In a controversial 2-1 decision that has sent shockwaves through the cybersecurity community, the Federal Communications Commission voted Thursday to eliminate mandatory cybersecurity requirements for telecommunications carriers—just months after one of the most devastating espionage campaigns in American history exposed glaring vulnerabilities in the nation’s communications infrastructure.
The Vote That Weakened America’s Digital Defense
The FCC’s Republican commissioners, Chairman Brendan Carr and Commissioner Olivia Trusty, voted to rescind Biden-era rules that required telecommunications carriers to “secure their networks from unlawful access or interception of communications.” Democratic Commissioner Anna Gomez cast the lone dissenting vote, warning that the decision leaves Americans “less protected than they were the day the Salt Typhoon breach was discovered.” [
FTC Chair Warns Tech Giants Against Weakening Data Privacy for Foreign Compliance
Tech companies face regulatory crossfire as Trump administration pushes back on EU and UK digital content laws Federal Trade Commission Chairman Andrew Ferguson has issued a stark warning to America’s biggest technology companies: complying with European and British digital content regulations cannot come at the expense of American users’ privacy
![]()
Security Careers HelpSecurity Careers
The timing couldn’t be more troubling. This rollback comes in the direct aftermath of Salt Typhoon, a Chinese state-sponsored cyberespionage campaign that compromised at least nine major U.S. telecommunications companies, including AT&T, Verizon, T-Mobile, and Lumen. The breach has been described by Senate Intelligence Committee Chairman Mark Warner as “the worst telecom hack in our nation’s history—by far.”
What Was Actually Rolled Back
The rescinded regulations, adopted on January 15, 2025, during the final days of the Biden administration, had established two critical requirements:
- Mandatory Network Security: A declaratory ruling under the Communications Assistance for Law Enforcement Act (CALEA) that “affirmatively requires telecommunications carriers to secure their networks from unlawful access or interception of communications”
- Annual Certification: A proposed rule that would have forced telecom providers to annually certify their cyber risk management plans with the FCC
Chairman Carr characterized these rules as “rushed,” “unlawful,” and “ineffective,” arguing they exceeded the agency’s authority under CALEA and imposed “inflexible and ambiguous requirements.” He claimed the FCC has “adopted targeted rules to address the greatest cybersecurity risks to critical communications infrastructure without imposing inflexible and ambiguous requirements.”
The Salt Typhoon Reality Check
The FCC’s decision to eliminate these protections stands in stark contrast to the devastating reality of what actually happened during Salt Typhoon—and what continues to happen as hackers remain embedded in telecom systems. [
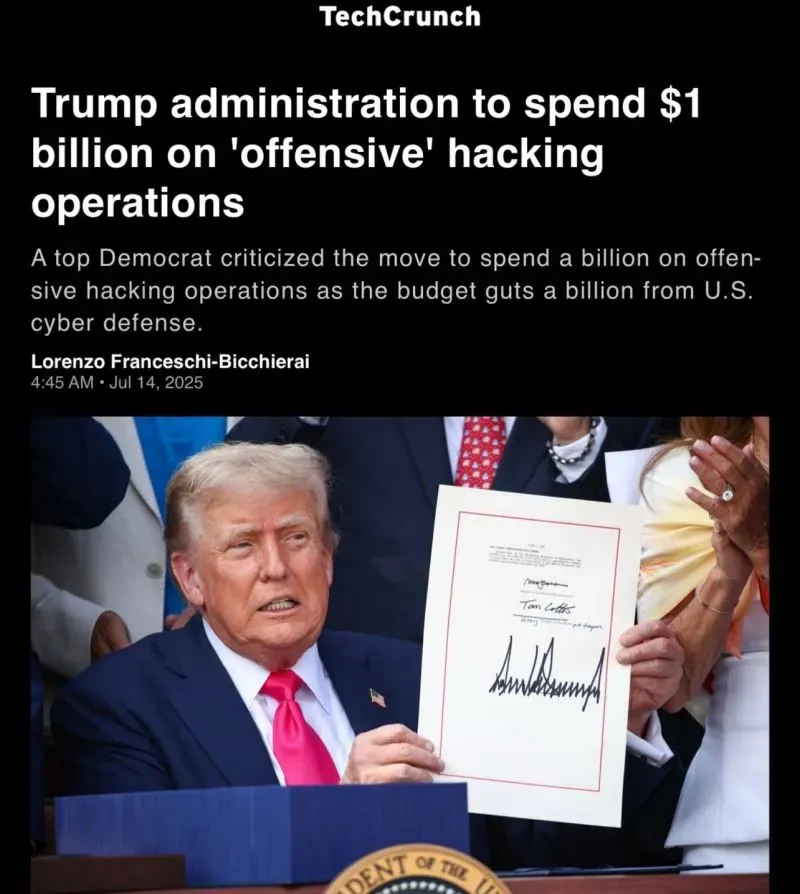
Trump’s $1 Billion Cyber Gambit: America’s Dangerous Shift from Defense to Offense
A Seismic Strategic Realignment in U.S. Cybersecurity In a move that has sent shockwaves through the cybersecurity community, the Trump administration has committed $1 billion over the next four years on what it calls “offensive cyber operations” while simultaneously slashing defensive cyber budgets by an equivalent amount. This represents
![]()
Security Careers HelpSecurity Careers
The Breach’s Staggering Scope
According to government officials and cybersecurity experts, Salt Typhoon represents an unprecedented intelligence compromise:
- At least 9 U.S. telecommunications companies breached, with several hundred additional organizations notified they may be at risk
- 80+ countries impacted globally, demonstrating sophisticated international coordination
- Persistent access maintained since at least 2022, with hackers still not fully eradicated from all compromised systems
- Law enforcement wiretap systems compromised, allowing Chinese operatives to know who U.S. investigators were targeting
- High-value political targets including phones belonging to President-elect Donald Trump, Vice President-elect J.D. Vance, and members of the Harris campaign
- Metadata of over 1 million Americans accessed, with most victims still not notified
The White House’s December 2024 assessment revealed the breach succeeded because telecommunications companies failed to implement “rudimentary cybersecurity measures.” Deputy National Security Adviser Anne Neuberger reported finding shocking security failures, including:
- One administrator account with access to over 100,000 routers
- No password protection on servers containing authentication keys
- Plaintext storage of thousands of credentials
- Outdated operating systems lacking critical security patches
- Failed intrusion detection monitoring with logs ignored despite anomalous behavior
- No access controls between internet-facing systems and internal networks
“The reality is that from what we’re seeing regarding the level of cybersecurity implemented across the telecom sector, those networks are not as defensible as they need to be,” Neuberger stated. [
CISA Under Siege: Trump’s Nominee Promises Funding Amid Agency Overhaul
Sean Plankey faces heated confirmation hearing as cybersecurity agency undergoes dramatic downsizing and mission refocus The nation’s premier cybersecurity agency finds itself at a crossroads as Sean Plankey, President Donald Trump’s nominee to lead the Cybersecurity and Infrastructure Security Agency (CISA), attempts to reassure lawmakers that he can secure adequate
![]()
Security Careers HelpSecurity Careers

](https://securitycareers.help/cisa-under-siege-trumps-nominee-promises-funding-amid-agency-overhaul/)
Congressional Response vs. FCC Retreat
The contrast between congressional action and FCC rollback couldn’t be more pronounced. While the FCC eliminates enforcement mechanisms, Congress has responded with legislation specifically designed to address telecommunications vulnerabilities.
The Intelligence Authorization Act, passed by the Senate Intelligence Committee, establishes baseline cybersecurity requirements for vendors of telecommunications services to intelligence agencies and leverages the intelligence community’s procurement power to enforce standards across the sector.
Senator Maria Cantwell, chair of the Senate Commerce Committee which oversees the FCC, wrote in a scathing letter to Carr that the rescinded rules “simply brought the agency’s interpretation of [CALEA] in line with current network realities” and represented “a commonsense acknowledgment that providers are responsible for protecting public safety against cybersecurity threats.”
Senator Gary Peters, ranking member of the Senate Homeland Security Committee, stated he was “disturbed by the FCC’s effort to roll back these basic cybersecurity safeguards, which, if successful, will leave the American people exposed and erode efforts to harden our national security against attacks like these in the future.”
Industry’s Successful Lobbying Campaign
The telecommunications industry mounted an aggressive campaign against the Biden-era cybersecurity requirements, arguing they were overly burdensome and that voluntary cooperation works better than mandatory compliance.
This argument might carry weight if industry self-regulation had actually worked. Instead, the evidence demonstrates catastrophic failure: [
Reshaping America’s Digital Defense: Trump Administration’s Sweeping Changes to Intelligence and Cybersecurity Leadership
In the first months of President Donald Trump’s second term, his administration has implemented far-reaching personnel changes across America’s intelligence and cybersecurity apparatus. These changes, characterized by critics as a purge and by supporters as necessary restructuring, represent one of the most significant overhauls of the U.S. national security
![]()
Security Careers HelpSecurity Careers
The Track Record of “Voluntary Cooperation”
The Salt Typhoon incident provides a definitive answer to whether voluntary cybersecurity measures are sufficient. According to government investigations:
- Telecom companies failed to detect the multi-year intrusion
- Companies have not provided evidence they’ve removed intruders from their networks, even months after discovery
- Some exploited vulnerabilities dated back to 2018, with patches available but never implemented
- One provider’s management system was protected with a basic numeric password
Senator Cantwell specifically challenged Carr’s reliance on voluntary measures, noting that telecom companies “failed to detect the hacks and have not provided me any of the evidence I requested that they have removed the intruders from their networks.”
Similar patterns of inadequate security emerged in the SK Telecom breach, where South Korea’s largest telecommunications provider suffered a 90.9% collapse in operating profit after exposing 27 million customers due to shocking security failures including no password protection on critical servers and plaintext credential storage.
What Voluntary Cooperation Really Means
Chairman Carr pointed to telecom executives’ agreement to implement additional cybersecurity controls as evidence that voluntary measures work. These commitments include:
- Accelerated patching
- Reviewing access controls
- Improving threat-hunting efforts
- Disabling unnecessary outbound connections
- Increasing information-sharing with federal government
- Establishing a new Communications Cybersecurity Information Sharing and Analysis Center (C2 ISAC)
Commissioner Gomez demolished this argument: “Handshake agreements without teeth will not stop state-sponsored hackers in their quest to infiltrate our networks. They won’t prevent the next breach. They do not ensure that the weakest link in the chain is strengthened. If voluntary cooperation were enough, we would not be sitting here today in the wake of Salt Typhoon.”
The White House echoed this concern, with Neuberger stating that UK officials told her their mandatory regulations meant breaches “would have been found faster, contained faster, and wouldn’t have spread as widely” as Salt Typhoon did in the United States.
The Compliance and Enforcement Gap
The FCC’s decision to eliminate cybersecurity requirements creates a dangerous enforcement vacuum at a time when regulatory frameworks worldwide are strengthening.
International Comparison
Other nations have maintained or strengthened telecommunications cybersecurity requirements:
- United Kingdom: Mandatory security regulations in place since 2018
- Australia: Telecommunications security framework established in 2018
- European Union: NIS2 Directive covering telecommunications as critical infrastructure with mandatory incident reporting and supply chain security requirements
The FCC’s approach now places the United States as an outlier, with weaker telecommunications security oversight than peer nations despite facing the most sophisticated threats.
The Enforcement Problem
Without mandatory requirements and certification processes, the FCC has effectively eliminated its ability to:
- Establish baseline security standards that all carriers must meet
- Verify compliance through annual certification requirements
- Hold carriers accountable for security failures before breaches occur
- Create enforceable frameworks rather than relying on voluntary commitments
This represents a fundamental shift from proactive security governance to reactive incident response—closing the barn door after nation-state adversaries have already stolen the horses.
The Real Cost of Weak Cybersecurity
The telecommunications industry’s argument that mandatory security requirements are “too burdensome” ignores the catastrophic costs of inadequate security, both to individual companies and national security.
Corporate Financial Impact
The SK Telecom case provides a sobering example. The breach cost the company:
- $97 million in regulatory fines (record-breaking penalty)
- $349 million in customer compensation
- 90.9% collapse in operating profit
- 250,000+ customers lost to competitors, with potential losses reaching $5 billion over three years
- 25-year profit streak ended
These costs dwarf any expense associated with implementing proper cybersecurity controls. The reality is that robust security measures are vastly cheaper than breach remediation, regulatory penalties, customer compensation, and lost business.
National Security Implications
Beyond corporate balance sheets, weak telecommunications security threatens fundamental national security interests:
- Intelligence Compromise: China gained access to U.S. law enforcement wiretap systems, revealing investigative targets
- Political Espionage: High-level government officials’ communications compromised
- Infrastructure Vulnerability: Access to telecommunications networks provides entry points to other critical infrastructure
- Persistent Threat: Hackers remain in systems months after discovery, continuing intelligence collection
- Supply Chain Risk: Compromise extends beyond individual carriers to backbone providers and interconnection points
As cybersecurity expert Tom Kellermann stated: “In my 25 years in cybersecurity, this is the most significant systemic cyber-intrusion to date, period.”
The “Flexibility” Fallacy
Chairman Carr’s justification emphasizes “flexible and tailored solutions” over “inflexible and vague” mandatory requirements. This framing deserves scrutiny.
What “Flexibility” Actually Means
In cybersecurity contexts, “flexibility” often translates to:
- No minimum standards: Companies choose their own security level
- No verification: No requirement to demonstrate effectiveness
- No accountability: No consequences for failures until after catastrophic breaches
- Race to bottom: Economic pressure to minimize security spending
The Salt Typhoon breach demonstrates what “flexible” approaches produced: multi-year persistent access by foreign intelligence services because telecommunications companies chose not to implement available security patches, used basic numeric passwords on critical systems, and failed to monitor their own networks effectively.
What Mandatory Requirements Actually Provide
In contrast, mandatory cybersecurity requirements offer:
- Baseline protection: Everyone must meet minimum standards
- Accountability framework: Clear expectations and consequences
- Verification mechanisms: Regular audits and certifications
- Level playing field: Security costs distributed across industry
- Proactive stance: Problems identified before breaches occur
The Biden-era rules didn’t dictate specific technologies or approaches—they required carriers to have and implement risk management plans. That’s not inflexible micromanagement; it’s basic governance.
What This Means for Different Stakeholders
The FCC’s decision has different implications for various parties:
For Telecommunications Customers
American consumers and businesses now face:
- Reduced security on communications infrastructure
- Continued vulnerability to foreign espionage
- No assurance that carriers implement basic protections
- Limited recourse when breaches occur
- Information asymmetry: Customers can’t verify carrier security
As noted in our analysis of class action litigation in data breaches, telecommunications breaches often trigger extensive legal action, but class action remedies rarely fully compensate victims for privacy violations and security compromises.
For Telecommunications Companies
Carriers that lobbied for this rollback may find they’ve secured a pyrrhic victory:
- Competitive disadvantage: Security-conscious customers may prefer carriers that maintain higher standards
- Increased liability: Absence of mandatory requirements doesn’t eliminate legal liability for breaches
- Regulatory uncertainty: Future administrations may implement even stricter requirements
- Reputational damage: Associated with weakening national security protections
For Foreign Adversaries
Nation-state threat actors are the clear winners:
- Reduced pressure: No mandatory security improvements from last round of compromises
- Maintained access: Existing footholds in networks less likely to be discovered
- Future opportunities: Voluntary measures easier to bypass than enforced requirements
- Strategic advantage: U.S. infrastructure remains more vulnerable than peer nations
For Government and Law Enforcement
Federal agencies face continued challenges:
- Compromised intelligence: Wiretap systems remain vulnerable
- Limited oversight: Reduced ability to ensure carrier security
- Ongoing response: Must continue addressing Salt Typhoon without improved protections
- International concerns: Allied nations question U.S. telecommunications security
Alternative Regulatory Approaches
While the FCC has retreated from enforcement, other regulatory frameworks demonstrate effective approaches:
CISA’s Enhanced Guidance
The Cybersecurity and Infrastructure Security Agency, as the Sector Risk Management Agency for communications, released Enhanced Visibility and Hardening Guidance for Communications Infrastructure. This guidance represents collaborative threat intelligence sharing but lacks enforcement mechanisms.
State-Level Action
Individual states could implement telecommunications security requirements through:
- Public utility commission oversight
- State-specific critical infrastructure protection laws
- Procurement requirements for government contracts
- Consumer protection regulations
However, this fragmented approach lacks the comprehensive coverage of federal requirements.
Congressional Legislation
The House passed a bill requiring the establishment of an interagency group, led by CISA, to respond to China-backed telecommunications hacks. This represents process coordination but doesn’t establish security requirements.
The Intelligence Authorization Act’s telecommunications provisions offer a model for future legislative action, using procurement power to enforce standards.
Looking Ahead: The Next Breach
Commissioner Gomez’s dissent proves prescient: “Simply trusting industry to police itself is an invitation for the next breach.”
Predictable Outcomes
Based on the pattern established by Salt Typhoon and the FCC’s response, we can predict:
- Continued Presence: Chinese intelligence services maintain persistent access to telecommunications networks
- Future Breaches: Additional compromises by other nation-state adversaries (Russia, Iran, North Korea)
- Delayed Discovery: Voluntary security measures fail to detect intrusions quickly
- Reactive Response: Government and industry scramble to respond after damage is done
- Renewed Calls for Regulation: Post-breach pressure for mandatory requirements returns
What Would Actually Work
Effective telecommunications cybersecurity requires:
- Mandatory minimum standards: Clear baseline requirements all carriers must meet
- Regular verification: Audits, certifications, and third-party assessments
- Enforcement mechanisms: Meaningful penalties for non-compliance
- Threat intelligence sharing: Government-industry collaboration on specific threats
- Supply chain security: Requirements extending to vendors and partners
- Incident response requirements: Mandatory reporting and coordination
- International coordination: Alignment with allied nations’ security frameworks
Industry Sectors to Watch
The FCC’s decision may influence cybersecurity regulation in other critical infrastructure sectors:
Energy and Utilities
Following the recent surge in critical infrastructure attacks, energy sector regulators may face similar industry pressure to rely on voluntary measures rather than mandatory compliance.
Financial Services
Banking and financial institutions generally face stronger regulatory oversight, but the FCC precedent could influence debates about proportionality and burden.
Healthcare
Healthcare providers continue struggling with cybersecurity, as demonstrated by ongoing ransomware incidents. The telecommunications regulatory rollback may embolden opposition to healthcare-specific security requirements.
The Broader Implications for National Security
Salt Typhoon represents more than a telecommunications breach—it’s part of China’s comprehensive strategy to infiltrate American critical infrastructure. The FCC’s decision to weaken security requirements must be understood in this broader context.
China’s Multi-Front Campaign
Chinese threat actors have systematically targeted U.S. infrastructure:
- Salt Typhoon: Telecommunications networks for intelligence gathering
- Volt Typhoon: Pre-positioning for destructive attacks on critical infrastructure
- Flax Typhoon: Compromising IoT devices for botnet operations
- Silk Typhoon: Targeting IT supply chains
Each campaign demonstrates sophisticated capabilities and long-term strategic planning. The FCC’s voluntary approach seems inadequate against adversaries operating with state resources and multi-year planning horizons.
What Organizations Should Do Now
Despite weakened federal requirements, organizations that depend on telecommunications infrastructure should:
For Enterprise Customers
- Vendor assessment: Evaluate telecommunications providers’ security practices
- Contract requirements: Include security provisions in service agreements
- Encryption: Implement end-to-end encryption for sensitive communications
- Redundancy: Don’t rely solely on single carriers
- Monitoring: Deploy tools to detect anomalous communications patterns
For Security Professionals
- Threat modeling: Assume telecommunications compromise in risk assessments
- Defense in depth: Don’t trust network-level security as sole protection
- Incident planning: Prepare for telecommunications infrastructure compromise scenarios
- Supply chain: Assess risks from telecommunications dependencies
- Advocacy: Support stronger security requirements through professional organizations
For Telecommunications Carriers
Despite regulatory rollback, responsible carriers should:
- Maintain standards: Continue implementing robust security controls
- Transparency: Communicate security practices to customers
- Industry leadership: Support development of voluntary standards that actually work
- Threat intelligence: Participate actively in information sharing
- Long-term thinking: Recognize that strong security is competitive advantage
The Role of Market Forces
Some argue that market mechanisms will drive telecommunications security improvement without regulation. The evidence suggests otherwise.
Why Markets Fail for Security
Telecommunications security exhibits classic market failure characteristics:
- Information asymmetry: Customers can’t evaluate carrier security
- Externalities: Security failures impose costs on society beyond direct customers
- Public goods: National security benefits don’t accrue to individual carriers
- Long time horizons: Consequences appear years after decisions
- Complexity: Technical sophistication exceeds most decision-makers’ expertise
These factors mean rational profit-maximizing behavior leads to underinvestment in security—exactly what Salt Typhoon demonstrated.
International Reactions and Implications
The FCC’s decision has drawn attention internationally, particularly among allied nations concerned about telecommunications security.
Allied Nation Perspectives
Countries participating in the Five Eyes intelligence alliance (US, UK, Canada, Australia, New Zealand) jointly released guidance on telecommunications security threats in response to Salt Typhoon. The FCC’s regulatory rollback contradicts this collaborative approach and may strain intelligence sharing relationships.
Adversary Calculations
Chinese intelligence services are undoubtedly analyzing the FCC decision’s implications. The removal of mandatory requirements likely factors into their risk assessments for maintaining persistent access to U.S. telecommunications networks.
The Path Forward
What comes next depends on how various stakeholders respond:
Short Term (6-12 months)
- Telecommunications companies implement voluntary commitments (or don’t)
- CISA continues collaborative security guidance without enforcement power
- Congressional oversight hearings examine FCC decision
- State-level regulatory experimentation begins
- Salt Typhoon remediation continues without improved requirements
Medium Term (1-3 years)
- Additional telecommunications breaches likely discovered
- Industry voluntary approach proves insufficient (again)
- Legislative proposals for mandatory requirements gain traction
- International security cooperation models emerge
- Class action litigation from Salt Typhoon proceeds through courts
Long Term (3-5 years)
- Comprehensive telecommunications security legislation possible after next major breach
- Integration of telecommunications security into broader critical infrastructure framework
- Potential reorganization of regulatory authority and sector oversight
- Evolution of threat landscape as adversaries exploit regulatory gaps
🎧 Related Podcast Episode
Conclusion: Security Theater vs. Security Reality
The FCC’s November 21, 2025 decision to eliminate mandatory telecommunications cybersecurity requirements represents a triumph of industry lobbying over national security imperatives.
Chairman Carr’s justification—that voluntary cooperation and flexible approaches work better than mandatory compliance—stands refuted by the Salt Typhoon breach itself. Chinese intelligence services penetrated U.S. telecommunications networks for years precisely because carriers failed to implement basic security measures voluntarily.
Commissioner Gomez’s dissent captures the fundamental issue: “Handshake agreements without teeth will not stop state-sponsored hackers in their quest to infiltrate our networks.”
The telecommunications industry successfully argued that mandatory security requirements were too burdensome. They failed to mention that the alternative—catastrophic breaches compromising national security—is vastly more burdensome for everyone else.
As we documented in our analysis of the expanding Salt Typhoon campaign, Chinese intelligence services didn’t stop at initial telecommunications compromises—they expanded into data centers and backbone infrastructure. Without mandatory security requirements and enforcement mechanisms, what incentive exists for carriers to implement the comprehensive security measures needed to prevent the next Salt Typhoon?
The answer, unfortunately, appears to be none. Until the next major breach forces another regulatory reckoning, American telecommunications infrastructure will remain vulnerable to sophisticated nation-state adversaries. The FCC has chosen security theater over security reality, and Americans will pay the price.
Resources and Further Reading
- Salt Typhoon: Chinese Hackers Expand Beyond Telecom to Target Critical US Data Infrastructure
- SK Telecom’s Data Breach Devastates Q3 Financials
- Senate Passes Intelligence Authorization Act in Response to Salt Typhoon
- Class Action Lawsuits in Data Breaches: A 2025 Legal Compliance Guide
- Understanding the Evolving Cybersecurity Threat Landscape in the EU
- The 10 Most Recent and Significant Cyber Attacks and Data Breaches Worldwide (Q1 2025)





