Introduction: Protecting Your Growth in a High-Risk Industry
Welcome to the booming legal cannabis market. As the industry rapidly expands, with projected sales expected to hit $40.6 billion by 2024, it has also become a prime target for cybercriminals. These attackers see cannabis businesses—often new, fast-growing, and data-rich—as the perfect opportunity for theft and disruption. [
Cannabis Business Security Tools | cannabisrisk.diy
Comprehensive security tools, checklists, and compliance resources for cannabis businesses. Estimate breach costs, audit PoS, review vendor security, and more.
cannabisrisk.diy](https://cannabisrisk.diy/)
Think of cybersecurity not as a complex technical burden, but as a fundamental business practice. It is just as essential as tracking inventory or managing your finances. Strong security protects your profits, ensures you remain compliant with state regulations, and, most importantly, earns the trust of your customers. A single data breach can be devastating; according to the National Cybersecurity Alliance, about six out of ten small businesses that fall victim to a cyberattack go out of business within six months. This guide will provide a clear, straightforward path to understanding the threats you face and the practical steps you can take to protect your business.
1. Why Your Cannabis Business is a Top Target for Hackers
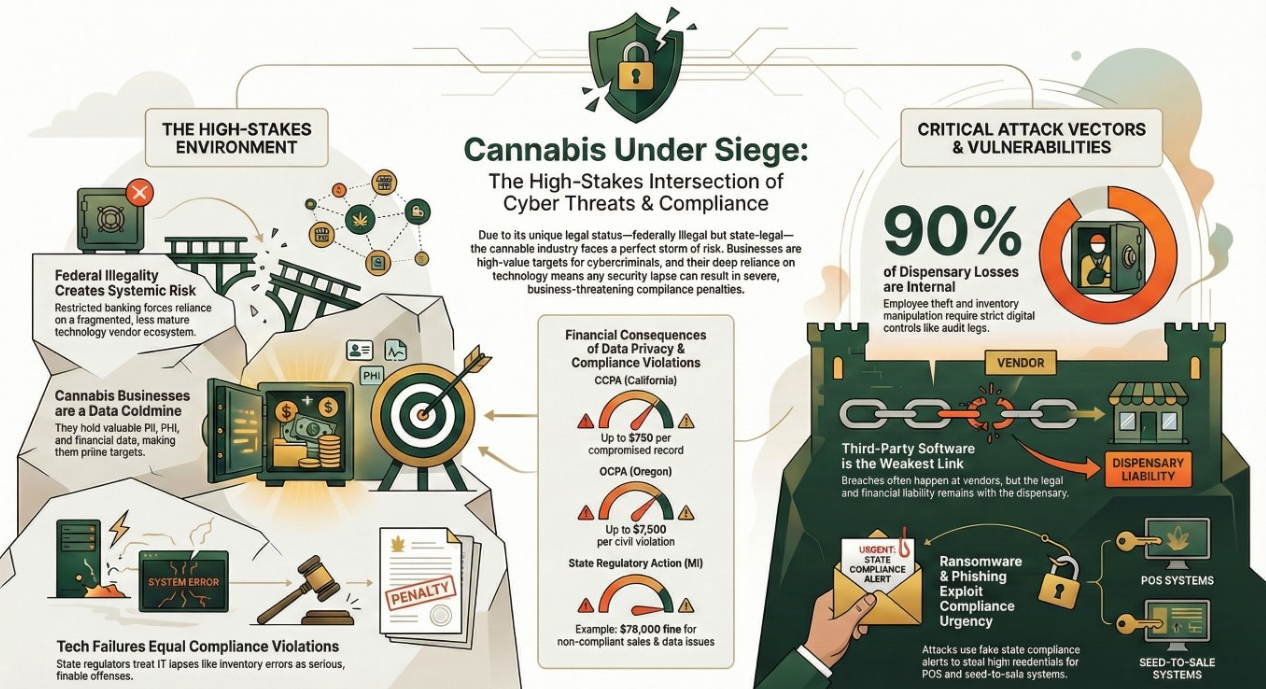
The cannabis industry’s unique combination of high-value data, a fragmented regulatory environment, and rapid growth makes it especially attractive to cybercriminals. Here are the key reasons why your business is in their crosshairs:
- You Handle High-Value Data: Cannabis businesses are a gold mine of sensitive information. You collect and store a huge volume of customer data, including names, phone numbers, driver’s licenses (Personally Identifiable Information, or PII), and, in the case of medical dispensaries, protected health records (PHI). Because cannabis remains federally illegal, a data breach carries a unique reputational risk for your customers, making this data especially valuable on the dark web.
- Fragmented Security Landscape: The conflict between state and federal law means there are no uniform, national security standards for the cannabis industry. This forces you to rely on a patchwork of specialized technology vendors for everything from Point-of-Sale (POS) systems to compliance tracking. These vendors may not have the mature, robust security infrastructure of mainstream providers, creating potential weak points in your defenses and expanding your attack surface.
- Perceived as “Low-Hanging Fruit”: Many new cannabis operators are understandably focused on licensing, growth, and the day-to-day challenges of a new business. Cybersecurity is often treated as a lower priority. Criminals are well aware of this and actively hunt for businesses that have weaker defenses, viewing them as easier and more profitable targets.
Now that you understand why your business is a target, let’s look at the specific methods criminals use to exploit these vulnerabilities.
2. The Top 5 Cyber Threats Explained in Simple Terms
Cybercriminals use a variety of tactics to exploit the unique threat landscape of the cannabis industry. Understanding these common threats is the first step toward building an effective defense.
1. Phishing & Social Engineering: The Art of the Trick
Phishing is a type of scam where a criminal sends an email or text message impersonating a trusted entity—like a government agency, a supplier, or even your company’s CEO—to trick an employee into giving up sensitive information like passwords or financial details. It is by far the most common type of attack, responsible for nearly 9 out of 10 data breaches.
Here are some cannabis-specific examples:
- Fake Compliance Alerts: An attacker sends an email that looks exactly like a notification from your state’s seed-to-sale system (e.g., Metrc). It warns of a “compliance issue” and prompts an employee to click a link and log in to a fake website, stealing their credentials.
- Fraudulent Invoices: The back office receives an email that appears to be from a regular supplier, stating that their banking information has changed. The email instructs your team to send the next payment to a new account, which is actually controlled by the attacker.
- Impersonating Leadership: A manager receives a text message that appears to be from the dispensary owner. The message describes an “emergency” and instructs the manager to deliver a large sum of cash to an off-site location, which is a setup for theft.
2. Ransomware: Your Data Held Hostage
Ransomware is a type of malicious software (malware) that, once inside your network, encrypts your critical business data—customer lists, financial records, inventory—making it completely inaccessible. The attackers then demand a ransom, often in cryptocurrency, to restore your access. The FBI reports that around 4,000 ransomware attacks occur every day, and small businesses are the most frequent targets, accounting for 71% of all attacks in 2018.
3. Third-Party Tech Breaches: Your Vendor’s Problem Becomes Your Problem
One of your biggest risks doesn’t come from your own network, but from the software partners you rely on every day, especially Point-of-Sale (POS) systems. The 2024 data breach at Stiiizy, a major cannabis operator, is a perfect example. The breach exposed the sensitive data of over 420,000 customers, including government-issued IDs and medical cannabis cards.
Crucially, the attack didn’t happen on Stiiizy’s own servers. Instead, criminals compromised an account at a third-party Software-as-a-Service (SaaS) vendor used by Stiiizy’s POS provider. This case highlights a critical reality: even if your internal security is perfect, a vulnerability in your vendor’s system can lead to a massive breach, and the legal liability ultimately falls on your business.
This incident proves the traditional security perimeter is dead. The risk now lies in the SaaS supply chain. For a cannabis business, vendor risk management is as critical as securing your own storefront. This shifts the mindset from “my security” to “my ecosystem’s security.”
4. Unsafe Connections: Risks from Public WiFi and “Smart” Devices
Cyber threats can also come from unsecured connections.
- Public WiFi: When employees work remotely from a café or hotel and connect to public WiFi, they are vulnerable to “man-in-the-middle” attacks. Hackers on the same network can intercept data and steal login credentials for your business systems.
- Internet of Things (IoT) Leaks: Cultivation facilities often use “smart” devices like fully automated growing stations to control temperature, lighting, and irrigation. These IoT devices are often shipped with simple, default passwords. Hackers use automated programs to scan the internet for these devices, and if the passwords haven’t been changed, they can gain access, giving them the power to sabotage your environmental controls and destroy an entire crop cycle overnight.
5. Insider Threats: When the Danger is Already Inside
While outside hackers pose a significant threat, the data shows that the vast majority of losses at a dispensary—up to 90%—come from employee theft. This goes far beyond stealing physical products. Digital insider threats are just as damaging and include manipulating inventory records in the POS system to hide stolen products, creating discrepancies that will be flagged during a state audit of your Metrc data. Other examples include giving unauthorized discounts to friends and family or creating fraudulent returns to pocket cash.
These threats don’t just impact your bottom line; they can also put your business license at risk by causing serious compliance failures.
3. Where Compliance and Cybersecurity Collide
For a cannabis business, strong cybersecurity and state compliance are two sides of the same coin. A technological failure, whether from a hack or an internal error, can directly lead to a regulatory violation, resulting in fines or even the loss of your license.
Your Seed-to-Sale (S2S) System is a Compliance Tool
State-mandated S2S systems like Metrc (the state-mandated seed-to-sale tracking system used in over 20 states) are the technological backbone of compliance. They track every product from the moment it’s grown to the moment it’s sold. State regulators are strict and frequently issue fines for “METRC non-compliance,” which often stems from technological issues.
For example, a ransomware attack that locks your POS system prevents you from reporting sales to Metrc in real-time. This IT failure immediately becomes a regulatory failure, resulting in fines for “METRC non-compliance”—even though the root cause was a cyberattack, not an operational error.
The Payment Processing Trap
Because cannabis is federally illegal, major credit card networks like Visa and Mastercard prohibit cannabis transactions. This has forced the industry to find workarounds, some far riskier than others.
|
Risky Workaround |
The Safe Alternative | |
“Cashless ATMs” disguise debit card sales as ATM withdrawals. This is a deceptive practice that violates card network rules, is considered legally fraudulent, and is being aggressively shut down by financial institutions. |
ACH (Automated Clearing House) allows for direct bank-to-bank transfers (like an eCheck). This method is federally tolerated, transparent, secure, and avoids the risks associated with the major card networks. |
Protecting Customer Data Isn’t Just Good Practice, It’s the Law
Many states have enacted strict data privacy laws that apply to cannabis businesses. A data breach can expose you to severe financial penalties under these regulations.
- The California Consumer Privacy Act (CCPA) allows consumers to sue businesses after a data breach, with statutory damages of up to $750 per compromised record.
- The Oregon Consumer Privacy Act (OCPA) allows for civil penalties of up to $7,500 per violation.
This level of liability fundamentally changes the risk posture of a cannabis retailer. A single, large-scale data breach could create financial penalties that exceed the company’s annual revenue, making data protection a matter of financial survival, not just IT compliance.
Understanding these overlapping risks is the first step; now let’s focus on the practical, foundational steps you can take to build your defenses.
4. Four Pillars of Your Digital Fortress: An Actionable Blueprint
Securing your business doesn’t require a massive budget or a dedicated IT department. By implementing a few foundational security measures, you can dramatically reduce your risk.
1. Build Your Human Firewall: Your First and Best Line of Defense
Your employees are your first and most important line of defense. A well-trained team that can spot a scam is more effective than any piece of software. Implement regular training for all staff—from budtenders to the back office—on the following essentials:
- Recognizing Phishing: Teach them to be suspicious of emails or texts that create a sense of urgency, come from an unfamiliar sender, or ask for login credentials.
- Password Hygiene: Mandate the use of strong, unique passwords for every system.
- Verification Protocol: Instruct employees to always verify unusual requests for money, data, or credentials through a separate, secure channel. If an email asks for a wire transfer, they should make a direct phone call to a known number to confirm the request is legitimate.
2. Deploy Essential Tech Defenses
Complement your human firewall with these critical technical controls:
- Use Multi-Factor Authentication (MFA): MFA requires a second form of verification—like a code sent to a phone—in addition to a password. It is one of the single most effective ways to prevent unauthorized access to your accounts, even if a password is stolen.
- Maintain Secure Data Backups: The only way to reliably recover from a ransomware attack without paying the ransom is to have secure, offline, and encrypted backups of your critical data. Test your backup restoration process regularly to ensure it works.
- Install Reputable Security Software: Ensure all computers, including POS terminals, are protected with robust and up-to-date anti-virus software.
- Change All Default Passwords: The moment you install any new equipment—from your WiFi router to IoT sensors in your grow facility—change the default administrator password. This simple step closes one of the most common entry points for hackers.
3. Develop a “What If?” Plan
A crisis is not the time to invent a plan. A core component of resilience is having a documented, tested incident response plan that ensures your team can act decisively, not chaotically. Document the answers to the following:
- Who is the first person we call in a cyber incident (e.g., an IT consultant, legal counsel)?
- How do we quickly disconnect affected computers or systems from the network to stop an attack from spreading?
- How will we continue to operate and make sales if our POS system is down?
- Who is the designated person authorized to speak to regulators, law enforcement, or customers?
Conclusion: From Compliant to Resilient
In the modern cannabis industry, cybersecurity is not an optional IT expense—it is a core business function that protects your finances, your license, and your reputation. By understanding your risks and taking proactive, foundational steps to defend your business, you can move beyond simply being compliant to becoming truly resilient. In an industry where trust is paramount and licenses are fragile, a robust cybersecurity program is no longer a cost center—it is a competitive advantage that builds brand value and ensures long-term viability. Building a culture of security will earn the trust of your customers, empower your team, and ensure your long-term success in this competitive and exciting industry.