Government Agency Warns of “Likely to Very Likely” Threat from Tech Products Connected to China
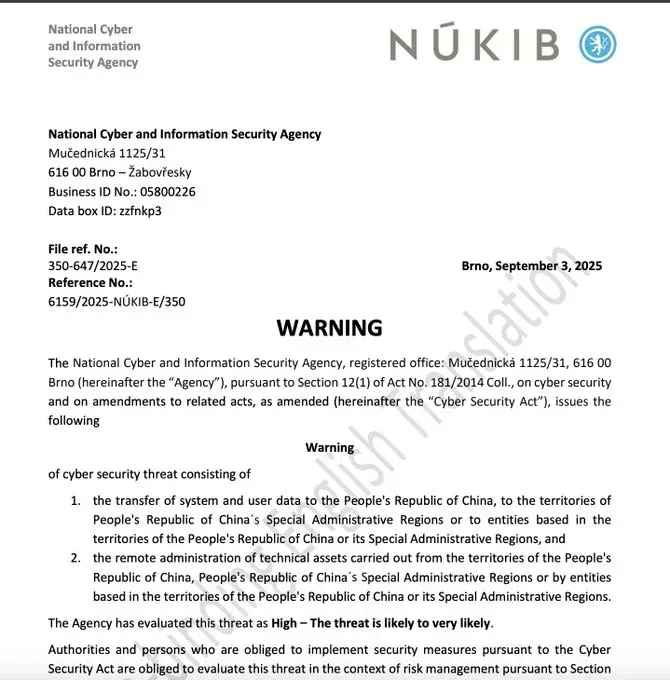
The Czech Republic’s National Cyber and Information Security Agency (NÚKIB) has issued its most serious cybersecurity warning to date, alerting organizations and the public to “HIGH” level threats from the transfer of system and user data to China and remote administration of technical assets from Chinese territories. The September 3, 2025 warning specifically targets smartphones, cloud services, IP cameras, smart meters, and photovoltaic inverters that send data to or are controlled from China.
Bottom Line: Czech cybersecurity experts conclude that Chinese laws give the government unlimited access to data stored in China, making any technology that transfers information there or allows remote control from China a significant security risk—especially for critical infrastructure in telecommunications and energy.
[
EN_2025-09-03_warning
EN_2025-09-03_warning.pdf
493 KB
download-circle](/files/EN_2025-09-03_warning.pdf)
The Core Security Threat
NÚKIB has assessed the threat level as “High – The threat is likely to very likely”, representing a 3 out of 4 probability rating on their threat scale. The warning encompasses two primary concerns:
- Data Transfer Risk: System and user data being sent to the People’s Republic of China, its Special Administrative Regions (Hong Kong and Macau), or entities based in these territories
- Remote Administration Risk: Technical assets being remotely controlled from Chinese territories or by China-based entities
The agency emphasizes that “mere control of the devices, given their complexity, is insufficient. Therefore, users must also consider non-technical factors of the products, such as trust in the manufacturer and the legal or political environment in which the manufacturer operates.”
China’s Legal Framework: The Root of the Problem
The warning is grounded in an extensive analysis of Chinese legislation that, according to NÚKIB, creates an environment where the government can compel companies to cooperate with intelligence services. Key laws include:
National Security and Intelligence Laws
- National Security Law (2015): Imposes a general duty on all Chinese citizens and organizations to provide assistance to state authorities in matters of state security
- National Intelligence Law (2017): Article 7 stipulates that “every citizen and organization must support national intelligence activities, provide cooperation and collaboration”
- Counter-Espionage Law (2014, amended 2023): Imposes duty to provide cooperation and information on foreign clients, with broad definitions that can apply to almost any activity
Corporate Control Mechanisms
- Company Law (2013): Requires Communist Party organizations to be established in companies, allowing the CPC to effectively influence private company operations
- Cybersecurity Law (2016): Requires network operators to store select data within China and allows Chinese authorities to conduct spot-checks on company network operations
Critical Infrastructure at Risk
The warning particularly highlights risks to sectors regulated under Czech cybersecurity law, including:
- Telecommunications networks
- Energy systems (including smart grids and photovoltaic installations)
- Transportation infrastructure
- Healthcare systems
- Public administration networks
NÚKIB warns that “technology solution providers can significantly influence the operation of critical infrastructure and/or access important data, making trust in the reliability of the provider absolutely crucial”.
Real-World Attack Evidence
The warning isn’t just theoretical. NÚKIB points to concrete evidence of Chinese cyber operations targeting Czech infrastructure:
- APT31 Attacks: In May 2025, the Czech government publicly attributed cyberattacks on the Ministry of Foreign Affairs to APT31, a group associated with the Chinese Ministry of State Security, which had been targeting Czech networks since at least 2022
- Coordinated Global Campaign: International intelligence agencies have documented Chinese state-sponsored actors compromising networks worldwide to feed a global espionage system, with operations linked to multiple China-based entities providing cyber services to intelligence services
European Response: A Growing Trend
The Czech warning aligns with increasing European concerns about Chinese technology risks:
GDPR Enforcement Actions
European privacy advocacy group noyb filed GDPR complaints in January 2025 against six major Chinese tech companies—TikTok, AliExpress, SHEIN, Temu, WeChat, and Xiaomi—for unlawfully transferring European personal data to China. The complaints argue that “Given that China is an authoritarian surveillance state, it is crystal clear that China doesn’t offer the same level of data protection as the EU”.
Telecommunications Infrastructure Concerns
Despite official EU guidance encouraging restrictions on “high-risk vendors,” Chinese equipment still supplies more than 50% of 5G infrastructure in 31 European countries as of 2022, with Germany particularly dependent at 59% Chinese 5G equipment.
Specific Technology Risks
NÚKIB’s analysis extends beyond traditional IT infrastructure to include:
Consumer Devices
- Smartphones and smartwatches: Risk of location tracking, communication monitoring, and audiovisual recording
- Electric vehicles: Potential for movement tracking and data collection
- Smart home devices: Including IP cameras and smart meters
Industrial Equipment
- Photovoltaic inverters: Critical to renewable energy infrastructure
- Network equipment: Routers, switches, and telecommunications gear
- Cloud services: Data storage and processing platforms
Recommendations and Requirements
The warning creates legal obligations for organizations covered by Czech cybersecurity law, who must:
- Evaluate the threat in their risk management frameworks
- Implement adequate security measures to address identified risks
- Consider supplier trustworthiness when selecting technology providers
For the general public, NÚKIB recommends:
- Carefully assessing Chinese technology and services before use
- Considering what type of information is shared with such services
- For high-profile individuals, considering complete avoidance of affected technologies
Global Context: Part of a Broader Pattern
The Czech warning reflects growing international recognition of Chinese cyber threats:
- US Intelligence Assessment: The 2025 Annual Threat Assessment highlights persistent cyber threats from China, with actors like Volt Typhoon and Salt Typhoon extending beyond traditional espionage to target critical infrastructure
- Five Eyes Alliance: International intelligence alliances have issued joint advisories describing Chinese APT group tactics and their global espionage activities
- European Parliament Resolution: A January 2024 resolution identified Chinese influence on European critical infrastructure as a security threat, noting that data transfers to Chinese clouds are “incompatible with European principles of privacy protection and security”
The Bigger Picture: Trust in the Digital Age
The Czech warning represents more than a technical cybersecurity alert—it’s a fundamental challenge to how democracies evaluate technology in an interconnected world. As NÚKIB Director Lukáš Kintr noted, the issue extends beyond mere technical specifications to questions of legal frameworks, political systems, and international trust.
The warning signals that the era of technology selection based solely on price and performance may be ending, replaced by a more complex calculus that includes geopolitical considerations and legal jurisdiction risks. For organizations worldwide, this raises difficult questions about balancing cost, functionality, and security in an increasingly multipolar technological landscape.
As cyber threats continue to evolve and state-sponsored espionage becomes more sophisticated, the Czech Republic’s decisive action may serve as a model for other nations grappling with similar security challenges in the digital age.