In today’s complex and rapidly evolving threat landscape, organizations face an ever-increasing barrage of cyberattacks. The Security Operations Center (SOC) stands as the central hub for an organization’s cybersecurity efforts, acting as the frontline defense against malicious actors. This in-depth article will explore the critical functions, evolving trends, persistent challenges, and the significant influence of organizational structure and resources on the capabilities and maturity of modern SOCs, drawing upon insights from the provided sources.
The Foundation: Purpose and Core Functions of a SOC
At its core, the mission of a SOC is to centralize cybersecurity activity to protect an organization’s digital assets and ensure business continuity. A well-functioning SOC achieves this through a range of interconnected functions:
- Detection and Monitoring: The SOC continuously monitors security-relevant data from various sources, including network traffic, endpoint activity, logs, and cloud environments. Technologies like Security Information and Event Management (SIEM) play a crucial role in aggregating and analyzing this vast amount of data to identify potential threats.
- Triage: Once alerts are generated, SOC analysts perform triage to sort through potentially malicious activity and determine the order of importance for investigation. This prioritization is often based on factors like the attack’s progression, the criticality of the affected system, the privilege level of potentially compromised accounts, and whether the attack appears targeted or unique. Effective analysts leverage their knowledge of frameworks like the Lockheed Martin Cyber Kill Chain and the MITRE ATT&CK framework to understand attacker tactics, techniques, and procedures (TTPs).
- Investigation: After an alert is prioritized, SOC analysts conduct a more detailed investigation to verify if a security incident is truly occurring. This involves analyzing alert data, gathering additional evidence from network sensors or logs, and potentially performing open-source intelligence research. The goal is to accurately determine if an alert is a true or false positive. Structured and rigorous investigation techniques are crucial to avoid cognitive biases.
- Incident Response: When a confirmed security incident occurs, the SOC initiates the incident response process. This involves containing the incident, eradicating the threat, recovering affected systems, and implementing lessons learned to prevent future occurrences. Well-defined incident response plans, Standard Operating Procedures (SOPs), and playbooks are essential for a consistent and effective response.
- Threat Intelligence: Cyber threat intelligence (CTI) is a critical function that informs all other SOC activities. Threat intelligence teams gather, analyze, and disseminate information about adversary groups, their motivations, capabilities, and likely targets. This intelligence helps prioritize defenses, detection strategies, and incident response efforts. A Threat Intelligence Platform (TIP) can provide context to atomic indicators, enabling analysts to understand why an IP address or domain is considered malicious. Threat intelligence can be tactical (IOCs), operational (TTPs), or strategic (adversary motivations).
- Threat Hunting: Recognizing that not all threats trigger alerts, threat hunting is a proactive function where analysts actively search for potential malicious activity within the organization’s infrastructure. This involves formulating hypotheses about potential attacker presence and using various analysis techniques to uncover hidden threats.
- Vulnerability Management: While often a separate team, close collaboration between the SOC and vulnerability management is crucial. The SOC utilizes vulnerability scan results to prioritize triage efforts when an exploit attempt is detected against a vulnerable system.
- Forensics: Primarily focused on the incident response stage, forensics teams provide specialized knowledge to analyze compromised systems and uncover datable evidence of malicious activity.
- Penetration Testing and Red Teaming: These activities simulate attacks against the organization’s defenses to evaluate the effectiveness of the SOC’s people, processes, and technologies. [
Modern Security Operations Center
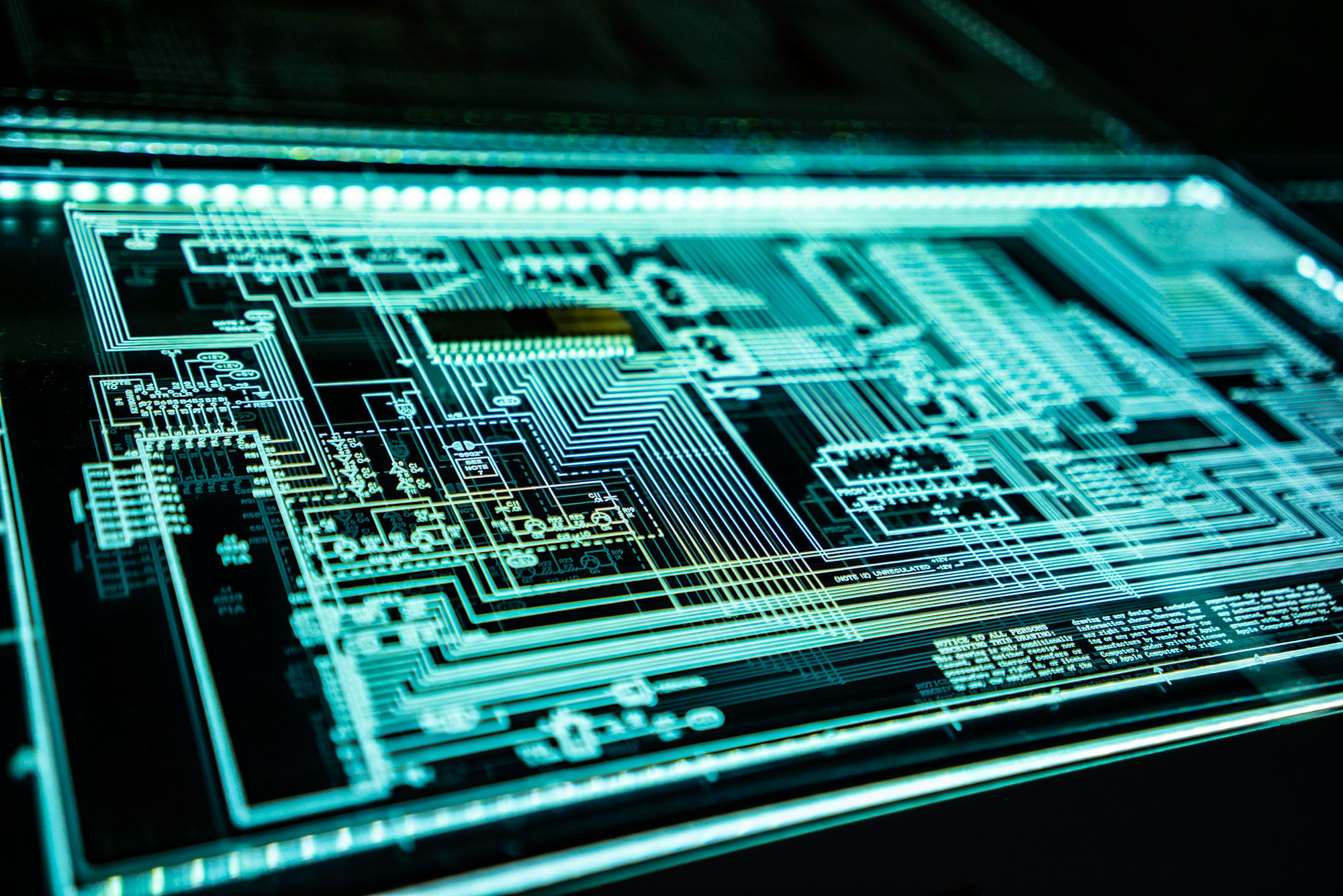
Below is an overview of how many organizations are now approaching “modern SOC” (Security Operations Center) architecture and deployment. The goal is to build something that is efficient, scalable, secure, and that lets humans focus on higher-value tasks by leveraging automation, AI/ML, and cloud infrastructure. While specific vendor or
![]()
Security Careers HelpSecurity Careers
](https://securitycareers.help/modern-security-operations-center/)
nThe Evolving Landscape: Trends Shaping Modern SOCs
Modern SOCs are constantly adapting to an evolving threat landscape and leveraging new technologies to enhance their effectiveness. Key trends include:
-
Integration of Advanced Technologies:
- Artificial Intelligence (AI) and Machine Learning (ML): AI and ML are being increasingly integrated into SOC operations to enhance threat detection, identify anomalies, and automate analysis of large datasets.
- Extended Detection and Response (XDR): XDR represents a move towards a more unified security approach by integrating data from endpoints, networks, cloud environments, and email to provide broader visibility and more contextualized threat detection and response.
- Security Orchestration, Automation, and Response (SOAR): SOAR platforms automate repetitive tasks, orchestrate workflows across different security tools, and streamline incident response processes, improving efficiency and reducing analyst workload. The 2023 SANS SOC Survey highlights the importance of continuous tuning of SOAR by skilled analysts to achieve its full potential.
-
Proactive Security Measures: A shift from purely reactive incident response to more proactive approaches like operational threat hunting is gaining momentum.
-
Enhanced Threat Intelligence Utilization: Modern SOCs are focusing on making threat intelligence more actionable by integrating it deeply into their detection and response processes. This includes consuming various threat intelligence feeds, potentially producing their own intelligence, and leveraging platforms to enrich alerts with context.
-
Emphasis on Metrics and Measurement: SOCs are increasingly focused on defining and tracking key performance indicators (KPIs) and metrics to measure their effectiveness, identify areas for improvement, and demonstrate value to stakeholders. Metrics are also used to justify funding for SOC operations.
-
Cloud Security Operations: With the widespread adoption of cloud services, SOCs are expanding their capabilities to monitor and secure cloud environments.
-
Collaboration and Information Sharing: Effective communication and collaboration within the SOC, with other internal teams, and with the external cybersecurity community are recognized as crucial for staying ahead of evolving threats. Sharing threat intelligence, like through platforms such as AlienVault OTX, strengthens the collective defense. [
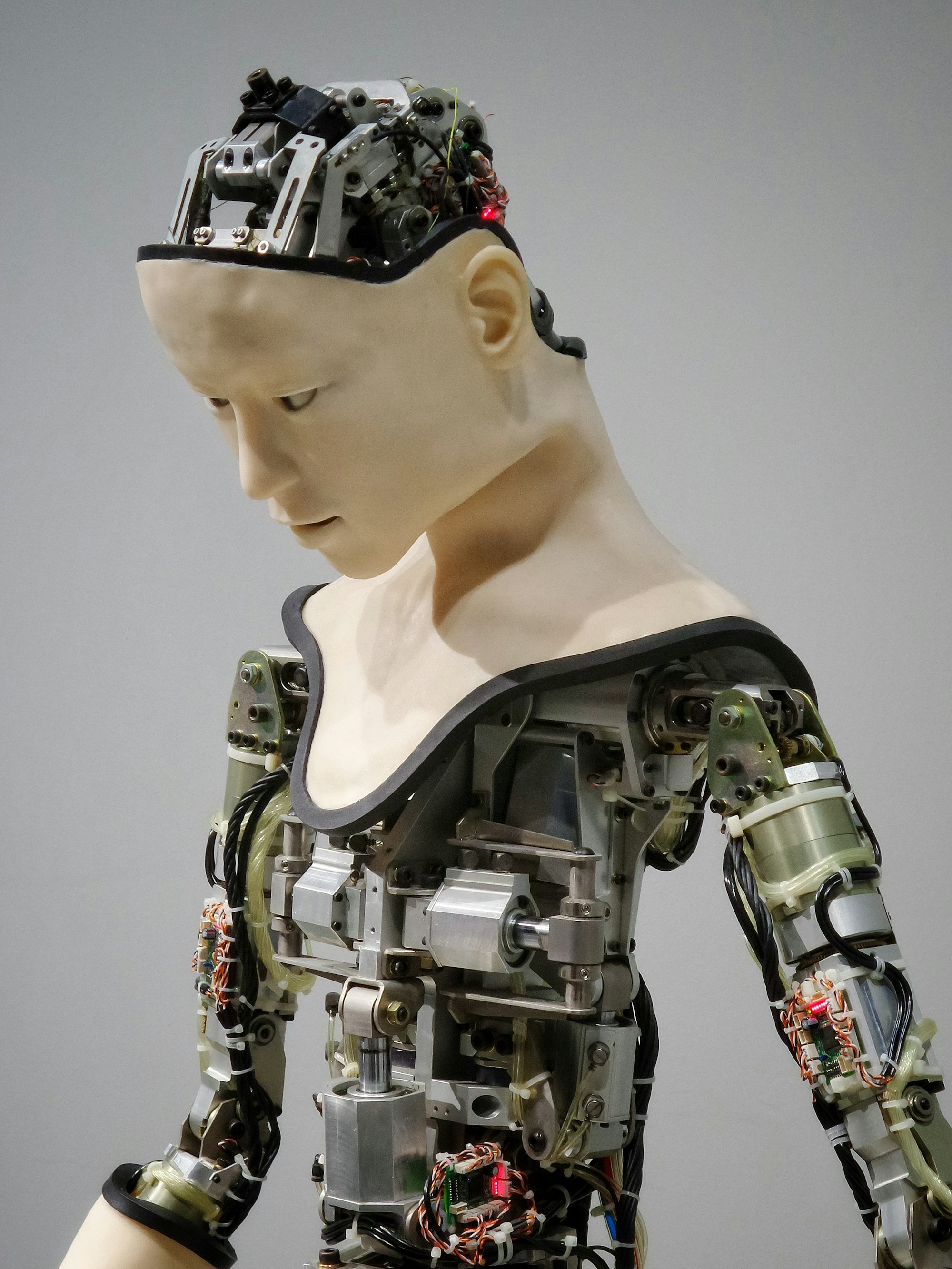
Navigating the Cyber Threat Landscape: The Crucial Role of Security Operations Centers (SOCs) and the Integration of AI and MSSP Services
In an era where cyber threats are increasingly sophisticated and pervasive, establishing a robust defense mechanism is paramount for organizations of all sizes. A Security Operations Center (SOC) acts as the central nervous system of an organization’s cybersecurity framework, providing real-time detection, analysis, and response to threats. However, the effectiveness
![]()
Security Careers HelpSecurity Careers
Navigating the Challenges: Obstacles to SOC Effectiveness
Despite advancements, modern SOCs face several persistent challenges that can hinder their effectiveness:
- Lack of Context: A significant challenge highlighted in the 2023 SANS SOC Survey is the lack of context related to security alerts, making it difficult for analysts to understand the bigger picture and prioritize effectively.
- Staffing Shortages and Skill Gaps: Hiring and retaining qualified security analysts remains a major challenge. There’s a high demand for experienced analysts with the necessary technical and non-technical skills, leading to staff turnover. SOCs often struggle to onboard and train new staff effectively. Hiring managers look for both technical skills like “Information Systems and Network Security” and non-technical skills like “Risk Management”.
- Resource Constraints: Many SOCs operate with limited budgets, staff, and time, making it difficult to implement comprehensive security measures and keep pace with the threat landscape. SOC budget requests often face cuts.
- Alert Overload and Fatigue: SIEMs and other security tools can generate a high volume of alerts, many of which are false positives, leading to alert fatigue and potentially causing analysts to miss critical incidents. Lack of proper correlation between alerts exacerbates this issue.
- Lack of Automation and Orchestration: The insufficient adoption and tuning of automation and orchestration tools limits the efficiency and scalability of SOC operations.
- Visibility Gaps: A lack of enterprise-wide visibility across all IT and OT assets, including cloud environments, hinders the SOC’s ability to detect and respond to threats comprehensively.
- Tool Sprawl and Lack of Integration: Organizations often deploy numerous security tools that are not well-integrated, creating silos of information and complicating analysis.
- Difficulty in Measuring and Demonstrating Value: Quantifying the effectiveness of SOC operations and demonstrating return on investment to upper management can be challenging. [
The Importance of Security Operations Centers (SOCs) in Modern Enterprises
Introduction In today’s digital age, cybersecurity is a top concern for businesses. Security Operations Centers (SOCs) play a pivotal role in safeguarding an organization’s information assets. This article explores the critical functions of SOCs and offers insights into setting up and running an effective SOC. What is a Security Operations
![]()
Security Careers HelpSecurity Careers
The Impact of Structure and Resources on SOC Capabilities
The organizational structure and available resources have a profound impact on a SOC’s capabilities and maturity [our conversation]:
-
Organizational Structure:
- A centralized SOC generally offers better visibility, more consistent processes, and the ability to pool resources and expertise, leading to higher maturity.
- Distributed or federated SOC models can be more tailored to specific business units but may suffer from a lack of centralized oversight and inconsistent capabilities if not managed effectively [our conversation].
- Granting the SOC the authority to do its job, as outlined in a SOC charter, is crucial for its effectiveness.
-
Available Resources:
- Budget and Funding: Adequate funding enables the acquisition of advanced security technologies (SIEM, EDR, XDR, SOAR), the hiring and training of skilled staff, and the implementation of robust processes. Limited budgets can restrict the SOC’s ability to adopt necessary tools and expertise, hindering its maturity.
- Staffing (Quantity and Quality): A sufficient number of well-trained and experienced analysts are essential for effective monitoring, triage, investigation, and incident response. Understaffing and skill gaps directly limit the SOC’s capacity and maturity.
- Technology and Tools: The deployment and proper configuration of relevant security technologies are foundational to SOC operations. Access to advanced tools like SIEM with well-tuned correlation rules, EDR for endpoint visibility, XDR for broader context, and SOAR for automation significantly enhances a SOC’s detection, analysis, and response capabilities. However, the effectiveness of these tools relies on skilled personnel to manage and interpret the data they provide.
- Data Collection and Analysis Capabilities: The ability to collect and effectively analyze security-relevant data from various sources is critical for threat detection and investigation. Mature SOCs invest in technologies and processes to ensure comprehensive data collection and advanced analytics capabilities, including behavioral analysis.
- Threat Intelligence: Access to timely and relevant threat intelligence feeds, platforms, and skilled threat intelligence analysts enhances the SOC’s proactive defense, detection, and response capabilities.
- Processes and Procedures: Well-defined and documented incident response plans, playbooks, and SOPs contribute significantly to the consistency and effectiveness of SOC operations. Resource constraints can lead to underdeveloped or inconsistently applied processes, impacting the SOC’s maturity.
[
Artificial intelligence (AI) is Revolutionizing Cybersecurity Operations
Artificial intelligence (AI) is revolutionizing cybersecurity operations, empowering Chief Information Security Officers (CISOs) to enhance threat detection, automate responses, and future-proof security frameworks. Here’s how forward-thinking CISOs are implementing AI in security departments and Security Operations Centers (SOCs), drawing insights from industry practices and real-world deployments. Strategic Alignment for
![]()
Security Careers HelpSecurity Careers
Building an Effective SOC: Key Considerations
Drawing upon the insights from the sources, building and maintaining an effective SOC requires a strategic approach encompassing:
- Understanding What to Protect and Why: A fundamental first step is to identify and prioritize critical assets, data, and business processes.
- Securing Organizational Authority: Granting the SOC the necessary authority and support from leadership is essential for it to function effectively.
- Developing a SOC Structure Aligned with Organizational Needs: Choosing a SOC structure (centralized, distributed, etc.) that best fits the organization’s size, complexity, and business requirements is crucial.
- Investing in Quality Staff: Hiring passionate and skilled analysts, providing continuous training and career progression opportunities, and fostering a positive work environment are vital for building a strong and resilient SOC team.
- Prioritizing Incident Response: Developing and regularly testing comprehensive incident response plans and playbooks ensures the SOC can effectively handle security incidents.
- Leveraging Actionable Threat Intelligence: Integrating threat intelligence into all aspects of SOC operations, from detection rules to incident response procedures, enhances the SOC’s ability to anticipate and respond to threats effectively.
- Selecting and Collecting the Right Data: Focusing on collecting high-value security data from relevant sources, balancing data volume with analytical value, is essential.
- Leveraging Tools to Support Analyst Workflow: Deploying and properly configuring security tools, including SIEM, EDR, XDR, and SOAR, to automate tasks, correlate data, and provide analysts with the necessary context is critical.
- Fostering Clear Communication and Collaboration: Establishing effective communication channels within the SOC, with stakeholders, and with the broader security community enhances situational awareness and enables collective defense.
- Measuring Performance to Drive Improvement: Implementing a metrics program to track SOC performance, identify areas for improvement, and demonstrate value to stakeholders is essential for continuous enhancement.
- Continuously Expanding SOC Functionality: As the SOC matures, expanding its capabilities to include proactive threat hunting, red teaming, and advanced analysis techniques can further enhance its effectiveness against sophisticated adversaries.
Conclusion: The Ongoing Evolution of Cyber Defense
The Security Operations Center remains the cornerstone of an organization’s cyber defense strategy. Its effectiveness hinges on a synergistic combination of skilled human expertise, advanced technologies, well-defined processes, and actionable threat intelligence. As the cyber threat landscape continues to evolve in complexity and sophistication, SOCs must also adapt and embrace new trends while addressing persistent challenges. The influence of organizational structure and the availability of adequate resources are critical determinants of a SOC’s capabilities and maturity. By strategically investing in the right people, processes, and technologies, organizations can build robust and resilient SOCs capable of effectively safeguarding their digital assets in the face of ever-present cyber threats.