🎧 Related Podcast Episode
Executive Summary
Cyber risk has emerged as a critical threat to the financial sector, driven by the increasing volume, value, and sensitivity of data managed by financial institutions (FIs) and financial market infrastructures (FMIs). The scope and intensity of cyber threats are escalating, with cyberattacks becoming more frequent, sophisticated, and potent. As the financial system’s dependency on complex Information and Communication Technology (ICT) grows, the potential for a systemic cyber incident to compromise financial stability and create negative macroeconomic spillovers is a primary concern for regulators and supervisors.
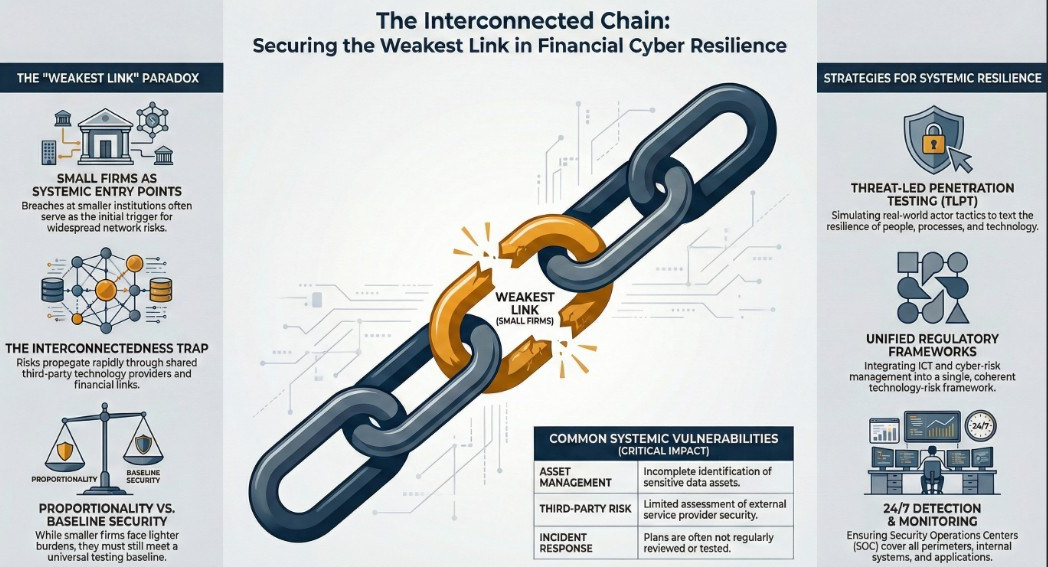
Effective management of this risk requires a forward-looking approach to regulation and supervision. Key opportunities for improvement in regulation include integrating disparate ICT and cyber-risk-management rules into a single, coherent technology-risk-management framework. The most impactful recent developments have centered on formalizing expectations for cybersecurity testing, mandating cyber crisis exercises, and addressing the systemic risks posed by the financial sector’s growing reliance on third-party technology service providers. Bringing these critical providers under a direct oversight framework is a major forthcoming challenge.
In supervision, the most consequential factor for improving the cybersecurity posture of the financial sector is the persistent and thorough presence of the supervisor. Through frequent and inquisitive offsite and onsite engagement, rigorous analysis, and diligent follow-up, supervisors can significantly elevate industry practices.
[
Good Practices in Cyber Risk Regulation and Supervision-compressed
Good Practices in Cyber Risk Regulation and Supervision-compressed.pdf
875 KB
download-circle](/files/Good-Practices-in-Cyber-Risk-Regulation-and-Supervision-compressed.pdf)
Two overarching principles are fundamental to both effective regulation and supervision:
- A Balanced Approach: A blend of principles-based and prescriptive elements is essential. Regulations should focus on desired outcomes and remain technology-agnostic to provide flexibility. Supervision must rely on professional judgment, which is paramount in the dynamic field of cyber risk.
- Proportionality: A one-size-fits-all approach is ineffective. For systemically important and complex entities, the highest standards must be applied rigorously. For smaller, non-systemic institutions, expectations should be adapted to fit their specific risk profiles, while recognizing that in an interconnected system, security is only as strong as its weakest link.
The Evolving Cyber Risk Landscape
Core Concepts
This analysis utilizes definitions from the Financial Stability Board’s (FSB) Cyber Lexicon to ensure clarity and consistency.
- Cyber: Pertains to the interconnected information infrastructure involving interactions among people, processes, data, and information systems. It is not limited to technology but encompasses the human and procedural elements that interact with ICT.
- Cybersecurity: The preservation of confidentiality, integrity, and availability of information and information systems within the cyber medium. It also includes properties like authenticity, accountability, and reliability. Effective cybersecurity requires measures proportional to the risks involved.
- Cyber Incident: A cyber event that jeopardizes the cybersecurity of an information system, violates security policies, or impacts an organization’s normal IT operations. This definition includes unsuccessful attempts and events occurring without malicious intent, such as user error or technology failure.
- Cyber Risk: The combination of the probability of cyber incidents occurring and their potential impact. This broad definition encompasses risks from malicious activity, non-malicious actions, and technology failures.
Evolution of the Threat Landscape
The cyber threat landscape has intensified significantly, with a marked increase in the frequency and cost of incidents, particularly since 2020.
- Incident Frequency: The number of cyberattacks in a single year nearly doubled compared to 2019 levels.
- Financial Impact: Total losses from cyber incidents saw an extraordinary spike of approximately 500% in 2020 compared to 2019. From 2020 to 2023, direct losses reported by the financial sector alone stood at $2.5 billion. Given systemic under-reporting and the fact that indirect losses often exceed direct ones by several multiples, the true total losses are likely much higher.
- Sector Targeting: The financial sector is a primary target, accounting for approximately 20% of all reported cyber incidents over the past two decades, with banks being the most frequent victims.
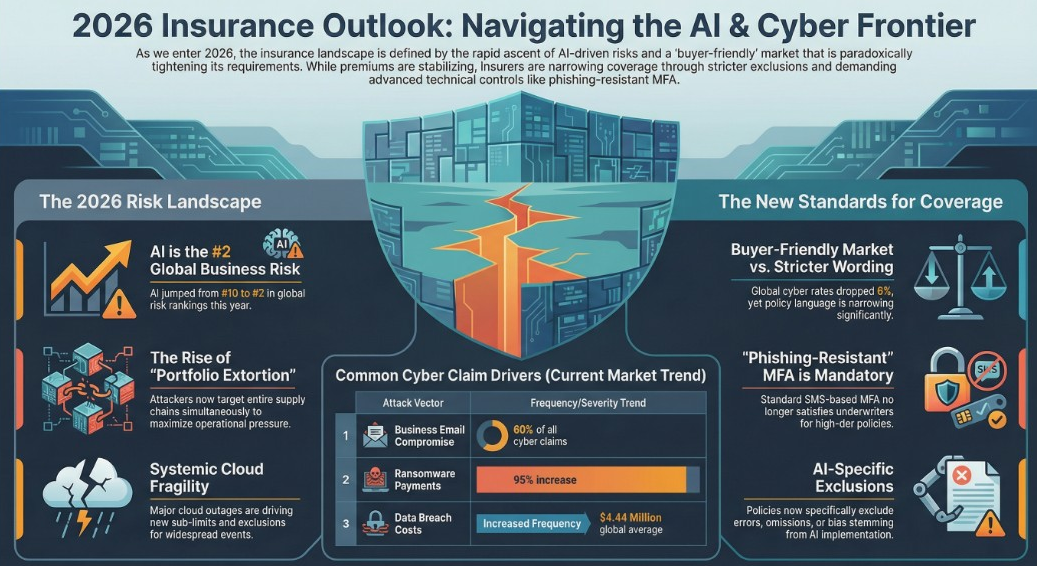
- Driving Factors: This escalation is driven by increasing dependency on ICT, faster financial innovation leading to shorter testing cycles, and geopolitical and economic factors. The adoption of Artificial Intelligence (AI) has fueled next-generation phishing and attack automation, while geopolitical tensions have contributed to attacks on critical infrastructure and an increase in insider threats.
Systemic Importance of Cyber Risk
Cyber risk is a key material risk for the financial sector with the potential for systemic implications that could compromise financial stability. Incidents can propagate through the financial system via three primary channels:
|
Transmission Channel |
Description | |
Loss of Confidence |
A data breach or prolonged service disruption at an FI can erode public trust, triggering liquidity risks (e.g., “cyber runs”) or solvency issues that spill over to connected entities. | |
Lack of Substitutes |
An attack incapacitating a critical and not easily substitutable FMI, such as a real-time gross settlement system or a clearinghouse, could severely disrupt the entire financial system. | |
Interconnectedness |
The impact of an incident can spread rapidly through technological links (e.g., common software vulnerabilities) or financial links (e.g., the interbank market). |
Emerging technologies like AI and quantum computing are poised to accelerate the buildup of cyber risk. AI can be used for both offensive operations (e.g., deepfake-based phishing) and defense, while quantum computing threatens to break classic cryptography, endangering data confidentiality and integrity.
The IMF’s Role in Strengthening Cyber Resilience
Since 2017, the International Monetary Fund (IMF) has implemented a comprehensive work program to assist member countries in strengthening the cyber resilience of their financial systems through surveillance and capacity development.
Financial Sector Assessment Program (FSAP)
The FSAP, a cornerstone of IMF surveillance for jurisdictions with systemically important financial sectors, began formally piloting in-depth cyber risk assessments in 2020.
- Scope: These assessments have primarily focused on the regulation and supervision of cyber risks by banking and FMI authorities, aligning with Pillar 2 (Policy Framework, Oversight, Governance) of the FSAP framework.
- Challenges: Expanding assessments to other pillars, such as macrofinancial risk analysis (Pillar 1), is challenging due to a dearth of reliable data from FIs (who fear reputational damage) and a lack of convergence in incident reporting formats.
- Jurisdictions Assessed: A growing number of jurisdictions have undergone FSAP missions with in-depth cyber risk coverage.
|
Year |
Jurisdictions | |
2020 |
Norway, United States | |
2021 |
United Kingdom | |
2022 |
Mexico, South Africa | |
2023 |
Iceland, Republic of Türkiye, Sweden | |
2024 |
Japan, Luxembourg, Spain | |
2025 |
Canada, Euro Area, France, India, Switzerland |
Technical Assistance (TA)
The IMF provides extensive TA to emerging markets and developing economies, responding to a significant increase in demand. Over the past four years, 108 TA missions have been delivered.
-
Key Areas of Assistance:
- Developing national cyber strategies for the financial sector.
- Drafting regulations on cyber risk, IT, business continuity, and third-party risk.
- Establishing cyber incident reporting frameworks.
- Conducting cyber simulation exercises.
- Building supervisory capacity, including developing supervisory frameworks and manuals.
-
Observations from TA Missions:
- Emerging and developing economies have significant work to do, particularly in building the capacity to effectively supervise adherence to regulations.
- Most lack formal cyber incident reporting frameworks and information-sharing networks.
- Many have yet to conduct cyber simulation exercises or establish dedicated cyber risk supervision units.
Good Practices in Cyber Risk Regulation
The primary objective of cyber-risk-management regulation is to safeguard the confidentiality, integrity, and availability of information and systems within supervised entities.
Regulatory Development and Approach
A structured development process and a balanced regulatory approach are crucial for creating effective and coherent regulations.
- Process: A phased approach—Analyze/Plan, Design, Develop, Consult, and Implement—ensures that regulations solve identified problems without imposing undue burdens.
- Unified Regulation: Strive for a single, unified regulation that encompasses all technology risk areas rather than maintaining separate ICT and cyber risk regulations.
- Principles-Based vs. Prescriptive: An approach that is primarily principles-based is often more beneficial, as it is more future-proof against rapidly evolving threats and technologies. Prescriptive elements should be used exceptionally, based on the maturity of industry practices.
- Key Characteristics: Effective regulations are outcome-driven, technology-agnostic, and allow flexibility in implementation. They should also apply the principle of proportionality, with a baseline for all FIs and tiered requirements for larger, more complex entities.
Key Regulatory Expectations for FIs
The following areas are critical for inclusion in a robust regulatory framework for technology and cyber risk management.
|
Domain |
Key Expectations | |
Governance & Controls |
Board of directors must possess requisite experience, set risk tolerance, and ensure adequate resources. FIs must establish clear policies, manage information assets, maintain a security awareness program, secure an independent cybersecurity budget, and ensure robust internal audits. | |
Risk Management |
Establish a risk management framework with clear risk ownership. Conduct regular risk assessments and treatment, and implement continuous risk monitoring and reporting. A project management framework must integrate security validation at each stage of a project’s lifecycle. | |
ICT Service Management |
Implement a comprehensive framework covering asset management, patch management, change management, incident management, and identity and access management (IAM), applying principles like “need-to-know” and “least privilege.” Data center (DC) security and physical controls are also critical. | |
Cybersecurity Operations |
Establish a system for threat intelligence collection and analysis. Implement a security operations center (or equivalent function) for 24/7 cyber event monitoring and detection. Develop and test a cyber incident response and management plan, with mandatory reporting to supervisors. | |
Response & Recovery |
Institute a formal business continuity management process. Maintain a comprehensive backup regimen, including immutable backups to counter ransomware, with periodic test restorations. | |
Testing & Assurance |
Conduct regular vulnerability scanning and penetration testing, especially for external-facing services. Perform regular cyber exercises (e.g., tabletop simulations). Establish a process to track and remediate all identified issues. Ensure independent ICT and cyber risk audits are performed. | |
Third-Party Management |
FIs and their boards remain fully accountable for outsourced functions. A risk assessment and due diligence review must precede any contract with a technology service provider (TSP), and contracts must reserve the right for the regulator to audit the TSP. |
Good Practices in Cyber Risk Supervision
Effective supervision complements strong regulation and is paramount for improving the cybersecurity posture of the financial sector. Core supervisory processes include regulation development, offsite supervision, onsite examinations, and monitoring of cybersecurity testing.
Governance and Staffing
- Supervisory Governance: Boards of supervisory authorities should set the agenda for cybersecurity supervision. Responsibilities and accountability must be clearly assigned. It is essential to integrate cyber risk assessments into the overall enterprise-wide risk management picture.
- Staffing and Resources: The scarcity of skilled resources is a universal challenge. Good practices include creating specialized cyber risk units, leveraging expertise from other departments (IT, payments, audit), and using external auditors as a stopgap measure. Background checks on supervisors are mandatory.
- Learning and Development: Cybersecurity is a dynamic field requiring continuous learning. Supervisors need ongoing training, professional certifications (e.g., CISA, CISSP), and participation in workshops and knowledge-sharing forums.
Proportionality in Supervision
Proportionality involves calibrating supervisory intensity and regulatory requirements to an institution’s size, complexity, systemic importance, and risk profile.
-
Supervisory Practice: The frequency, scope, and depth of onsite examinations can be scaled up for the largest, most systemic FIs and for those with aggressive digital business models.
-
Control Maturity: While control objectives (e.g., IAM) remain the same for all institutions, larger FIs are expected to have more mature control procedures, such as dedicated systems and automation.
-
Examples:
- Penetration Testing: A baseline expectation for all FIs to conduct testing, with more stringent requirements (e.g., annual, independent third-party) for systemic FIs.
- CISO Function: Smaller FIs may have more flexibility in how they structure the Chief Information Security Officer role compared to larger institutions, which are expected to ensure greater independence from first-line technology functions.
Offsite and Onsite Supervision
|
Supervisory Method |
Overview & Good Practices | |
Offsite Supervision |
Enables continuous monitoring of an FI’s cybersecurity posture. Good practices include:
- Developing an annual offsite supervision plan.
- Establishing minimum reporting requirements for both qualitative data (strategies, policies, audit plans) and quantitative metrics (incident numbers, system uptime).
- Implementing a robust ad hoc cyber incident reporting system with 24/7 monitoring and follow-up.
- Conducting risk analysis of both idiosyncratic and systemic risks, including through tools like cyber mapping.
- Using notifications and permissions to stay informed of material changes like new outsourcing arrangements.
Onsite Supervision |
Provides stronger assurance on the quality of cyber risk management through direct verification. Good practices include:
- Thorough planning, including a pre-examination information request and review of all available materials.
- Adopting an auditor’s mindset of professional skepticism (“trust but verify”) and using evidence-based validation and sample testing.
- Meeting with the board of directors and representatives from all three lines of defense (independently where necessary).
- Conducting an exit meeting to communicate preliminary findings.
- Issuing a formal report with ranked findings (e.g., requirements, recommendations) and diligently following up on the FI’s remediation plan.
An example of a structured supervisory intervention is the Australian Prudential Regulation Authority’s (APRA) CPS 234 “Tripartite” review, which required all regulated entities to appoint an independent auditor to assess their compliance with APRA’s information security standard, driving significant industry-wide improvements.
Advanced Supervisory Tools
-
Thematic Reviews: These are deep-dive reviews on a single topic (e.g., third-party risk management, business continuity) across multiple FIs. They are an incisive tool for understanding sector-wide practices, identifying common gaps, and informing future supervisory priorities.
-
Monitoring Cybersecurity Testing: Supervisors are increasingly overseeing advanced testing like Threat-Led Penetration Testing (TLPT). In a TLPT, a “Red Team” simulates real-world attackers based on targeted threat intelligence to test an entity’s defenses (“Blue Team”).
- Supervisor’s Role: The supervisor’s role is to oversee the entire process, not conduct the test. They set the framework, assess results, and ensure remediation.
- Good Practice: Supervisors should avoid collecting highly technical details of vulnerabilities and exploits from test reports to minimize their own attractiveness as a target. The focus should be on ensuring the weakness is understood at a business risk level and that a robust remediation plan is executed and tracked.
Cyber Simulation Exercises
Cyber simulation exercises (also called “war games” or “tabletop exercises”) are a powerful tool for strengthening cybersecurity by allowing participants to practice response strategies in a controlled environment. Authorities should take a leading role in driving sector-wide exercises.
Benefits of Cyber Simulations
|
Benefit Category |
Examples | |
Improved Response |
Faster decision-making under pressure and better coordination between IT, security, legal, and communications teams. | |
Gap Identification |
Exposes vulnerabilities in security infrastructure, policies, and procedures; tests the effectiveness of backup and recovery plans. | |
Enhanced Preparedness |
Provides practical training for employees in both technical and non-technical roles. | |
Better Risk Management |
Allows teams to evaluate the potential impact of different attack vectors (e.g., ransomware, insider threats) and prioritize defenses. | |
Stronger Collaboration |
Refines internal and cross-departmental communication strategies. | |
Continuous Improvement |
Post-exercise debriefings (“hotwash”) provide actionable insights that feed into an improvement plan. |
Good Practices for Exercise Programs
An effective cyber simulation program should be structured and cyclical. Key components include:
- Stakeholder Engagement: Secure support from key leaders to guide the program and set priorities.
- Multiyear Preparedness Priorities: Base the program on risk assessments and a multiyear plan that allows for tracking long-term improvements.
- Improvement Planning: Use after-action reports to generate measurable corrective actions with clear owners and deadlines.
- Individual Exercise Process: Follow a structured approach for each exercise, encompassing design, development, conduct, and assessment to ensure objectives are met and lessons are learned.
Monitoring and Mitigating System-wide Cyber Risk
Operational resilience requires focused operational preparedness—an alignment of people, processes, and technology. Supervisors must adopt a holistic view, understanding the entire delivery chain of digital financial products to identify dependencies and systemic vulnerabilities.
Key Pillars for Systemic Resilience
- Continuous Surveillance: Monitor cybersecurity preparedness across all industry participants.
- Incident Reporting: Implement a comprehensive framework to capture granular data for timely detection and response.
- Dependency Mapping: Map interconnections between institutions and, critically, with third-party service providers to identify concentration risks and single points of failure.
- Financial Stability Analysis: Incorporate severe but plausible cyberattack scenarios into stress testing and contingency planning.
- Sector-Wide Strategy: Establish a clear national cybersecurity strategy for the financial sector.
- Leadership & Culture: Top management at supervisory agencies must set the agenda and promote a culture of cybersecurity awareness.
- International Collaboration: Cooperate on regulatory convergence, threat intelligence sharing, and emerging threat analysis.
Financial Market Infrastructures (FMIs)
The safe operation of systemically important FMIs is essential for financial stability. Oversight of FMIs is becoming more intensive, adopting practices from prudential supervision. The IMF applies the CPMI-IOSCO Guidance on Cyber Resilience of FMIs in its assessments. Key recommendations for FMIs and their overseers include:
Recommendations to Strengthen FMI Cyber Resilience:
- Governance: Develop clear cyber strategies, ensure board members have cyber expertise, and give oversight divisions independence and resources.
- Identification: Maintain a database of third-party providers to identify concentration risks.
- Response and Recovery: Upgrade business continuity plans with cyber-specific, extreme-but-plausible scenarios that are regularly tested.
- Testing: Conduct regular cyber exercises with FMI participants and links, expedite penetration testing, and perform quantitative cyber stress tests.
- Situational Awareness: Establish formal information-sharing arrangements between authorities, cybersecurity agencies, and FMI participants.
Recommendations to Strengthen FMI Supervision and Oversight:
- Approach: Strengthen the oversight approach for FMI cyber resilience by increasing the frequency and depth of both offsite and onsite supervision.
- Powers and Resources: Grant FMI authorities clear regulatory powers and enhance the skills and expertise of FMI overseers.
- Cooperation: Enhance coordination between authorities that share responsibility for commonly overseen FMIs.