The cybersecurity community has been waiting with anticipation, and it’s finally here: the OWASP Top 10 2025 has been released as a release candidate, marking the first major update since 2021. This isn’t just another incremental refresh—it represents a fundamental shift in how we understand and address application security risks in an increasingly complex digital ecosystem. After analyzing data from over 2.8 million applications spanning 589 Common Weakness Enumerations (CWEs), OWASP has delivered a framework that reflects the harsh realities of modern software development and the sophisticated threats we face today.
The Methodology Behind the Madness
Before diving into the changes, it’s crucial to understand what makes the OWASP Top 10 2025 different from its predecessors. The project team made several methodological improvements that enhance both the accuracy and relevance of the list:
Data-Driven with Community Insight: The 2025 edition analyzed contributed data from security vendors, consultancies, bug bounty programs, and organizational contributions—a massive increase from the 400 CWEs examined in 2021 to 589 CWEs in 2025. However, recognizing that data alone can’t capture emerging threats, OWASP continues to reserve two spots for community-identified risks through surveys.
Root Cause Over Symptoms: A deliberate shift toward identifying root causes rather than symptoms. For example, instead of focusing on “Sensitive Data Exposure” (a symptom), the list emphasizes “Cryptographic Failures” (the root cause). This approach provides more actionable guidance for remediation.
CVE-Enhanced Risk Assessment: The team downloaded CVE data with CVSS scores to calculate average exploit and impact metrics for each CWE category. With approximately 175,000 CVE records (up from 125,000 in 2021) mapped to 643 unique CWEs, the risk assessment is more comprehensive than ever.
Breaking Down the OWASP Top 10 2025
A01:2025 - Broken Access Control: Still the Reigning Champion
Broken Access Control maintains its #1 position, and the numbers explain why. The contributed data indicates that 3.73% of applications tested had one or more of the 40 CWEs in this category—but that statistic barely scratches the surface of the real-world impact.
Access control vulnerabilities allow users to act outside their intended permissions, leading to unauthorized information disclosure, modification, or destruction of data. The category encompasses several critical vulnerability types:
- Insecure Direct Object References (IDOR): Despite being well-documented for over a decade, IDOR vulnerabilities continue to plague modern applications. Recent analysis suggests these vulnerabilities accounted for a significant portion of breaches in 2024, with researchers discovering flaws that allowed attackers to alter API connections across multiple organizations.
- Privilege Escalation: Both horizontal (accessing another user’s resources at the same privilege level) and vertical (elevating privileges to administrator level) remain common attack vectors.
- Server-Side Request Forgery (SSRF): Now rolled into this category, SSRF vulnerabilities enable attackers to induce server-side applications to make requests to unintended locations.
Real-World Impact: The T-Mobile API breach in January 2023 exposed 37 million customers’ personal data through an exposed API endpoint without proper authentication. More recently, access control exploits accounted for nearly 80% of crypto hacks in 2024, according to the Hacken Web3 Security Report, demonstrating that these vulnerabilities transcend traditional web applications.
The Agentic AI Amplification: As we enter the era of autonomous AI agents, broken access control risks are poised to explode. When AI systems can independently make decisions and access resources on behalf of users, every authorization failure becomes a potential catastrophe. An AI agent with incorrectly configured permissions could autonomously exfiltrate data, modify critical systems, or grant itself elevated privileges—all without direct human intervention.
Why It Persists: Several factors contribute to the continued prevalence of access control issues:
- Complexity of Modern Applications: Microservices architectures, API gateways, and distributed systems create multiple enforcement points where access control can fail
- Manual Testing Required: Automated tools struggle to detect authorization logic flaws, requiring creative manual security testing
- Development Speed vs. Security: The rush to deliver features often overshadows security considerations, with developers skipping proper access control implementation for each endpoint
A02:2025 - Security Misconfiguration: Rising to #2
Security Misconfiguration has surged from #5 in 2021 to #2 in 2025, and this upward trajectory should surprise no one. Approximately 3.00% of tested applications had one or more of the 16 CWEs in this category. As software engineering increasingly relies on configuration-driven behavior, the attack surface for misconfigurations has expanded exponentially.
The Modern Misconfiguration Crisis: Recent research reveals the staggering scale of this problem:
- 83% of organizations dealt with at least one cloud security incident in 2024
- 80% of ransomware attacks exploit misconfigurations
- Cloud misconfigurations were involved in nearly 25% of cloud security incidents in 2024
- The average cost of a misconfigured cloud setting: $4.24 million per incident
- 65% of cloud network security incidents result from user errors and misconfigurations
Common Misconfiguration Vectors:
- Default Credentials and Settings: Systems deployed with unchanged default usernames, passwords, and configurations remain one of the easiest entry points for attackers.
- Excessive Permissions: The 2024 Snowflake breach exemplified this perfectly. Attackers didn’t need to break Snowflake’s infrastructure—they simply exploited customer accounts lacking multi-factor authentication, network restrictions, and proper credential rotation. Over 165 customers were affected because basic security configurations weren’t enforced.
- Publicly Accessible Storage: Datadog’s State of Cloud Security 2024 report found that 1.48% of AWS S3 buckets are effectively public. In one high-profile case, Blue Shield of California exposed sensitive member data for nearly three years due to an improper link between Google Analytics and Google Ads.
- API Misconfigurations: In Spring 2024, CBIZ left a misconfigured API endpoint exposed without authentication controls for three months, resulting in approximately 36,000 sensitive personal and financial client records being compromised.
- Overly Permissive Network Rules: Verizon’s 2024 DBIR notes that errors, including misconfigurations, account for nearly 30% of breaches, often traced back to lax network rules allowing 0.0.0.0/0 ingress.
The Cloud Complexity Factor: As organizations migrate to cloud-native architectures, the configuration landscape becomes increasingly complex. Multi-cloud strategies, containerization, Infrastructure-as-Code (IaC), and serverless computing all introduce new configuration parameters that must be correctly set and continuously monitored. Each misconfiguration becomes a potential entry point for attackers.
Emerging Threat - Model Context Protocol (MCP): As we enter 2025, new technologies bring new misconfiguration risks. MCP, a mechanism for AI platforms to connect to external systems, is already showing vulnerabilities including token theft, prompt injection attacks, and direct server compromise. Securing external-facing MCP servers represents a major undertaking that security teams can easily get wrong.
A03:2025 - Software Supply Chain Failures: The New Perimeter
Software Supply Chain Failures represents a significant expansion from 2021’s “Vulnerable and Outdated Components.” This category was overwhelmingly voted as a top concern in the community survey, and for good reason—it reflects how modern software is actually built and attacked.
The category encompasses compromises occurring within or across the entire ecosystem of software dependencies, build systems, and distribution infrastructure. With only 5 CWEs mapped but the highest average exploit and impact scores from CVEs, this category represents low-frequency, high-impact threats that keep CISOs awake at night.
The Supply Chain Attack Surge: The data paints a concerning picture:
- Software supply chain attacks doubled in 2024
- 75% of all software supply chains reported attacks in 2024
- Gartner predicts 45% of organizations will experience a software supply chain attack by 2025
- The global annual cost is projected to reach $138 billion by 2031, up from $60 billion in 2025
- From October 2024 to May 2025, supply chain attacks increased to just over 16 per month, up from under 13 per month in the previous period
Recent High-Profile Attacks:
- XZ Utils Backdoor (2024): This sophisticated, likely nation-state-backed operation demonstrated the “benevolent stranger” playbook. Attackers spent two years gaining trust within the project through social engineering, gradually introducing encrypted malicious code into binary test files. They were just days away from having this compromised version deployed to major Linux distributions globally.
- SolarWinds Legacy: The 2020 SolarWinds attack, where attackers embedded malicious code (Sunburst) into software updates distributed to thousands of government agencies and corporations, continues to influence how we think about supply chain security.
- npm Package Hijacking (September 2024): The Chalk and Debug library compromise represented one of the largest supply chain attacks yet. While the financial impact was limited (approximately $600 in stolen cryptocurrency), the incident forced thousands of engineering and security teams to spend countless hours cleaning compromised environments.
- Lazarus Group Campaigns (2024-2025): The North Korean state-sponsored group has repeatedly targeted open-source registries, embedding backdoors and stealers in npm and PyPI packages aimed at cryptocurrency firms and defense contractors.
Why Supply Chain Attacks Are Effective:
- Trusted by Default: Dependencies and build tools operate within inherently trusted environments, allowing malicious code to bypass traditional security controls.
- Amplification Effect: A single malicious dependency can propagate through CI/CD systems, containers, and cloud environments within hours, affecting potentially millions of downstream users.
- Detection Challenges: Traditional security scanners often miss supply chain compromises because the malicious code is deliberately obfuscated or hidden in legitimate-looking updates.
- Human Factor: Open-source projects, often maintained by volunteers, become targets through social engineering. Attackers gain trust, become contributors, and eventually maintainers—positioning themselves to inject malicious code.
Emerging Vectors: The supply chain attack surface continues to expand:
- AI Coding Assistants: Tools like GitHub Copilot, while improving productivity, can introduce vulnerabilities or even malicious code suggestions
- Malicious IDE Extensions: Extensions that modify source code, assets, or build pipelines can silently trojanize development environments
- Machine Learning Models: Malicious actors can poison LLMs and generative AI, or exploit the pickle format used by PyTorch to execute arbitrary Python code when models are loaded
The Build System Battleground: Modern attacks increasingly target the build pipeline itself rather than the final product. Compromising build systems allows attackers to inject malicious code that gets automatically included in every build, affecting all downstream users without ever touching the source repository.
A04:2025 - Cryptographic Failures: Falling but Still Critical
Cryptographic Failures drops from #2 to #4, but don’t mistake this for decreased importance. With 3.80% of applications showing one or more of the 32 CWEs in this category, cryptographic issues remain a fundamental security concern that often leads to sensitive data exposure or complete system compromise.
Common Cryptographic Failures:
- Use of weak or deprecated algorithms (MD5, SHA-1, DES)
- Insufficient key lengths for current computational capabilities
- Improper key management and storage
- Missing encryption for sensitive data in transit or at rest
- Weak random number generation for cryptographic operations
- Failure to validate certificates properly
The Persistence Problem: Despite decades of guidance on cryptographic best practices, these vulnerabilities persist due to:
- Legacy System Constraints: Older systems may not support modern cryptographic standards
- Implementation Complexity: Cryptography is notoriously difficult to implement correctly
- Performance Trade-offs: Organizations sometimes sacrifice security for performance
- Knowledge Gaps: Many developers lack deep understanding of cryptographic principles
A05:2025 - Injection: Still Dangerous, But Evolving
Injection falls from #3 to #5, representing both progress and shifting attack patterns. This remains one of the most tested categories with 38 CWEs and the greatest number of associated CVEs. The category encompasses a range of issues from Cross-site Scripting (high frequency/low impact) to SQL Injection (low frequency/high impact).
Modern Injection Landscape:
- Traditional SQL injection attacks continue, but modern frameworks provide better protection
- NoSQL injection is rising as organizations adopt document databases
- Command injection through API parameters remains prevalent
- LDAP, XML, and XPath injection persist in enterprise applications
- Server-Side Template Injection (SSTI) affects modern web frameworks
Why It’s Dropping: The decline isn’t due to decreased severity but rather:
- Framework Protection: Modern web frameworks include built-in protections against common injection attacks
- Better Developer Education: Injection vulnerabilities are well-understood, and parameterized queries are now standard practice
- Code Analysis Tools: Static and dynamic analysis tools effectively detect many injection vulnerabilities
A06:2025 - Insecure Design: Threat Modeling Gains Traction
Insecure Design slides from #4 to #6 as organizations increasingly adopt threat modeling and secure design principles. Introduced in 2021, this category focuses on design-level weaknesses requiring threat modeling, secure design patterns, and reference architectures.
Progress Indicators:
- 72% of organizations now empower cybersecurity teams during initial phases of technology investments
- “Secure-by-design” approaches are becoming standard practice
- Threat modeling is no longer optional for critical systems
- Architecture review processes increasingly include security considerations
What Insecure Design Encompasses:
- Missing or ineffective control design
- Failure to establish security requirements
- Lack of threat modeling during design phase
- Insecure business logic that can’t be fixed with implementation changes
- Missing security controls for high-risk operations
A07:2025 - Authentication Failures: The MFA Effect
Authentication Failures maintains #7 position with a slight name change (previously “Identification and Authentication Failures”). The 36 CWEs in this category remain important, but standardized authentication frameworks appear to be having beneficial effects.
Positive Trends:
- Widespread adoption of multi-factor authentication (MFA)
- OAuth 2.0 and OpenID Connect standardization
- Password manager usage increasing
- Passwordless authentication gaining traction
Remaining Challenges:
- Session management vulnerabilities persist
- Weak credential recovery mechanisms
- Insufficient protection against brute force attacks
- Poor implementation of MFA (SMS-based remains vulnerable)
A08:2025 - Software and Data Integrity Failures: The Lower-Level Threat
Software or Data Integrity Failures continues at #8, focusing on failures to maintain trust boundaries and verify integrity at a lower level than supply chain failures. This includes:
- Insecure deserialization vulnerabilities
- CI/CD pipeline compromises
- Auto-update mechanisms without integrity verification
- Insecure deserialization of untrusted data
Critical Distinction: While A03 (Supply Chain Failures) addresses ecosystem-wide compromises, A08 focuses on application-specific integrity issues. Both are essential for comprehensive security.
A09:2025 - Logging & Alerting Failures: Visibility is Security
Logging & Alerting Failures retains #9 position with a name change emphasizing the importance of alerting functionality. The new name recognizes that excellent logging without alerting provides minimal value in identifying security incidents.
The Detection Time Gap: Organizations take an average of 277 days to detect cloud breaches, highlighting the critical importance of effective logging and alerting. Without proper visibility:
- Attacks go undetected for months
- Incident response is delayed or impossible
- Forensic investigation lacks crucial evidence
- Compliance requirements can’t be met
Why It’s Underrepresented: This category will always be underrepresented in data because:
- Logging failures aren’t directly exploitable vulnerabilities
- Testing effectiveness requires sophisticated analysis
- Community survey votes keep it on the list due to its operational importance
A10:2025 - Mishandling of Exceptional Conditions: The New Entry
Mishandling of Exceptional Conditions is new for 2025, containing 24 CWEs focused on improper error handling, logical errors, failing open, and related scenarios stemming from abnormal conditions.
What This Category Addresses:
- Verbose error messages revealing sensitive information
- Systems that “fail open” instead of “fail closed”
- Improper handling of null values or unexpected input
- Race conditions in error handling routines
- Unhandled exceptions leading to denial of service
The Resilience Imperative: This category reinforces that secure software isn’t only about preventing attacks but also about failing safely and predictably when something goes wrong. Many weaknesses previously grouped under “poor code quality” now receive dedicated attention, reflecting a broader cultural shift toward resilience and safe failure modes.
Emerging Concern - DoS Through Exception Abuse: Recent incidents suggest algorithmic DoS attacks exploiting exception handling logic. For example, ReDoS (Regular Expression Denial of Service) attacks trigger catastrophic backtracking in regex engines, consuming extreme CPU time and hanging applications with minimal input.
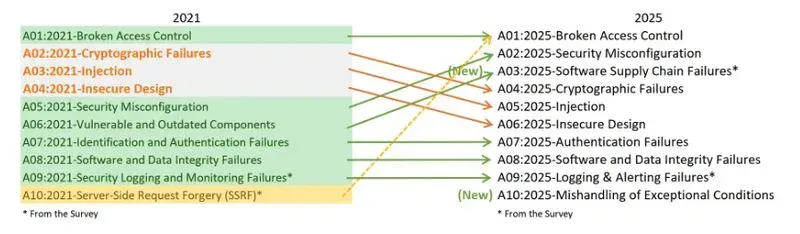
What Changed: The Big Picture
Comparing 2021 to 2025 reveals several significant trends:
- Configuration Over Code: The rise of Security Misconfiguration from #5 to #2 reflects the reality that modern applications are increasingly configuration-driven. As infrastructure-as-code, containerization, and cloud-native architectures dominate, configuration mistakes have become more prevalent and impactful than code vulnerabilities.
- Supply Chain Takes Center Stage: Expanding “Vulnerable and Outdated Components” to “Software Supply Chain Failures” acknowledges that threats extend far beyond outdated dependencies to encompass the entire software development lifecycle, from build systems to distribution infrastructure.
- Root Cause Philosophy: The deliberate focus on root causes over symptoms provides more actionable guidance. Addressing cryptographic failures prevents data exposure; fixing misconfiguration prevents countless exploitation scenarios.
- The Exception Handling Gap: The addition of “Mishandling of Exceptional Conditions” recognizes that how systems fail is as important as how they function. This category addresses a long-overlooked aspect of security: graceful degradation and fail-safe defaults.
- Access Control Dominance: Broken Access Control remaining at #1 for the second consecutive cycle indicates this is a fundamental, persistent challenge in application security that transcends technological evolution.
The Threat Intelligence Perspective
The OWASP Top 10 2025 doesn’t exist in isolation—it reflects broader trends in the threat landscape:
Attack Sophistication: Threat actors increasingly target complex, systemic vulnerabilities rather than simple implementation flaws. Supply chain compromises require months of planning and social engineering. Configuration-based attacks exploit the complexity of modern infrastructure rather than coding mistakes.
AI-Powered Attacks: Artificial intelligence is now a double-edged sword. While defensive AI tools improve detection capabilities, attackers use AI to:
- Automate reconnaissance and vulnerability discovery
- Generate sophisticated phishing campaigns
- Adapt attack tactics in real-time based on defenses encountered
- Identify configuration weaknesses at scale
State-Sponsored Activity: Nation-state actors dominate supply chain attacks, with groups like Lazarus (North Korea) and Midnight Blizzard (Russia) conducting sustained campaigns against critical infrastructure, defense contractors, and cryptocurrency platforms.
Economic Impact: The financial consequences of these vulnerabilities continue to escalate:
- Average data breach cost: $4.88 million globally
- Misconfiguration-related breach: $4.24 million average
- Supply chain attack costs projected to reach $138 billion annually by 2031
- Cloud security incidents affecting 80% of companies in 2024
The SMB Reality Check: Reducing Risk by 90% Without Breaking the Bank
Before diving into enterprise-level implications, it’s worth noting that most organizations—especially small and medium businesses—are flying blind on cybersecurity, assuming they’re fine until it’s too late. One attack can cripple operations, ruin customer trust, and cost far more than prevention.
The harsh reality? You can cut your top cyber risks by nearly 90% using tools you already have from your cloud service provider—with no new spend required. This is particularly relevant when examining the OWASP Top 10 through a practical lens.
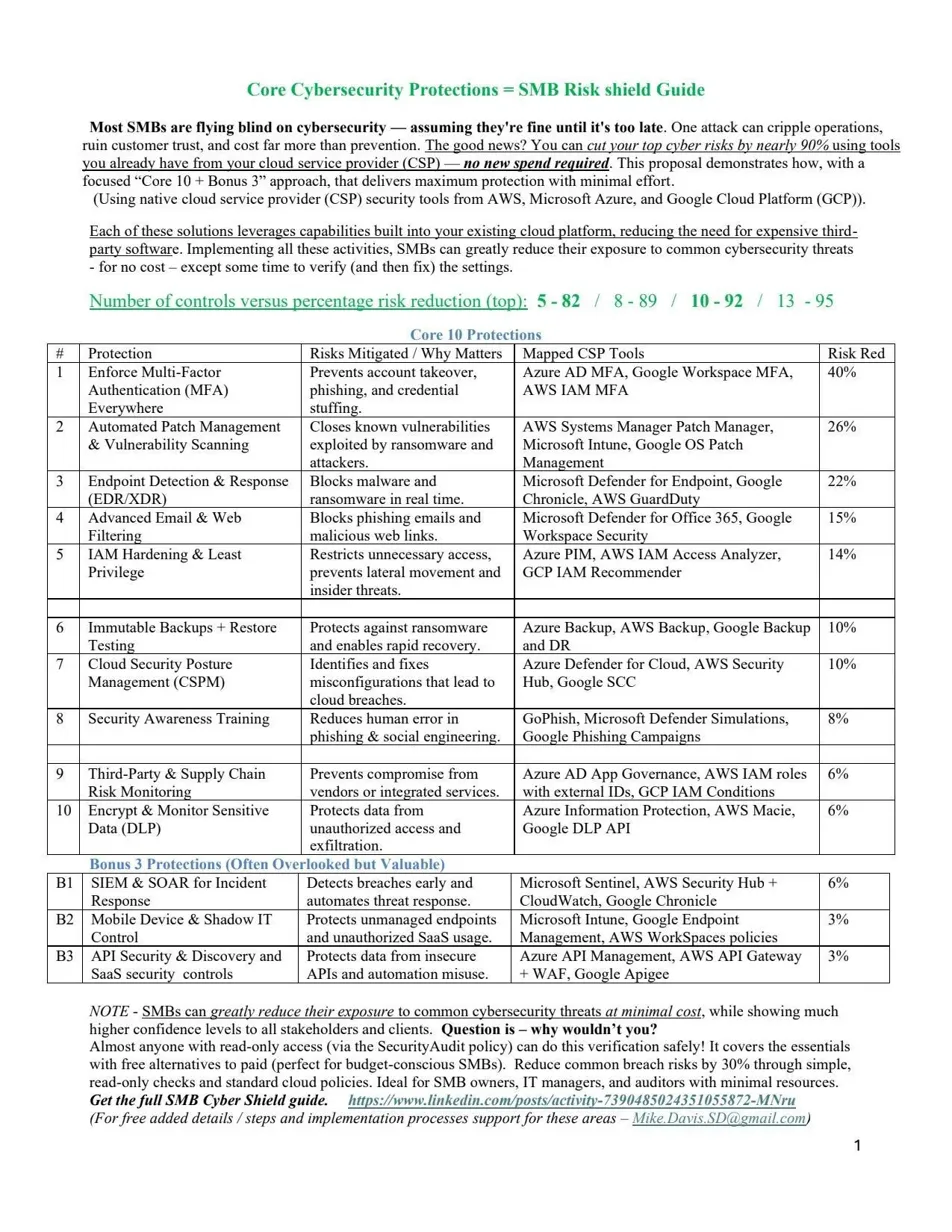
Mapping OWASP Top 10 to Core Security Controls
The connection between theoretical vulnerabilities and practical controls becomes clear when we examine how native cloud platform tools address multiple OWASP categories simultaneously:
A01 - Broken Access Control & A07 - Authentication Failures: Enforcing multi-factor authentication (MFA) everywhere provides 40% risk reduction and directly prevents account takeover, credential stuffing, and unauthorized access. Azure AD MFA, Google Workspace MFA, and AWS IAM MFA are built-in solutions that address the root cause of access control failures.
A02 - Security Misconfiguration: Cloud Security Posture Management (CSPM) tools like Azure Defender for Cloud, AWS Security Hub, and Google SCC provide 10% risk reduction by continuously identifying and helping fix misconfigurations before they become breaches. Given that 80% of ransomware attacks exploit misconfigurations, this represents critical defensive infrastructure.
A03 - Software Supply Chain Failures: Third-party and supply chain risk monitoring through Azure AD App Governance, AWS IAM roles with external IDs, and GCP IAM Conditions provides 6% risk reduction. While this seems modest, remember that supply chain attacks have the highest impact scores—this 6% prevents potentially catastrophic breaches.
A05 - Injection & A08 - Software/Data Integrity: Advanced email and web filtering blocks phishing emails and malicious web links that often deliver injection payloads or compromise software integrity. Microsoft Defender for Office 365 and Google Workspace Security provide 15% risk reduction at this critical entry point.
A09 - Logging & Alerting Failures: SIEM and SOAR tools for incident detection and response (Microsoft Sentinel, AWS Security Hub + CloudWatch, Google Chronicle) detect breaches early and automate threat response, providing 6% risk reduction. More importantly, they transform logging from passive to active defense.
A10 - Mishandling of Exceptional Conditions: Endpoint detection and response (EDR) tools block malware and ransomware in real time, catching the exceptions that exploit improper error handling. Microsoft Defender for Endpoint, Google Chronicle EDR, and AWS GuardDuty provide 22% risk reduction—the second-highest impact after MFA.
The “Core 10 + Bonus 3” Approach
Implementing these controls in a systematic way—what some practitioners call the “Core 10 + Bonus 3” approach—delivers maximum protection with minimal effort:
Core 10 Protections (Total Risk Reduction: 5-82 points on a 100-point scale):
- Multi-Factor Authentication (40% reduction)
- Automated Patch Management (26% reduction)
- Endpoint Detection & Response (22% reduction)
- Advanced Email & Web Filtering (15% reduction)
- IAM Hardening & Least Privilege (14% reduction)
- Immutable Backups + Restore Testing (10% reduction)
- Cloud Security Posture Management (10% reduction)
- Security Awareness Training (8% reduction)
- Third-Party & Supply Chain Risk Monitoring (6% reduction)
- Encrypt & Monitor Sensitive Data (6% reduction)
Bonus 3 Protections (Often Overlooked but Valuable):
- SIEM & SOAR for Incident Response (6% reduction)
- Mobile Device & Shadow IT Control (3% reduction)
- API Security & Discovery (3% reduction)
Why This Matters for OWASP Top 10 Compliance
The power of this approach lies in recognizing that you don’t need expensive third-party software for most protections. Native cloud service provider tools from AWS, Microsoft Azure, and Google Cloud Platform already include these capabilities. By implementing all these activities, SMBs can greatly reduce their exposure to common cybersecurity threats—covering most OWASP Top 10 categories—for no additional cost except the time to configure and verify these controls.
This directly addresses several persistent OWASP challenges:
- Configuration over Code: Proper CSPM prevents the misconfigurations driving A02
- Supply Chain Visibility: Monitoring third-party integrations catches A03 compromises
- Access Control at Scale: IAM hardening and MFA systematically address A01
- Detection Gaps: SIEM and EDR provide the visibility needed for A09
The key insight? Most organizations can achieve 80-90% risk reduction using existing tools, while demonstrating much higher confidence levels to stakeholders, clients, and auditors. Almost anyone with read-only access via a Security Audit policy can verify these controls are properly configured—perfect for budget-conscious SMBs looking to maximize security ROI.
For security leaders wondering where to start with OWASP Top 10 remediation, this framework provides a clear roadmap: focus on the controls that reduce the most risk (MFA, patching, EDR) before moving to more specialized protections.
Practical Implications for Security Programs
The OWASP Top 10 2025 has immediate implications for how organizations should allocate security resources:
1. Prioritize Access Control Reviews
With access control remaining #1, organizations must:
- Implement comprehensive authorization testing in CI/CD pipelines
- Conduct regular access control audits, especially for APIs
- Use both automated tools and manual testing (IDOR requires human analysis)
- Adopt attribute-based access control (ABAC) for complex authorization scenarios
- Prepare for AI-driven authorization challenges
2. Configuration Management as Security
Security misconfigurations demand systematic approaches:
- Implement Infrastructure-as-Code (IaC) with security validation
- Use policy-as-code frameworks to enforce secure configurations
- Deploy cloud security posture management (CSPM) tools
- Conduct regular configuration audits and compliance checks
- Establish secure baseline configurations for all systems
- Automate detection and remediation of misconfigurations
3. Supply Chain Security Maturity
Organizations must mature their supply chain security programs:
- Generate and maintain Software Bills of Materials (SBOMs)
- Implement continuous dependency scanning with prioritized remediation
- Verify digital signatures on all dependencies
- Monitor for compromised packages through threat intelligence
- Secure CI/CD pipelines with strict access controls
- Conduct regular supply chain risk assessments
- Establish vendor security requirements in contracts
- Consider zero-trust principles for build environments
4. Shift Security Left
The rise of design and configuration issues reinforces the “shift left” imperative:
- Integrate threat modeling in design phases
- Conduct architecture security reviews before implementation
- Provide security training for developers and DevOps teams
- Embed security champions within development teams
- Implement security gates in CI/CD pipelines
- Use pre-commit hooks to catch issues before code is committed
5. Detection and Response
With logging and alerting failures at #9, organizations must:
- Implement comprehensive logging across all layers
- Deploy SIEM solutions with proper alert correlation
- Establish clear playbooks for alert response
- Reduce mean time to detect (MTTD) through automation
- Test incident response procedures regularly
- Maintain audit logs meeting compliance requirements
6. Exception Handling Standards
The new #10 category requires:
- Establish secure error handling standards
- Implement fail-secure defaults (fail closed, not open)
- Avoid verbose error messages in production
- Test error handling paths as rigorously as happy paths
- Implement graceful degradation strategies
- Monitor for exceptions that could indicate attacks
Industry-Specific Considerations
Different industries face unique challenges with the OWASP Top 10:
Financial Services: Access control and authentication failures are existential threats. The Verizon DBIR noted that 43% of cloud-infrastructure secrets exposed in public repositories were Google Cloud API keys, with a median remediation time of 94 days.
Healthcare: The 2024 Change Healthcare ransomware attack affected at least 100 million people. Healthcare organizations must prioritize supply chain security given their extensive vendor ecosystems and compliance requirements.
Government: With 88% citing misconfiguration as their top issue, government agencies struggle with basics like access control and encryption despite regulatory oversight.
Cryptocurrency/Web3: Access control exploits accounted for nearly 80% of crypto hacks in 2024, with Web3 projects vulnerable through their Web2 backend infrastructure.
Looking Ahead: 2026 and Beyond
Several trends will likely influence future OWASP Top 10 editions:
AI/ML Security: As AI systems become integral to applications, expect dedicated categories for:
- AI model poisoning and adversarial attacks
- Prompt injection and jailbreak attempts
- AI decision transparency and explainability
- Autonomous agent security and containment
Quantum Computing Threats: As quantum computers advance, cryptographic failures may return to prominence as current encryption standards become vulnerable.
Edge Computing Security: The proliferation of edge computing introduces new attack surfaces requiring specific attention.
Zero Trust Architecture: As zero trust principles become standard, we may see category reorganization reflecting continuous verification rather than perimeter-based security.
Regulatory Pressure: Increasing regulations like the EU’s Cyber Resilience Act will influence how vulnerabilities are categorized and prioritized.
🎧 Related Podcast Episode
Conclusion: The Persistent Challenge
The OWASP Top 10 2025 tells a story of both progress and persistent challenges. While some categories decline due to improved frameworks, education, and tooling, others rise as our infrastructure becomes more complex and distributed.
Three key themes emerge:
- Complexity is the Enemy of Security: As our systems become more complex—with microservices, APIs, cloud-native architectures, and AI integration—the attack surface expands exponentially. Configuration management and supply chain security reflect this reality.
- The Human Element Persists: Many of the top vulnerabilities result from human error: forgotten default credentials, misconfigured permissions, skipped authorization checks, and trusted-but-compromised maintainers. Technical solutions alone won’t solve these problems; they require cultural change, better education, and organizational commitment.
- Security Must Be Foundational: The elevation of design issues and the addition of exception handling emphasize that security can’t be bolted on afterward. It must be considered from the first design meeting through deployment and ongoing operations.
For cybersecurity professionals, the OWASP Top 10 2025 provides a roadmap for resource allocation and program development. For developers, it highlights areas requiring particular attention and care. For executives, it justifies security investments and explains why shortcuts lead to breaches.
The reality is stark: organizations face approximately 1,925 cyberattacks per week in 2025, a 47% increase since 2024. With 83% of organizations experiencing at least one cloud security incident and supply chain attacks doubling year-over-year, the OWASP Top 10 has never been more relevant.
As we enter an era where AI agents autonomously make decisions, where supply chains span thousands of dependencies, and where a single misconfiguration can expose millions of records, the fundamentals matter more than ever. The OWASP Top 10 2025 reminds us that while technology evolves, the principles of secure design, least privilege, defense in depth, and continuous verification remain timeless.
The question isn’t whether your organization will face these vulnerabilities—it’s whether you’ll discover them before attackers do.
This analysis synthesizes data from the OWASP Top 10 2025 Release Candidate, recent cybersecurity research, breach reports, and threat intelligence. As the final version is released in early 2025, expect refinements to categories and CWE mappings based on community feedback.
Key Takeaways:
- Broken Access Control remains #1 for good reason—it’s prevalent, impactful, and will worsen with AI
- Security Misconfiguration surging to #2 reflects the reality of configuration-driven modern infrastructure
- Software Supply Chain Failures deserves its prominence as attacks double and sophistication increases
- The addition of Mishandling of Exceptional Conditions highlights the importance of failing safely
- Organizations must shift from reactive vulnerability management to proactive secure design
- Supply chain security, configuration management, and authorization testing deserve increased investment
- The human element—training, awareness, and culture—remains as important as technical controls
About the CISO Marketplace Network: We track application security trends across our comprehensive ecosystem including breached.company, compliancehub.wiki, and microsec.tools, providing CISOs and security professionals with actionable intelligence for protecting their organizations.