future capabilities
The strategy is expected to be approximately five pages long—dramatically shorter than the Biden administration’s 35-page strategy—and will likely be followed by executive orders for implementation.
Policy Framework Review
The strategy implementation includes plans to reexamine foundational policy frameworks:
NSPM-13 (classified) - Governs which agencies can launch cyber operations and authorization processes
PPD-41 - Defines roles, responsibilities, and coordination for major cyber incidents
NSM-22 - Sets standards for protecting critical infrastructure across sectors
This comprehensive policy review indicates the administration intends deep structural changes, not just incremental adjustments.
Risk Analysis: What Could Go Wrong
Operational Risks
Misidentification and collateral damage:
- Attribution in cyberspace is notoriously difficult
- Private actors may lack intelligence resources for accurate targeting
- Collateral damage from cyber operations can be extensive and unpredictable
- No mechanism to recall or abort operations once launched
Coordination failures:
- Multiple private entities operating simultaneously creates de-confliction nightmares
- Lack of centralized operational awareness
- Potential for friendly fire incidents
- No established protocols for priority and deference
Technical limitations:
- Private companies may lack sophisticated operational security
- Increased attack surface for adversary counterintelligence
- Potential compromise of capabilities through private sector breach
- Reduced operational security discipline compared to military units
Strategic Risks
Escalation management:
- Private sector lacks training and authority for de-escalation
- No diplomatic channels to communicate intent or clarify misunderstandings
- Profit motives may drive toward more aggressive actions
- Compressed decision timelines in fast-moving cyber operations
International precedent:
- Legitimizes similar programs by adversaries
- Erodes international norms against cyber privateering
- Makes negotiation of cyber warfare treaties nearly impossible
- Creates race to the bottom in cyber conflict governance
Domestic security:
- Private companies become legitimate military targets for adversaries
- Employees face personal security risks from foreign intelligence services
- Potential for domestic critical infrastructure targeting in retaliation
- Blurs line between military and civilian targets
Legal and Accountability Risks
Liability questions:
- Who’s responsible when private operations cause unintended harm?
- What insurance covers acts of war conducted by private entities?
- How do war crimes laws apply to contractors?
- What protections exist for employees who refuse unlawful orders?
Oversight challenges:
- Congressional oversight becomes extremely complex
- Classification limits transparency and accountability
- Profit motives create incentives to avoid oversight
- Difficult to audit effectiveness of classified operations
Constitutional concerns:
- Delegation of war powers to private entities
- Due process implications for targeted individuals
- Fourth Amendment concerns about surveillance and data collection
- First Amendment complications if operations target speech or media
Alternative Approaches: What Else Could Work?
Enhanced Government Capacity
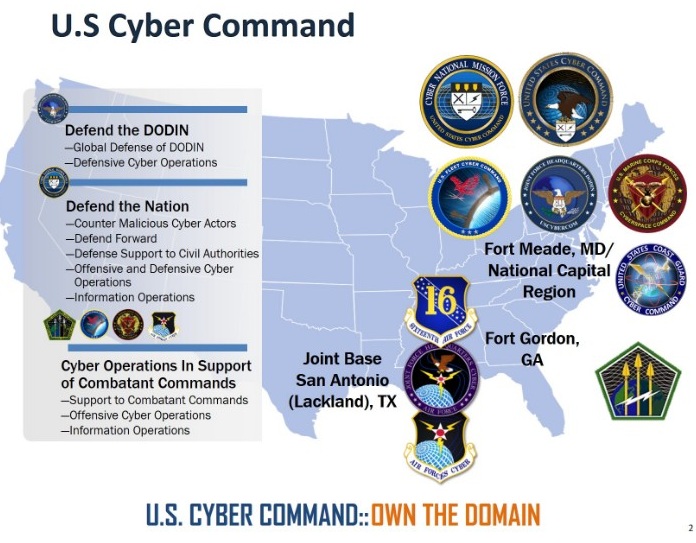
Rather than privatizing offensive operations, focus could shift to dramatically expanding government cyber workforce through existing military cyber structures. The U.S. already maintains comprehensive cyber warfare capabilities across all military branches, from Army Cyber Command’s offensive 780th Military Intelligence Brigade to the Air Force’s 688th Cyberspace Wing and specialized units across all services.
Advantages:
- Maintains accountability and control
- Preserves international law framework
- Reduces escalation risks
- Better integration with intelligence and diplomatic efforts
Challenges:
- Still faces recruitment and retention difficulties
- Slower to scale than private sector approach
- Requires substantial budget increases
- Competitive compensation with private sector
Public-Private Partnerships
Structured collaboration without full privatization:
Threat intelligence sharing:
- Private sector identifies threats and shares data
- Government conducts response operations
- Preserves clear roles and accountability
Capability development:
- Companies develop tools and capabilities
- Government maintains monopoly on use
- Access to innovation without operational privatization
Defensive focus:
- Support critical infrastructure protection
- Enhance attribution capabilities
- Improve incident response
- Stay within defensive legal framework
International Frameworks
Multilateral approach with allies:
Benefits:
- Shared burden among democratic nations
- Legitimacy through collective action
- Better intelligence sharing
- Reduced escalation risk
Structure:
- NATO cyber operations coordination
- Combined cyber commands
- Shared offensive capabilities
- Unified rules of engagement
Industry Impact: Winners and Losers
Potential Beneficiaries
Offensive cyber capabilities firms:
- Specialized penetration testing companies
- Vulnerability research firms
- Exploit development businesses
- Red team operators
Defense contractors:
- Traditional defense companies pivoting to cyber
- Systems integrators
- Command and control platforms
- Training and simulation providers
Cyber intelligence startups:
- Threat intelligence platforms
- Attribution technologies
- Operational security tools
- Analysis and visualization systems
Companies at Risk
Pure-play defensive security:
- May lose customers concerned about offensive associations
- Pressure to pivot toward offensive capabilities
- Reputational challenges
- Talent drain to offensive sector
Cloud and infrastructure providers:
- Become targets for retaliation
- Liability for hosting offensive operations
- International market access complications
- Regulatory challenges in foreign jurisdictions
Market Dynamics
The authorization of private offensive operations would create entirely new market segments:
Emerging markets:
- Cyber privateering as a service
- Offensive operations insurance
- Legal advisory for cyber operations
- Operational security for contractors
Valuations:
- Offensive cyber startups become attractive targets
- Defense contractors gain new growth opportunities
- Pure defensive firms may see valuation pressure
- Consolidation likely as capabilities combine
The Cybersecurity Consultant’s Perspective
Practical Implications for Organizations
For potential contractors:
If your firm possesses offensive capabilities, you face critical decisions:
- Pursue government contracts for offensive operations?
- Conduct thorough legal risk assessment
- Evaluate liability insurance adequacy
- Consider reputational impact on commercial business
- Assess employee safety and security implications
- Establish clear separation between offensive and defensive operations?
- Separate corporate entities
- Different branding and marketing
- Isolated infrastructure and personnel
- Transparent disclosure to customers
- Focus on defensive capabilities and avoid offensive work?
- Potential competitive disadvantage
- May lose talent to offensive opportunities
- Reduces total addressable market
- Maintains lower risk profile
For potential targets:
Organizations should assume they may become collateral damage in cyber operations:
- Enhanced security posture becomes more critical
- Assume advanced persistent threats
- Implement zero-trust architectures
- Segment critical systems aggressively
- Prepare for state-level adversaries
- Incident response planning must account for escalation
- Diplomatic notification protocols
- Legal framework for reporting attacks
- Communication strategies for attribution questions
- Business continuity for extended incidents
- Geographic considerations for infrastructure placement
- Avoid hosting in countries with aggressive cyber programs
- Diversify across jurisdictions
- Consider neutral country locations
- Plan for regulatory fragmentation
Assessment for Clients
As consultants advising clients, we must provide balanced analysis:
Questions to ask:
- Does the client’s threat model include state-sponsored attacks?
- What is the client’s risk tolerance for being caught in crossfire?
- How would the client respond to nation-state attribution questions?
- What insurance coverage exists for acts of cyber war?
- How would operations continue if infrastructure is targeted?
Recommendations framework:
- Assess exposure to cyber operations theater
- Evaluate current security controls against advanced threats
- Implement enhanced monitoring and detection
- Develop incident response plans for state-level threats
- Consider geographic and architectural changes to reduce risk
Conclusion: The Path Forward
The Trump administration’s proposal to enlist private companies in offensive cyberoperations represents one of the most significant shifts in warfare doctrine since the advent of cyber capabilities. The initiative promises to dramatically expand U.S. offensive cyber capacity, potentially providing the scale and persistence needed to deter sophisticated adversaries.
Career Implications for Cybersecurity Professionals
For those in the cybersecurity field, this policy shift creates both opportunities and challenges. Organizations will need professionals who understand offensive cyber operations, legal frameworks, and risk management. Security professionals must continuously evolve their skills to meet these changing demands, whether through specialized certifications, hands-on experience with emerging tools, or staying ahead of generational shifts in the industry.
However, the risks are equally dramatic:
Legal complexity requiring congressional action and international legal framework development
Attribution challenges that could lead to unintended escalation with nuclear-armed adversaries
Accountability gaps in operations conducted by profit-driven entities
Precedent setting that legitimizes similar programs by authoritarian regimes
Operational chaos from inadequate coordination and deconfliction
The Critical Questions
As this policy develops, several fundamental questions demand answers:
- Can private entities conduct offensive operations without creating unacceptable escalation risks?
- What oversight mechanisms can provide adequate accountability while maintaining operational security?
- How will international law evolve to address cyber privateering?
- What happens when adversaries adopt similar approaches?
- Who bears liability when operations cause unintended harm?
Recommendations
Based on this analysis, several principles should guide policy development:
If privatization proceeds:
- Maintain strict oversight through Cyber Command control
- Establish clear accountability mechanisms and liability frameworks
- Develop international legal frameworks before major operations
- Implement robust coordination to prevent chaos
- Create sunset provisions allowing policy reassessment
Alternative approaches to consider:
- Dramatically expand government cyber capabilities instead
- Focus private sector on capability development, not execution
- Build multinational offensive cyber coalitions with allies
- Prioritize defensive measures and resilience
- Invest in attribution technologies to enable proportionate response
The Stakes
Lt. Gen. Moore’s warning bears repeating: “If you just have companies out there hacking back, what you end up with is potential chaos in the environment.”
The question is whether the potential benefits of scaled offensive operations outweigh the substantial risks of chaos, escalation, and the erosion of the already fragile norms governing cyber conflict.
As Lt. Gen. Rudd’s confirmation proceeds and the National Cybersecurity Strategy nears release, these are not academic questions. The decisions made in the coming months will shape cyber conflict for decades and potentially determine whether the digital domain becomes a space of persistent low-intensity warfare or spirals into something far more dangerous.
The cybersecurity community, Congress, and the American public must engage seriously with these questions now, before operational realities make reversal impossible.
Sources and References
- The New York Times, “U.S. Weighs Expanding Private Companies’ Role in Cyberwarfare” (January 14, 2026)
- Bloomberg News, “Trump Administration Turning to Private Firms in Cyber Offensive” (December 12, 2025)
- Nextgov/FCW, “Trump admin to revisit bedrock cyber policies as it implements new strategy” (December 15, 2025)
- CyberScoop, “Five-page draft Trump administration cyber strategy targeted for January release” (December 4, 2025)
- Vanderbilt Institute of National Security, Moore & Goldstein report on private sector cyber operations
- U.S. Naval Institute Proceedings, “Grant Cyber Letters of Marque to Manage ‘Hack Backs’” (October 2019)
- The Register, “Bill would give hackers letters of marque against US enemies” (August 21, 2025)
- DefenseScoop, “Trump nominates Army general to lead Cyber Command, NSA” (December 18, 2025)
- Federal News Network, “Five things to watch in cybersecurity for 2026” (January 12, 2026)
- Lawfare, “Pirates, Privateers, and Cartels: Why Profit-Driven Policing Backfires” (March 11, 2025)
Related Reading on Security Careers Help
For more context on the Trump administration’s cybersecurity policies and related topics:
- Trump’s $1 Billion Cyber Gambit: America’s Dangerous Shift from Defense to Offense - Analysis of the controversial budget reallocation favoring offensive operations over defensive programs
- Reshaping America’s Digital Defense: Trump Administration’s Sweeping Changes to Intelligence and Cybersecurity Leadership - Comprehensive overview of leadership turnover at NSA, Cyber Command, and other agencies
- Implications of US Cyber Command Standing Down from Operations Against Russia - Strategic analysis of the controversial decision to halt offensive cyber operations against Russia
- U.S. Army Cyber Divisions and Psychological Operations Units: A Comprehensive Overview - Detailed breakdown of existing military cyber warfare capabilities
- Building Cyber Warriors: The Imperative of the Evolving Cyber Professional - Career development guidance for cybersecurity professionals in a rapidly changing landscape
- Artificial Intelligence (AI) is Revolutionizing Cybersecurity Operations - How AI integration impacts CISOs and security operations centers
This analysis represents independent research and commentary. Views expressed are those of the author and do not represent official policy positions.
Last Updated: January 15, 2026
Version: 1.0