Introduction: The Evolution of Security Operations
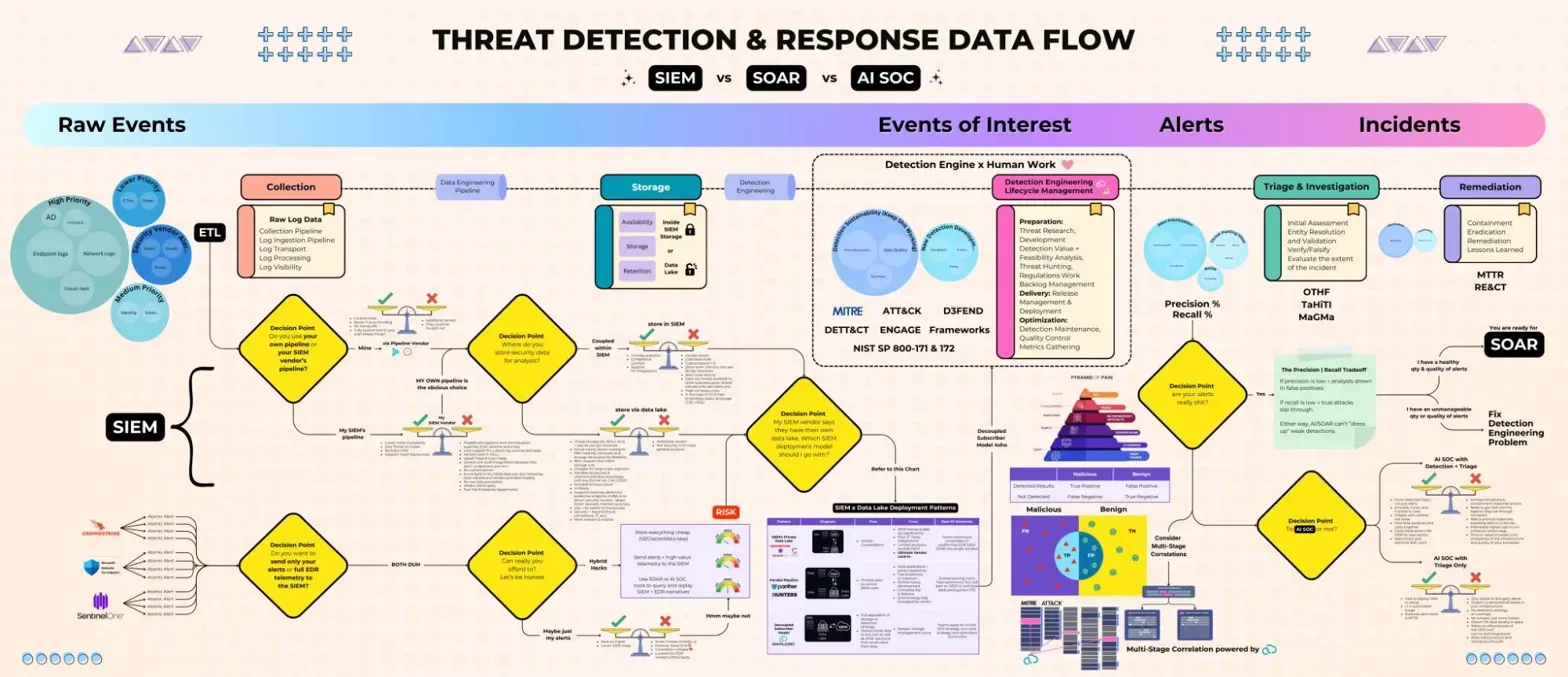
The security operations landscape has transformed dramatically over the past decade. What once relied heavily on manual processes and isolated tools has evolved into an interconnected ecosystem of intelligent platforms working in concert. This comprehensive guide explores the modern threat detection and response data flow, breaking down how Security Information and Event Management (SIEM), Security Orchestration, Automation and Response (SOAR), and AI-powered Security Operations Centers (AI SOC) work together to protect organizations from cyber threats. [
Unsupported client – Canva
Unsupported client – Canva
![]()
Canva

The Four Pillars of Modern Threat Detection
1. Raw Events: The Foundation of Security Monitoring
Every security operation begins with raw events - the massive volume of data generated by various sources across an organization’s infrastructure. These include:
- Network Logs: Traffic patterns, connection attempts, and communication flows
- Endpoint Logs: System activities, process executions, and file modifications
- Application Logs: User activities, authentication attempts, and application behaviors
- Cloud Logs: API calls, resource access, and configuration changes
- Security Tool Logs: Firewall alerts, IDS/IPS notifications, and antivirus detections
The sheer volume of these events - often millions per day in enterprise environments - creates the first major challenge: collection and normalization.
2. Events of Interest: Separating Signal from Noise
Not all events are created equal. The transition from raw events to “events of interest” represents the critical filtering stage where security teams identify potentially significant activities. This stage involves:
- Pattern Recognition: Identifying behaviors that deviate from baseline normal activity
- Threat Intelligence Integration: Matching events against known indicators of compromise (IOCs)
- Risk Scoring: Assigning severity levels based on context and potential impact
- Correlation: Connecting related events across different sources to identify attack chains
3. Alerts: When Detection Becomes Actionable
Alerts represent the point where the system has identified activities requiring human or automated intervention. Modern alert management includes:
- Alert Prioritization: Using frameworks like MITRE ATT&CK to understand attack techniques
- Context Enrichment: Adding relevant information about affected assets and users
- False Positive Reduction: Implementing machine learning to reduce alert fatigue
- Alert Clustering: Grouping related alerts to provide a comprehensive view of potential incidents
4. Incidents: Confirmed Threats Requiring Response
Incidents represent confirmed security issues that require immediate action. The incident stage triggers:
- Triage and Investigation: Deep-dive analysis to understand scope and impact
- Remediation Planning: Developing response strategies based on threat type
- Containment Actions: Isolating affected systems to prevent spread
- Recovery Operations: Restoring normal operations while maintaining evidence
The SIEM Layer: Intelligence Through Aggregation
Core SIEM Capabilities
The SIEM platform serves as the central nervous system of security operations, providing:
Data Collection and Normalization
- Ingesting logs from diverse sources using various protocols (syslog, API, agents)
- Converting disparate log formats into a common schema
- Handling high-velocity data streams in real-time
Storage and Retention
- Maintaining historical data for compliance and forensics
- Implementing efficient compression and indexing strategies
- Managing data lifecycle policies
Detection Engineering
- Creating custom detection rules based on organizational threats
- Implementing behavioral analytics to identify anomalies
- Utilizing machine learning for pattern recognition
Decision Points in SIEM Processing
The diagram highlights several critical decision points in SIEM processing:
- Collection Pipeline Decisions: Determining which data sources to ingest and at what granularity
- Storage Optimization: Balancing between hot (immediate access) and cold (archived) storage
- Rule Efficiency: Optimizing detection rules to minimize false positives while maintaining coverage
Key SIEM Metrics and Frameworks
Modern SIEMs integrate with industry frameworks:
- MITRE ATT&CK: Mapping detections to adversary tactics and techniques
- NIST SP 800-171 & 172: Ensuring compliance with security requirements
- Detection Engineering Frameworks: Systematic approaches to developing and testing detection logic
The SOAR Revolution: Automation at Scale
Understanding SOAR’s Role
SOAR platforms represent the evolution from reactive to proactive security operations. They excel at:
Orchestration
- Coordinating actions across multiple security tools
- Managing complex workflows involving multiple teams
- Ensuring consistent response procedures
Automation
- Executing repetitive tasks without human intervention
- Performing initial triage and enrichment automatically
- Scaling response capabilities beyond human limitations
Response Coordination
- Implementing playbooks for common incident types
- Facilitating collaboration between teams
- Tracking response metrics and effectiveness
The Precision vs. Recall Tradeoff
The diagram illustrates a fundamental challenge in automated response: balancing precision (avoiding false positives) with recall (catching all true threats). SOAR platforms address this through:
- Confidence Scoring: Assigning probability scores to automated decisions
- Graduated Response: Implementing different automation levels based on confidence
- Human-in-the-Loop: Requiring approval for high-impact actions
SOAR Decision Trees and Playbooks
Modern SOAR platforms utilize sophisticated decision logic:
- Conditional Branching: If-then-else logic based on event attributes
- Parallel Processing: Executing multiple investigative paths simultaneously
- Dynamic Playbooks: Adapting response based on real-time findings
AI SOC: The Intelligence Amplifier
The Promise of AI in Security Operations
AI SOC represents the cutting edge of security operations, offering:
Advanced Analytics
- Natural language processing for unstructured data analysis
- Computer vision for detecting visual anomalies
- Predictive analytics for anticipating threats
Cognitive Automation
- Understanding context beyond rule-based logic
- Learning from past incidents to improve future responses
- Adapting to evolving threat landscapes
Human Augmentation
- Providing analysts with AI-powered insights
- Reducing cognitive load through intelligent prioritization
- Accelerating investigation through automated hypothesis testing
Multi-Stage Correlation
The diagram shows AI SOC’s multi-stage correlation approach:
- Entity Resolution: Identifying and linking related entities across events
- Temporal Analysis: Understanding attack progression over time
- Behavioral Modeling: Establishing baselines and detecting deviations
- Threat Hunting: Proactively searching for hidden threats
AI SOC Integration Points
AI capabilities integrate throughout the detection and response pipeline:
- Data Enrichment: Adding context from internal and external sources
- Anomaly Detection: Identifying subtle deviations from normal behavior
- Automated Investigation: Following investigative leads automatically
- Response Optimization: Selecting the most effective remediation strategies
The Integrated Security Operations Workflow
From Detection to Remediation
The complete workflow illustrated in the diagram shows:
- Initial Detection: SIEM identifies potential threats through rules and analytics
- Triage and Investigation: SOAR automates initial assessment and enrichment
- Advanced Analysis: AI SOC provides deep insights and correlations
- Response Coordination: SOAR executes response playbooks
- Remediation: Automated and manual actions to contain and eliminate threats
- Learning and Improvement: Feeding lessons learned back into detection logic
Key Integration Points
The diagram highlights critical integration points:
- SIEM to SOAR: Alert forwarding with full context
- SOAR to AI SOC: Complex investigations requiring advanced analytics
- AI SOC to SOAR: Refined incidents ready for automated response
- Bidirectional Feedback: Continuous improvement through shared intelligence
Best Practices for Implementation
1. Start with Strong Foundations
- Data Quality: Ensure comprehensive and reliable data collection
- Use Case Development: Focus on high-value detection scenarios
- Process Documentation: Create clear procedures for each stage
2. Progressive Automation
- Crawl-Walk-Run: Start with semi-automated processes before full automation
- Measure and Refine: Track metrics to identify automation opportunities
- Maintain Human Oversight: Keep analysts in the loop for critical decisions
3. Continuous Improvement
- Regular Tuning: Adjust detection rules based on false positive rates
- Threat Intelligence Integration: Stay current with emerging threats
- Team Training: Ensure staff can leverage advanced capabilities
4. Technology Integration
- API-First Architecture: Ensure platforms can communicate effectively
- Common Data Models: Standardize data formats across tools
- Centralized Orchestration: Use SOAR as the coordination hub
Career Implications for Security Professionals
Evolving Skill Requirements
The modern SOC requires professionals who understand:
- Detection Engineering: Creating and tuning detection logic
- Automation Scripting: Building playbooks and workflows
- Data Analysis: Interpreting complex correlations and patterns
- Threat Intelligence: Understanding adversary behaviors and techniques
New Role Opportunities
The integrated approach creates new specializations:
- SOAR Engineers: Designing and implementing automation workflows
- Detection Engineers: Developing sophisticated detection strategies
- AI/ML Security Analysts: Leveraging AI for threat detection
- Security Architects: Designing integrated security ecosystems
Professional Development Priorities
Security professionals should focus on:
- Platform Expertise: Deep knowledge of SIEM, SOAR, and AI SOC platforms
- Programming Skills: Python, PowerShell, and API development
- Framework Knowledge: MITRE ATT&CK, NIST, and other standards
- Analytical Thinking: Understanding complex attack chains and correlations
Future Trends and Considerations
Extended Detection and Response (XDR)
The convergence of SIEM, SOAR, and AI SOC points toward XDR platforms that provide:
- Unified visibility across all security layers
- Native integration eliminating compatibility issues
- Simplified management through consolidated interfaces
Autonomous Security Operations
Future developments may include:
- Self-healing systems that remediate without human intervention
- Predictive defense that anticipates and prevents attacks
- Adaptive security postures that evolve with threats
Challenges and Considerations
Organizations must address:
- Skills Gap: Finding professionals who understand integrated platforms
- Tool Sprawl: Managing complexity as capabilities expand
- Cost Management: Balancing investment with security outcomes
- Privacy Concerns: Ensuring AI systems respect data privacy
🎧 Related Podcast Episode
Conclusion: The Path Forward
The threat detection and response data flow illustrated in this diagram represents the current state-of-the-art in security operations. Success requires not just implementing these technologies, but understanding how they work together to create a resilient security posture.
For security professionals, this integrated approach offers both challenges and opportunities. Those who master the interplay between SIEM, SOAR, and AI SOC will be well-positioned to lead the next generation of security operations. The key is to view these platforms not as separate tools, but as complementary components of a unified defense strategy.
As threats continue to evolve, so too must our detection and response capabilities. The future belongs to security teams that can effectively leverage automation, artificial intelligence, and orchestration to stay ahead of adversaries. This diagram serves as both a roadmap for current operations and a foundation for future innovation in cybersecurity.
This article is part of SecurityCareers.help’s mission to provide comprehensive guidance for security professionals navigating the evolving landscape of cybersecurity operations.