The Trump administration is preparing to fundamentally reshape America’s approach to cybersecurity, moving away from a primarily defensive posture to actively targeting nation-state hackers before they can strike U.S. infrastructure and critical systems.
A Strategic Pivot
Sean Cairncross, the administration’s national cyber director, recently announced that the forthcoming National Cyber Strategy represents a significant departure from previous approaches. Rather than focusing solely on hardening defenses and responding to breaches after they occur, the new strategy emphasizes proactive operations designed to impose “real-world costs” on adversaries who target American infrastructure and critical systems.
This shift reflects a growing recognition that purely defensive cybersecurity measures have proven insufficient against sophisticated nation-state actors. The strategy being developed in collaboration with the FBI aims to deter attacks by demonstrating that intrusions will trigger offensive responses.
Related: Trump’s $1 Billion Cyber Gambit: America’s Dangerous Shift from Defense to Offense
The Evolution of U.S. Cyber Doctrine
The move toward offensive cyber operations isn’t entirely new, but it represents a formalization and expansion of tactics that have been developing over recent years. Previous administrations laid groundwork for more aggressive cyber postures, including:
- The 2018 National Cyber Strategy under the first Trump administration, which emphasized “defend forward” operations
- The rescission of Presidential Policy Directive 20 (PPD-20), which had required interagency approval for offensive cyber operations
- U.S. Cyber Command’s evolution from a supporting to a fully operational combatant command
However, the current administration appears poised to take these concepts further, making offensive operations a cornerstone rather than a complement to defensive measures. As detailed in our analysis of Reshaping America’s Digital Defense, these changes represent one of the most significant overhauls of the U.S. national security establishment in decades.
What “Going on Offense” Actually Means
Offensive cyber operations can take several forms, each with different implications:
Persistent Engagement
This involves continuously operating in adversary networks to understand their capabilities, disrupt their operations, and create uncertainty about what actions might trigger U.S. response. U.S. Cyber Command has previously described this as “defending forward,” maintaining a presence in adversary infrastructure to prevent attacks at their source.
Disruption Operations
These include technical actions to degrade or disable adversary capabilities, such as taking down command-and-control servers, corrupting malware before deployment, or interfering with hacking infrastructure.
Information and Psychological Operations
Modern offensive cyber strategy extends beyond technical operations to include information warfare and psychological operations (PSYOPS). As explored in our analysis of The Silent War: Psychological Operations from the KGB to TikTok, these operations weaponize social media and digital platforms to influence public opinion, sow discord, and undermine adversary capabilities.
The U.S. government has increasingly recognized the importance of the information domain, as evidenced by The White House Influencer Pipeline: How the Biden Administration Revolutionized Government Communications Through Social Media. This approach represents a departure from traditional government communications, leveraging social media influencers and digital platforms as part of a broader strategic communications strategy.
However, these capabilities raise concerns about domestic surveillance and the boundaries of government authority. The Signature Scandal America Isn’t Talking About: When Trusted Insiders Forge Executive Authority demonstrates how insider access to sensitive government systems can be exploited, highlighting vulnerabilities that exist even at the highest levels of authority.
Deterrence Through Attribution and Consequences
Beyond technical measures, offensive strategy includes publicly attributing attacks, imposing economic sanctions, indicting foreign hackers, and conducting operations that demonstrate U.S. capabilities.
Hunt Forward Operations
These involve deploying U.S. cyber teams to partner nations’ networks to identify and neutralize threats targeting both those countries and American interests.
The Rationale Behind the Shift
Several factors are driving this strategic evolution:
Escalating Nation-State Threats
Chinese, Russian, Iranian, and North Korean cyber operations have grown increasingly bold, targeting everything from critical infrastructure to intellectual property. As documented in our comprehensive Briefing on the 2025 Cybersecurity Landscape, Q1 2025 data revealed a 47% year-over-year increase in weekly cyber attacks per organization and a 126% surge in ransomware incidents.
Recent high-profile incidents underscore the escalating threat:
- The F5 breach exposed nation-state actors maintaining long-term access to critical cybersecurity infrastructure
- Russian-linked attacks on federal court systems potentially exposed confidential informant identities and sealed case documents
- Chinese state-sponsored Salt Typhoon group maintained nine-month undetected access to U.S. Army National Guard networks
The Failure of Pure Defense
Sophisticated attackers maintain inherent advantages—they need to succeed only once, while defenders must succeed constantly. The expanding attack surface created by cloud computing, IoT devices, and interconnected supply chains makes comprehensive defense increasingly challenging.
The Collins Aerospace ransomware attack demonstrated how critical infrastructure vulnerabilities can cascade across international systems, bringing major European airports to their knees.
Strategic Competition
As cyber capabilities become central to geopolitical competition, nations that demonstrate credible offensive capabilities may deter adversaries more effectively than those relying solely on defensive postures.
Challenges and Risks
While the offensive pivot may address some cybersecurity gaps, it introduces significant challenges:
Escalation Dynamics
Offensive cyber operations risk triggering cycles of retaliation, potentially escalating conflicts in ways that are difficult to control or predict. Unlike kinetic weapons, cyber capabilities are easily copied and adapted by adversaries.
Attribution Complexity
Definitively attributing cyber attacks to specific actors remains technically and politically challenging. Taking offensive action based on uncertain attribution could target the wrong parties or be exploited by adversaries using false flag operations.
Private Sector Coordination
Most critical infrastructure is privately owned, creating coordination challenges. The massive Drift supply chain attack that compromised over 700 companies—including major cybersecurity vendors like Palo Alto Networks and Zscaler—demonstrates how third-party integrations create expanded attack surfaces that complicate offensive operations.
Companies may be uncomfortable with offensive operations launched from or through their networks, and legal frameworks around private sector involvement in offensive operations remain murky.
International Norms and Law
The application of international law to cyber operations remains contested. Aggressive offensive operations could undermine U.S. efforts to establish international norms around responsible state behavior in cyberspace.
Domestic Infrastructure Vulnerabilities
Pursuing offensive operations while domestic critical infrastructure remains vulnerable creates strategic contradictions. As detailed in our analysis of cyber threats to water infrastructure, even basic critical systems lack adequate protection. Adversaries may perceive U.S. offensive actions as justification for their own attacks on American infrastructure.
Privacy and Civil Liberties Concerns
The expansion of offensive cyber capabilities raises significant questions about surveillance, privacy, and civil liberties. As detailed in How Governments, Intelligence Agencies, and Shadow Actors Are Weaponizing Your Mind, the boundary between foreign intelligence operations and domestic surveillance can become blurred.
When offensive operations require maintaining persistent access to global networks and communication platforms, there’s an inherent risk of overreach that could impact American citizens’ privacy. The infrastructure used for offensive operations against foreign adversaries often overlaps with systems used by U.S. citizens, creating potential Fourth Amendment concerns and accountability questions.
The Information Warfare Dimension
Modern offensive cyber strategy cannot be separated from information warfare and influence operations. The digital battlefield now extends beyond networks and servers to include social media platforms, messaging apps, and the information ecosystem itself.
Social Media as a Weapon System
As documented in our analysis of psychological operations from the KGB to TikTok, adversaries have weaponized social media platforms to conduct sophisticated influence operations. The U.S. shift to offensive cyber strategy must account for this reality, but it also raises questions about where legitimate government communications end and propaganda begins.
The Biden administration’s approach to revolutionizing government communications through social media influencers demonstrated how governments are adapting to the digital information environment. The Trump administration’s offensive cyber strategy will likely build on these foundations while potentially taking more aggressive stances toward adversary information operations.
The Blurred Lines of Digital Influence
The challenge lies in distinguishing between:
- Defensive counter-messaging: Combating foreign disinformation campaigns
- Offensive information operations: Conducting influence campaigns against adversary populations
- Domestic strategic communications: Shaping public opinion within the United States
These activities often use similar tools, platforms, and techniques, making oversight and accountability particularly challenging. When offensive cyber operations include information warfare capabilities, the risk of those tools being turned inward—whether intentionally or inadvertently—becomes a legitimate concern.
Accountability and Oversight
The Signature Scandal revealed how even high-level government processes can be compromised by insiders with malicious intent or poor judgment. When offensive cyber capabilities are concentrated in government agencies, robust oversight mechanisms become essential to prevent abuse.
Questions that remain unresolved:
- What oversight mechanisms exist for offensive information operations?
- How are domestic impacts assessed before launching operations?
- What legal frameworks govern the use of offensive cyber tools against foreign targets when those operations may affect Americans?
- How is success measured in information warfare without reliable feedback loops that might enable mission creep?
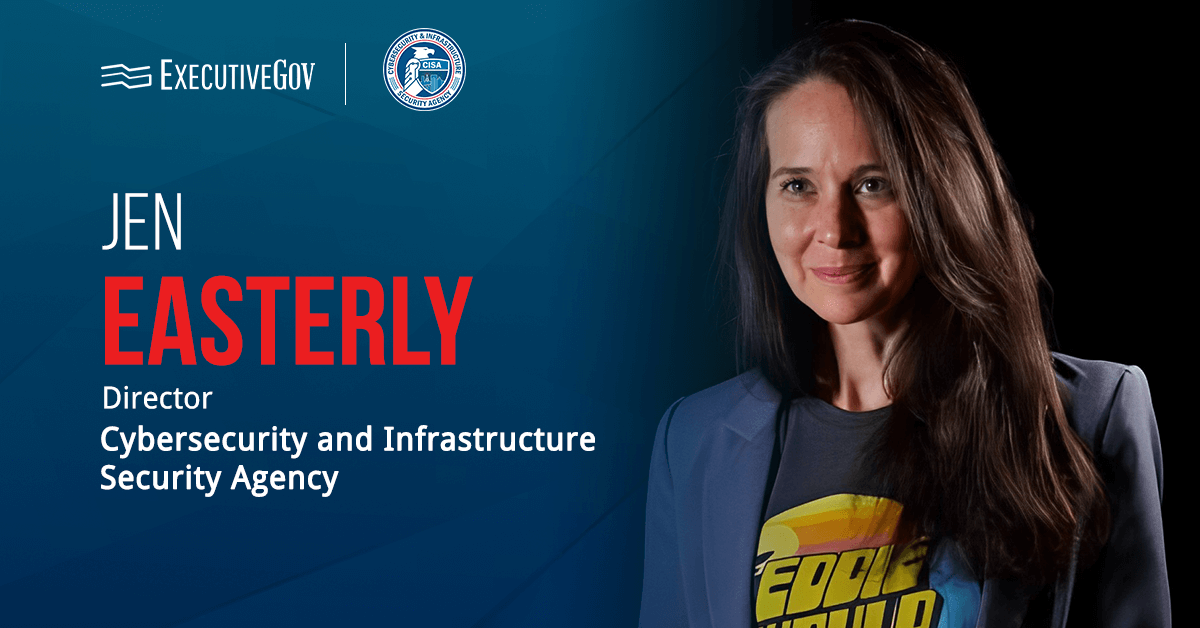
CISA’s Role in the New Strategy
The Cybersecurity and Infrastructure Security Agency (CISA) finds itself at a critical juncture. Under the new administration, CISA has experienced substantial personnel cuts and mission changes, with Homeland Security Secretary Kristi Noem describing some of the agency’s previous work as “off mission.”
Despite budget pressures and the $1 billion shift from defensive to offensive operations, CISA continues to provide essential services:
- Issuing emergency directives for critical vulnerabilities
- Maintaining the Known Exploited Vulnerabilities (KEV) catalog
- Coordinating incident response for critical infrastructure
- Providing threat intelligence to state and local governments
The proposed Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) final rules, expected in late 2025, will mandate that critical infrastructure entities report significant cyber incidents to CISA within 72 hours and ransomware payments within 24 hours—a key defensive capability that must be maintained even as the strategy shifts toward offense.
What This Means for Organizations
For businesses, particularly those in critical infrastructure sectors, this strategic shift has several implications:
Increased Threat Environment
As the U.S. adopts more aggressive cyber postures, adversaries may respond with escalated operations against American targets. Organizations should prepare for potentially increased attack volumes and sophistication.
The targeting of luxury brands like Louis Vuitton and Dior, and the sophisticated attacks on cybersecurity professionals themselves, demonstrate that no sector is immune.
Enhanced Government-Private Partnerships
The offensive strategy will likely require deeper collaboration between government agencies and private sector entities for threat intelligence sharing, coordinated response, and potentially using private infrastructure for offensive operations.
Regulatory Evolution
New legal frameworks may emerge to support offensive operations, potentially including requirements for private sector cooperation, liability protections for companies involved in government cyber operations, or new reporting obligations.
Investment Priorities
Organizations should continue strengthening fundamental security controls even as national strategy shifts toward offense. Basic cyber hygiene, network segmentation, zero trust architectures, and incident response capabilities remain essential regardless of government strategy.
The Insider Threat Dimension
As the U.S. pursues offensive operations, insider threats become even more critical. Recent cases highlight this risk:
- Peter Williams, former L3Harris executive, allegedly sold offensive cyber capabilities to Russia for $1.3 million
- Maxwell Schultz case demonstrated how terminated contractors can cause massive damage
- Jack Teixeira’s Air National Guard leak of classified documents exposed vulnerabilities in military security
These incidents underscore that offensive capabilities are only as secure as the people with access to them—a challenge that becomes more acute as the U.S. expands its offensive operations.
Looking Ahead
The success of an offensive cyber strategy depends on several factors: maintaining technological superiority, establishing clear rules of engagement, coordinating across government agencies and international partners, and balancing offensive operations with continued defensive investments.
The strategy also requires transparency—at least to Congress, allies, and the private sector—about authorities, oversight mechanisms, and decision-making processes for offensive operations. Without appropriate guardrails, offensive cyber operations risk creating more problems than they solve.
As the National Cyber Strategy takes shape, security leaders should monitor several developments:
- Publication of the formal strategy document and its specific operational frameworks
- Legislative proposals providing authorities or oversight for offensive operations
- Changes to federal cybersecurity requirements for critical infrastructure
- Evolution of information sharing programs between government and private sector
- International responses to more aggressive U.S. cyber posture
- Budget allocations between offensive and defensive capabilities
- CISA’s evolving role in the new strategic framework
Practical Recommendations
Organizations should take concrete steps to prepare:
Immediate Actions (0-3 Months)
- Review and update incident response plans
- Strengthen basic security controls and cyber hygiene
- Implement or enhance network segmentation
- Conduct tabletop exercises for nation-state attack scenarios
- Review third-party vendor security requirements
Medium-term Initiatives (3-12 Months)
- Adopt zero trust architecture principles
- Enhance threat intelligence capabilities
- Develop relationships with CISA and relevant ISACs
- Implement enhanced monitoring for insider threats
- Conduct comprehensive supply chain risk assessments
Strategic Planning (12+ Months)
- Develop long-term resilience strategies
- Invest in security team capabilities and training
- Plan for regulatory compliance under evolving requirements
- Build relationships with government partners
- Consider cyber insurance and risk transfer mechanisms
🎧 Related Podcast Episode
Conclusion
The shift toward offensive cyber operations represents a significant evolution in U.S. national security strategy. Whether it effectively deters adversaries while avoiding dangerous escalation will depend on careful implementation, robust oversight, and sustained investment in both offensive capabilities and fundamental defenses.
For organizations navigating this changing landscape, maintaining strong security fundamentals while preparing for an increasingly contested cyber environment remains the most prudent approach. The goal should be resilience—the ability to withstand, respond to, and recover from cyber attacks regardless of their source or sophistication.
As we’ve seen throughout 2025, from ransomware attacks hitting multiple sectors daily to supply chain compromises affecting hundreds of companies, the threat landscape continues to evolve rapidly. The offensive cyber strategy is one piece of a larger puzzle—but it’s a piece that will shape the cybersecurity landscape for years to come.
Additional Resources
Related Articles from the CISO Marketplace Network
Policy and Strategy:
- Trump’s $1 Billion Cyber Gambit: America’s Dangerous Shift from Defense to Offense
- Reshaping America’s Digital Defense: Trump Administration’s Sweeping Changes
Information Warfare and Psychological Operations:
- The Silent War: Psychological Operations from the KGB to TikTok
- The White House Influencer Pipeline: How the Biden Administration Revolutionized Government Communications
- The Signature Scandal America Isn’t Talking About: When Trusted Insiders Forge Executive Authority
Privacy and Surveillance:
- The Complete Guide to Social Media Privacy Protection: Secure Your Digital Life
- Your Complete Guide to Personal Privacy Tools & Strategies
Threat Landscape:
- Who’s Been Getting Hacked? A Look at Major Cyberattacks in Late 2025
- Briefing on the 2025 Cybersecurity Landscape: Key Threats, Trends, and Incidents
Critical Infrastructure:
- Breaking Down the Collins Aerospace Cyber-Attack: A Wake-Up Call for Aviation Security
- The Rising Tide of Cyber Threats: How Hackers Are Targeting Global Water Infrastructure
Government Targets:
- Russia-Linked Cyberattack Exposes Critical Vulnerabilities in Federal Court Systems
- National Guard Under Siege: Comprehensive Analysis of Cybersecurity Breaches
Insider Threats:
- Former L3Harris Cyber Executive Charged with Selling Trade Secrets to Russia
- Former IT Contractor Pleads Guilty to $862K Revenge Hack
Assessment Tools
- Security Team Risk Assessment Tool
- Social Media Risk Assessment Tool
- US State Breach Notification Requirements Tracker
This analysis is based on publicly available information about the evolving National Cyber Strategy and does not reflect classified details about specific offensive cyber programs or operations.
For cybersecurity consulting services, visit CISO Marketplace or explore our network of resources at Security Careers Help, Breached Company, and My Privacy Blog.